Categoria: Notícias
-

Practical hardening guide for containers and kubernetes to reduce cloud attack surface
Hardening containers and Kubernetes in the cloud means shrinking the attack surface with repeatable controls: minimal images, strict access, locked‑down runtime, segmented networking, and solid logging. Start by standardizing baselines, scanning images, enforcing least privilege, and validating everything with automated policies, so segurança em containers kubernetes na nuvem becomes measurable, not aspirational. Core hardening goals…
-

Cloud cybersecurity trends with Ai and confidential computing shaping the Sase future
Cloud-security trends for the next years will center on AI-native defenses, SASE convergence, confidential computing, deep zero-trust, automated compliance, and preparation for post-quantum threats. For Brazilian organizations, strengthening segurança em cloud para empresas means combining these capabilities into pragmatic architectures, supported by soluções de cibersegurança em nuvem and, when needed, serviços gerenciados de segurança em…
-

Cloud configuration errors that cause data leaks and how to prevent them
Configuration errors in cloud environments usually leak data through overly broad identity permissions, public object storage, exposed endpoints, weak API protection, missing encryption, and excessive logging retention. To avoid them, use least privilege, default-deny networking, automated misconfiguration scanners, strong key management, and clearly tested rollback plans before touching production. Immediate Risk Indicators and Priority Fixes…
-

Cloud monitoring and logging for incident detection: architectures and best practices
Cloud monitoring and logging for incident detection means collecting metrics, logs and traces from all your cloud workloads into a resilient, searchable and alert-enabled stack. You design an observability architecture, standardize telemetry, implement safe pipelines, and tune alert rules so that real incidents are detected fast without flooding teams with noise. Prioritized detection objectives and…
-

Cnapp tools comparison: best cloud-native application protection platform for large enterprises
For large Brazilian enterprises, a CNAPP comparison should focus on depth of cloud-native coverage, quality of risk prioritisation, integration with your existing AWS/Azure/GCP stacks, and realistic operating cost. Ignore vendor hype and score each candidate against concrete security outcomes, deployment complexity, and how it fits your current teams and processes. Essential Comparison Criteria for CNAPP…
-

Cloud key and secret management with Kms, Hsm and vaults: best practices
Cloud key and secret management in Brazil usually means combining a managed KMS for most keys, HSM only for the highest‑risk material, and a secrets vault for application credentials. Start with cloud‑native services, enforce least privilege, automate rotation, and standardize patterns across AWS, Azure and GCP to keep operations simple and auditable. Essentials: KMS, HSM…
-
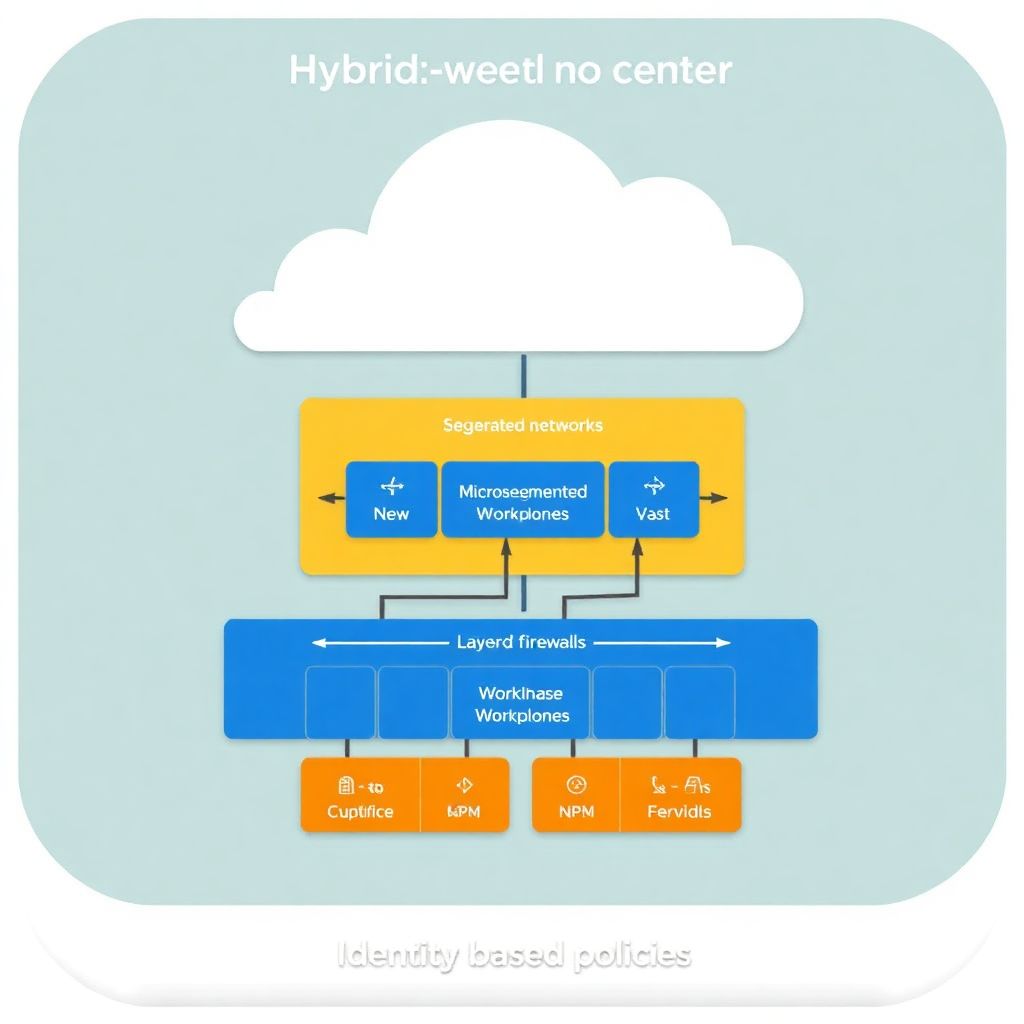
Segmentation and microsegmentation strategies for hybrid cloud networks
Hybrid cloud network segmentation and microsegmentation start with mapping workloads and trust boundaries, then designing layered controls across on‑prem and cloud. Use security groups, firewalls, and identity‑aware policies to isolate tiers, apply least privilege, and enforce Zero Trust consistently. Validate with logging, testing, and a safe, phased rollout to reduce disruption. Critical Implementation Milestones Document…
-

Practical hardening guide for accounts and identities in Aws, azure and Gcp
Hardening accounts and identities in AWS, Azure and GCP means eliminating standing admin access, enforcing strong authentication, segmenting tenants and projects, and continuously monitoring identity activity. Use organization-level guardrails, least privilege roles, secure MFA, managed secrets and well-tested incident playbooks tuned to the Brazilian context of segurança em nuvem aws azure gcp. Executive checklist: high-impact…
-

Siem and Soar cloud integration for faster incident response
To integrate SIEM and SOAR with AWS, Azure and GCP safely, start with a clear scope, use native cloud logging services, standardize data formats, and deploy a small pilot before scaling. Prioritize identity events, internet‑facing workloads and high‑value data. Use least‑privilege access, regional data controls and regular playbook testing. Core integration objectives and outcomes Achieve…
-

Sensitive data protection in cloud using encryption, tokenization and masking
For proteção de dados sensíveis na nuvem in Brazilian cloud environments, combine three layers: native at-rest and in‑transit encryption from your provider, application-level encryption or tokenization for the most critical identifiers, and data masking for non‑production and analytics. Choose per dataset: risk level, performance needs, integration effort and budget. Core safeguards for sensitive cloud data…