Zero Trust in multi-cloud means every access to cloud resources is explicitly verified, least-privilege, and continuously monitored, regardless of network location. For Brazilian enterprises using AWS, Azure, GCP and private clouds, the priority is a unified identity-centric policy model, strong segmentation, provider-agnostic controls, and safe, incremental rollout to avoid outages and configuration drift.
Operational checklist for Zero Trust rollout
- Define critical business flows across all clouds before touching network rules.
- Centralize identity and strong authentication as the primary control plane.
- Standardize policy language and tagging across providers and environments.
- Start with visibility and read-only mode; then enforce in small scopes.
- Continuously test, monitor and tune policies based on real traffic.
- Map Zero Trust controls to compliance and cost constraints from day one.
Assessing multi-cloud attack surface and identity landscape
Zero Trust architecture is most valuable when you already operate workloads across at least two cloud providers or a hybrid environment. It is not ideal to start a deep Zero Trust program while basic tasks such as inventory, backups, or incident response are still immature or undocumented.
This section focuses on how to understand your current arquitetura zero trust multi cloud readiness, including identities, networks and exposed services.
| Step / activity | Primary owner | Decision checkpoint (Yes/No) | Minimum acceptance criteria before rollout |
|---|---|---|---|
| Build inventory of cloud accounts, subscriptions and projects (AWS, Azure, GCP, private cloud) | Cloud platform team | Yes: all in CMDB; No: discovery still in progress | Every account uniquely identified and mapped to a business owner |
| Catalogue internet-exposed endpoints and services | Security operations | Yes: single list available; No: multiple partial spreadsheets | List of public IPs, DNS names, WAF frontends, VPN gateways, and APIs |
| Map identity providers and trust relationships (IdPs, directories, SSO) | Identity & Access Management (IAM) | Yes: clear diagram; No: ad-hoc trust and shadow IdPs | Documented list of IdPs used by employees, partners, workloads and devices |
| Identify critical business applications and data flows | Application owners | Yes: prioritised list; No: only technical inventory | Top mission-critical apps tagged and linked to underlying cloud resources |
| Assess current network segmentation and security groups | Network/security engineering | Yes: segmentation aligned to tiers; No: flat VPC/VNet designs | Baseline understanding of how workloads communicate within and across clouds |
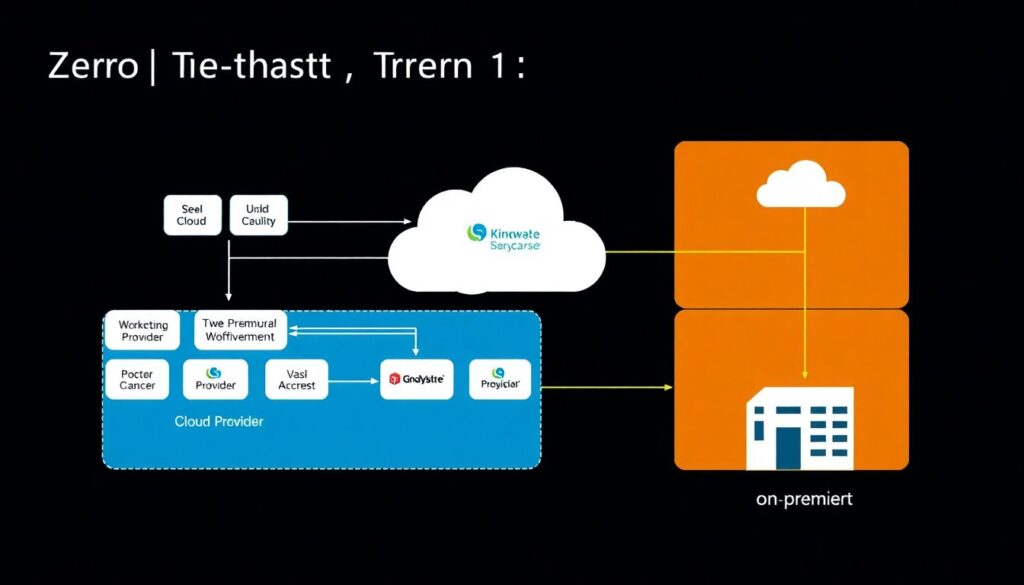
Conceptual diagram placeholder: one page showing all clouds, identity providers, and internet exposure points, with arrows indicating main data flows.
Designing a unified Zero Trust policy model across providers
This part describes what you need ready before enforcing segurança zero trust em ambiente multicloud: tools, access, and a common language for policies so that AWS, Azure, GCP and on-premise rules remain consistent and auditable.
| Design element | Owner | Decision checkpoint (Yes/No) | Minimum acceptance criteria |
|---|---|---|---|
| Common identity source and strong authentication (SSO, MFA) | IAM team | Yes: single SSO per persona; No: multiple logins per user | All workforce accounts integrated into one SSO with MFA enforced for admin access |
| Standard tagging model for workloads, data sensitivity and environments | Cloud governance | Yes: tag policy in place; No: inconsistent tags | Mandatory tags defined and validated during provisioning pipelines |
| Provider mapping for access policies (e.g., AWS SCPs, Azure Policy, GCP Org Policies) | Cloud security architects | Yes: mapping document; No: per-team policies only | For each global rule, there is a documented implementation for each cloud |
| Choice of policy engine (native, third-party or both) | Security architecture board | Yes: approved architecture; No: competing tools | Single reference design for how policies are authored, tested and deployed |
| Baseline access models for users, services and admins | Security and HR/process owners | Yes: role catalog; No: custom roles per app only | Role catalogue for main personas with least-privilege guidelines and examples |
When selecting soluções zero trust para multi cloud enterprise, make sure the chosen products integrate natively with your IdP, support your main cloud providers, and expose policies as code so you can test and version-control every change safely.
Conceptual diagram placeholder: layered view with identity at the center and policy fabric spanning AWS, Azure, GCP, and private data center.
Identity, device posture and workload attestation strategies
Before implementing these strategies, use the short preparation checklist below to avoid user impact and unsafe configurations.
- Confirm that emergency break-glass accounts exist and are stored securely offline.
- Test MFA flows with a small pilot group per business unit.
- Validate endpoint management coverage for corporate devices.
- Document which workloads can safely enforce mTLS and which need migration.
- Align helpdesk playbooks for locked-out users or failed device checks.
-
Unify human identity and authentication.
Start by consolidating workforce identities into a single IdP that supports SSO and strong MFA.- Integrate cloud consoles, critical SaaS, and VPNs into the same sign-in experience.
- Enforce conditional access for high-risk actions such as privilege escalation.
-
Classify identities and define risk-based access.
Group users into personas (e.g., developer, operator, contractor) and assign risk levels.- Use stricter controls for admins and third parties (MFA, device compliance, limited time-bound access).
- Document which apps each persona truly needs to reduce over-permissioning.
-
Deploy device posture checks for managed endpoints.
Integrate your endpoint management and EDR tools with access policies where possible.- Require compliant, encrypted and monitored devices before granting access to sensitive apps.
- Allow browser-based or VDI access for unmanaged or BYOD devices, isolating them from internal networks.
-
Implement workload identity and mutual TLS.
Replace IP-based trust between services with strong workload identities.- Use cloud-native mechanisms like AWS IAM roles, Azure managed identities and GCP service accounts consistently.
- Add mTLS between services using service mesh or gateways, starting with non-critical paths.
-
Introduce attestation and policy-based authorization.
For high-value workloads, verify that code, configuration and runtime context match expected states.- Leverage CI/CD attestations or image signing to ensure only verified workloads receive credentials.
- Use centralized policy engines for fine-grained authorization decisions per request.
-
Continuously review access and adjust.
Schedule regular access recertifications and posture reviews.- Automate removal of unused privileges and stale service accounts.
- Feed results from incident reviews back into identity and posture policies.
| Step | Owner | Decision checkpoint (Yes/No) | Safe minimum criteria before expanding |
|---|---|---|---|
| Consolidate to one workforce IdP with MFA | IAM team | Yes: >90% apps integrated; No: multiple primary IdPs | MFA enabled for all admins, documented fallback for outages |
| Roll out device posture checks | Endpoint and security teams | Yes: pilot stable; No: frequent false positives | Helpdesk trained, clear user communication and self-service instructions available |
| Enable workload identities and mTLS in one domain | Platform and app teams | Yes: observability ready; No: blind to service errors | Rollback plan tested, SLOs monitored before extending to critical apps |
Conceptual diagram placeholder: identity layers for users, devices and workloads, all feeding into a central policy decision point.
Secure connectivity: microsegmentation and policy enforcement points
This section provides a practical checklist to validate microsegmentation and enforcement points across clouds and data centers for an effective implementação de zero trust em nuvem pública e privada.
- Each environment (prod, test, dev) has separate network segments or projects with clear boundaries.
- Security groups, NSGs and firewall rules block all traffic by default and only allow explicit, documented flows.
- East-west traffic between workloads is enforced by identity or tags, not by IP ranges alone.
- Access from the internet terminates in controlled entry points: WAF, reverse proxies or Zero Trust Network Access (ZTNA) gateways.
- VPNs and private connectivity links are restricted to a small set of entry points with hardened configurations.
- Third-party vendor access is time-bound, monitored and never directly exposed to production subnets.
- Policy changes go through code review and automated validation, not manual console edits.
- Test environments used for experiments cannot reach production databases or message queues.
- Network logs (flow logs, firewall logs, proxy logs) are centrally collected and searchable.
- Controls are tested using safe synthetic traffic and change windows, with a rollback plan.
| Connectivity control | Owner | Decision checkpoint (Yes/No) | Minimum safe state |
|---|---|---|---|
| Microsegmentation design per environment and tier | Network architecture | Yes: documented; No: tribal knowledge only | Diagrams and rulesets stored in version control and accessible to security |
| Unified secure access entry points (ZTNA, WAF, VPN) | Security engineering | Yes: central access pattern; No: many custom paths | All remote user access forced through a small set of hardened entry services |
| Change management for network policies as code | Cloud platform | Yes: CI/CD-based; No: console-driven | All critical rules managed via code with automated tests before apply |
Conceptual diagram placeholder: segmented network view with policy enforcement points marked at user access, north-south and east-west paths.
Telemetry, continuous validation and automated response workflows
Many Zero Trust projects in Brazil struggle not because of missing tools, but due to recurring mistakes with telemetry and response. The list below describes common traps to avoid when pursuing melhores práticas zero trust cloud híbrida.
- Collecting logs from only one cloud provider, leaving others and on-premise blind to investigation.
- Forwarding huge volumes of raw logs without basic normalization, making detection rules fragile and costly.
- Not correlating identity events (logons, MFA, role changes) with network and workload activity.
- Relying solely on vendor default detections without adapting them to your specific environment and threats.
- Lacking clear thresholds for automated responses, which leads to either no action or disruptive false positives.
- Building complex SOAR playbooks before stabilizing a handful of simple, high-value automations.
- Ignoring feedback from incident post-mortems when tuning Zero Trust policies.
- Not simulating attacks or misuses (e.g., over-privileged tokens, lateral movement) to validate your controls.
- Forgetting to involve application owners when creating alerts that will page their teams.
- Skipping basic health checks for telemetry pipelines, causing silent gaps in visibility.
| Telemetry / response element | Owner | Decision checkpoint (Yes/No) | Minimum safe operational baseline |
|---|---|---|---|
| Central log aggregation across all clouds and data centers | Security operations | Yes: multi-source; No: per-cloud silos | Identity, network and critical workload logs reliably ingested into a central platform |
| High-confidence automated responses for a few priority scenarios | Blue team / SOC | Yes: tested playbooks; No: manual only | At least account lockout for clear compromise and key network blocks for known malicious IPs |
| Regular validation exercises (tabletop and technical simulations) | Security leadership | Yes: recurring; No: ad-hoc only | Exercises at agreed intervals, with documented findings feeding back into policies and tooling |
Conceptual diagram placeholder: data flow from cloud providers into a central analytics and response platform, with feedback loops to policy engines.
Governance, compliance mapping and cost-risk tradeoffs
Not every environment needs the same level of Zero Trust rigor. Sometimes, simpler alternatives are more appropriate, depending on regulatory, operational and budget constraints.
-
Hardened perimeter with enhanced monitoring.
Suitable for legacy systems that cannot support fine-grained identity, device or workload controls. Focus on strong perimeter firewalls, VPN hygiene, patching and extra monitoring, while planning a long-term modernization path. -
Single-cloud Zero Trust baseline first.
For organizations early in cloud adoption, start with a strong design in one provider, then extend patterns to others as your segurança zero trust em ambiente multicloud maturity grows. -
Managed Zero Trust services.
When internal skills are scarce, consider managed ZTNA, identity and security operations offerings. This can be a good bridge, especially for soluções zero trust para multi cloud enterprise that are complex to operate in-house. -
Data-centric controls and tokenization.
In some scenarios, focusing on encrypting and tokenizing sensitive data, along with strong key management, can deliver most of the risk reduction even when network and identity controls are still maturing.
| Governance choice | Primary driver | Decision checkpoint (Yes/No) | When this option is appropriate |
|---|---|---|---|
| Full multi-cloud Zero Trust rollout | High regulatory and business impact | Yes: strong platform team; No: limited expertise | Multiple regulated workloads across clouds with executive support and budget |
| Single-cloud baseline then expansion | Operational simplicity first | Yes: one dominant cloud; No: equal mix | Most critical apps live in one provider and others are still exploratory |
| Managed Zero Trust services | Skill and capacity constraints | Yes: small security team; No: strong internal capability | Teams need predictable service levels and faster time-to-value |
Conceptual diagram placeholder: decision tree connecting business drivers, compliance requirements and Zero Trust architecture depth across clouds.
Concise answers to recurring implementation concerns
How do I start Zero Trust without breaking existing connectivity?
Begin in monitor-only mode: collect identity, network and application telemetry, simulate policies, and test with non-critical workloads. Gradually move small segments to enforcement with clear rollback plans and change windows.
Is multi-cloud Zero Trust realistic for a mid-size Brazilian enterprise?
Yes, but only with a focused scope and strong governance. Start with the most important applications and one or two control planes, like identity and secure access, then grow coverage instead of trying to protect everything at once.
Which teams must be involved from the beginning?
At minimum, involve security, cloud platform, IAM, networking, and representatives from key application teams. Early alignment on responsibilities, escalation paths and change management avoids friction and unsafe shortcuts.
Do I need a service mesh to implement Zero Trust?
No. A service mesh can help with mTLS and fine-grained policies, but you can start with cloud-native controls, gateways and identity-based policies. Introduce mesh where it adds clear value and your teams can operate it safely.
How do I handle legacy systems that cannot support strong identity?
Place them behind proxies or gateways that perform modern authentication and authorization. Restrict access to narrow network segments, monitor closely, and plan gradual replacement or refactoring.
How can I measure progress of my Zero Trust program?
Track coverage metrics such as percentage of critical apps behind ZTNA, MFA adoption for admins, workloads using strong identities, and policy-as-code usage. Combine them with incident trends and audit findings to adjust priorities.
What if a cloud provider feature is missing for my design?
Revisit your requirements and see whether a provider-agnostic control or architectural change can achieve the goal. Avoid heavy custom workarounds that will be hard to maintain across multiple clouds.
