Categoria: Manuais
-

Continuous cloud security monitoring with metrics, logs, alerts and event correlation
Continuous cloud security monitoring combines metrics, centralized logs, real-time alerts and event correlation to detect and respond to threats quickly. Start by defining business‑aligned security objectives, then choose ferramentas de monitoramento contínuo de logs em nuvem and SIEM platforms, configure safe alert thresholds, build correlation rules and automate only well‑tested, reversible responses. Monitoring objectives and…
-

Zero trust network access (ztna) and Sse to protect remote cloud access
Zero Trust Network Access (ZTNA) and Security Service Edge (SSE) protect remote access to cloud resources by replacing flat VPN connectivity with identity‑centric, application‑level access. You authenticate users and devices, evaluate context (location, posture, risk), then grant least‑privilege access only to specific apps, continuously monitoring sessions and blocking or isolating risky behavior. Essential Controls for…
-

Security in saas, paas and iaas: shared responsibilities and hidden risks
For security in SaaS, PaaS and IaaS, choose based on how much control you truly need versus how much complexity you can reliably manage. In Brazil (pt_BR), many teams are safer starting SaaS-first, PaaS where you build code, and tightly-governed IaaS only where low-level control or regulatory constraints demand it. Top security contrasts at a…
-

Practical hardening guide for Aws, azure and google cloud security teams
Use this guide to harden AWS, Azure and Google Cloud with safe, repeatable steps: lock down identities, segment networks, harden workloads, configure managed services securely, protect pipelines and ensure logging plus incident playbooks. The focus is practical checklists and patterns your security team in Brazil can apply quickly. Critical hardening targets for cloud security Establish…
-

Zero trust in the cloud: implementing least-trust models in multi-cloud environments
Zero trust na nuvem in multi‑cloud means every request is verified based on identity, device, context and policy, regardless of network location. To implement it safely, start with an accurate asset and identity inventory, design minimal‑trust zones, enforce continuous authentication, microsegment workloads, automate policies, and track clear security and reliability metrics. Foundations to Prioritize Before…
-

Siem and Soar integration with cloud providers: architecture and use cases
SIEM-SOAR cloud integration means centralizing security telemetry from AWS, Azure and GCP into a SIEM, then using SOAR to automate triage and response with safe, well‑scoped actions. For teams in Brazil, start small with high‑value use cases, enforce least privilege, test playbooks in “dry‑run” mode, and continuously tune detections. Concise technical summary of SIEM-SOAR cloud…
-

Security by design in cloud Ci/cd pipelines: how to implement secure workflows
To implement security by design in cloud CI/CD pipelines, start by treating the pipeline itself as a high-value production system. Model threats, harden architecture with least privilege, secure secrets and artifacts, add automated checks (SAST/SCA), and continuously monitor. Align choices with your cloud provider, existing tools, and team skill set. Foundational principles for security-by-design in…
-
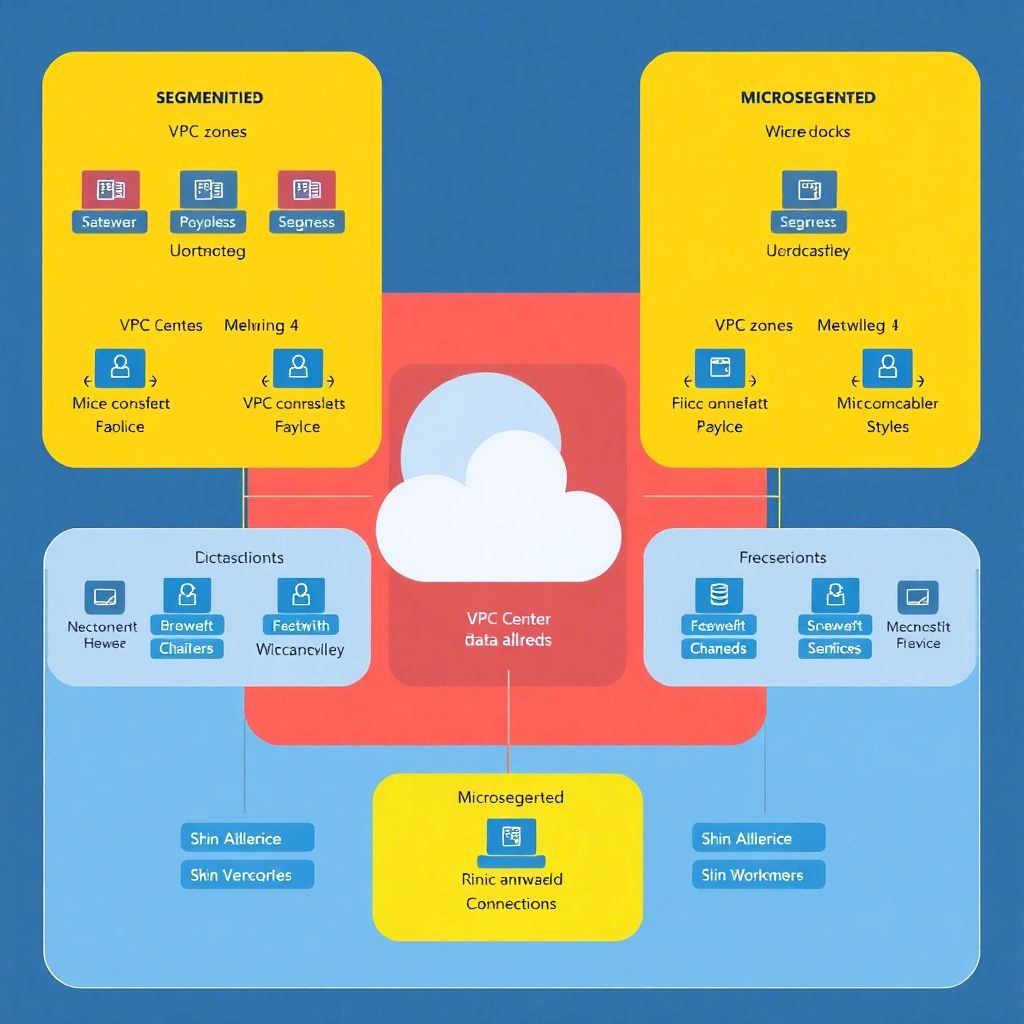
Network segmentation and microsegmentation in cloud: secure design and examples
Secure network segmentation and microsegmentation in cloud means grouping workloads by risk, identity and function, then enforcing least-privilege traffic rules at VPC/VNet and workload level. You define environment and application zones, label assets consistently, apply deny-by-default policies, and continuously validate flows with logging, tests and simple rollback options. Essential design checkpoints for network and microsegmentation…
-

Zero trust in cloud environments: principles, architecture and real use cases
Zero Trust em cloud means every access to your cloud resources is verified continuously, regardless of network location, device or user role. To apply it safely, map your identities, segment networks, encrypt sensitive data and enforce least privilege using cloud‑native controls plus focused third‑party tools where your provider is weaker. Core Principles Snapshot for Cloud…
-

Backup, disaster recovery and cyber resilience in modern cloud environments
Cloud backup, disaster recovery (DR) and cyber resilience in cloud environments mean combining automated backups, documented recovery objectives (RTO/RPO), tested runbooks and strong security controls. For empresas no Brasil, focus on multi-region backups, immutable storage, clear DR responsibilities, and regular restore drills aligned with your plano de continuidade de negócios em ambiente cloud. Operational priorities…