Why managed WAFs matter in 2026
In 2026, most web attacks never even reach your app; they die at the edge, inside a managed WAF. Cloud providers turned WAF into a kind of “security CDN layer”: always‑on, globally distributed and deeply integrated with identity, APIs and observability. Instead of managing rule engines and patches, teams now focus on tuning policies, plugging signals into SIEM and correlating WAF logs with zero‑trust access. That shift is what makes a revisão de ferramentas about waf gerenciado aws vs azure vs google cloud so relevant for real‑world architectures.
Key concepts: WAF, managed, and cloud‑native
A Web Application Firewall inspects HTTP(S) traffic and blocks malicious patterns such as SQL injection or credential stuffing. A “managed” WAF means the provider owns updates, rule feeds and infrastructure, while you only tune policies and exceptions. Cloud‑native WAFs go further: they hook into serverless, containers and API gateways, so you secure microservices without bolting on extra appliances. In 2026, this difference matters more than ever, because most internet‑facing endpoints live behind cloud load balancers or API gateways by default.
How the big three position their managed WAFs
AWS WAF is tightly tied to CloudFront, Application Load Balancer and API Gateway, with rules as code through CloudFormation and CDK. Azure Web Application Firewall sits on top of Application Gateway, Azure Front Door and Azure CDN, with strong hooks into Defender for Cloud. Google Cloud Armor doubles as WAF and DDoS shield, designed around load balancers and edge POPs. When people ask qual é o melhor waf gerenciado em nuvem para empresas, the honest answer is: it depends strongly on where your workloads and teams already live.
Text diagram: high‑level architecture
Picture a simple diagram in text form. On the left, users and bots: [Clients]. In the center, the managed WAF on the cloud edge: [CloudFront / Front Door / Cloud Armor]. Behind that, your services: [ALB / App Gateway / GCLB] → [Kubernetes / Functions / VMs]. The full flow looks like this: Clients → Managed WAF → Load Balancer or Gateway → Application. All three providers follow this basic structure, but the surrounding services, automation tools and logging pipelines differ a lot between platforms.
Deep dive: AWS managed WAF in 2026
On AWS, the managed WAF story revolves around three ideas: infrastructure‑as‑code, marketplace rule sets and tight observability. You can define rule groups in Terraform or CDK, plug threat intel feeds from vendors, and push logs into CloudWatch or S3 for SIEM. Modern patterns combine AWS WAF with AWS Shield, Route 53 and API Gateway for global APIs. As edge compute grows, more teams attach Lambda@Edge or CloudFront Functions to enrich WAF decisions with device risk or user reputation in real time.
New AWS trends: bots, APIs and account takeovers
By 2026, attacks shifted from noisy scans to profit‑driven bots and API abuse. AWS responded with better managed rules for account takeover protection, fraud‑oriented rate limiting and advanced bot control. You can model behavior per user or per session and feed signals into Cognito or custom auth flows. A common pattern is: WAF flags suspicious login bursts, sends metrics to CloudWatch, triggers Lambda playbooks and temporarily raises friction with extra MFA. This defense‑in‑depth approach is now more common than relying on static signatures alone.
Deep dive: Azure WAF in 2026
Azure Web Application Firewall leans heavily on integration with the broader security stack. Deployed on Application Gateway for regional apps or on Azure Front Door for global sites, it plugs into Microsoft Defender for Cloud, Sentinel and Entra ID. In practice that means WAF logs show up right next to identity anomalies and endpoint alerts. This makes Azure attractive for enterprises already invested in Microsoft 365 and Defender, because security teams get one pane of glass for SaaS, on‑prem and cloud workloads.
Zero‑trust and hybrid realities
Many organizations in 2026 still run hybrid: some workloads on‑prem, others in multiple clouds, with identity and devices managed through Entra ID. Azure WAF plays well here by bridging private networks, VPNs and ExpressRoute with Front Door security policies. A typical scenario: legacy apps in a datacenter fronted by Front Door + WAF, authenticated via Entra and monitored in Sentinel. Instead of refactoring those apps, you wrap them with modern controls. This hybrid‑friendly profile is a major reason Azure often wins in regulated industries.
Deep dive: Google Cloud Armor in 2026
Google Cloud Armor combines WAF and DDoS defense, heavily inspired by Google’s own edge protection for Search and YouTube. You attach it to HTTP(S) load balancers and now, increasingly, to API gateways and Cloud Run services. Cloud Armor shines for global latency and smart ML‑driven rules that learn from vast traffic baselines. For companies running analytics, media or gaming on Google Cloud, this low‑latency, always‑on shield pairs well with Cloud CDN and global load balancing, keeping both apps and APIs safer at planetary scale.
ML‑driven detection and SRE workflows
By 2026, Google leans into machine learning to spot anomalies: sudden spikes in failed logins, unusual geo mixes or abnormal request paths. Security and SRE teams create guardrails, then let the system adapt within safe bounds. A simple flow: Cloud Armor flags a surge in suspicious traffic, auto‑tightens a rate limit, then opens an incident in Opsgenie or PagerDuty via Pub/Sub. If the pattern stabilizes, the rule relaxes. This feedback loop mirrors SRE principles: automate the repetitive work and keep humans for ambiguous calls.
Comparing the big three: features and mindset
Any comparativo de waf gerenciado aws azure gcp in 2026 quickly reveals a pattern: features look similar on paper, but each platform has a personality. AWS emphasizes building blocks and flexibility, expecting you to wire WAF, Shield, Lambda and identity exactly as you like. Azure focuses on integrated security experiences across cloud, endpoints and SaaS. Google bets on globally distributed, ML‑assisted protection operating close to user traffic. Picking a platform is less about a single magic feature, more about which ecosystem matches your operating model.
Diagram: decision factors as a funnel
Imagine a funnel drawn in text. At the top: [Where are your workloads?]. That narrows into: [How centralized is your security team?]. Then: [Preferred tooling: Terraform, Sentinel, Chronicle, etc.]. At the bottom, you end up with: [Chosen managed WAF]. The idea is to avoid starting from vendor hype; instead, you feed constraints, team skills and compliance rules into the funnel. The output is rarely “perfect”, but it gives a pragmatic answer aligned with how your org already runs systems.
Pricing and cost control in 2026
When teams compare preço waf gerenciado aws azure google cloud, they usually discover three components: base protection per resource, rule evaluation or policy tiers, and per‑request charges. Subtle differences matter: one provider may bundle DDoS mitigation for free, another may charge per advanced managed rule group. The real trick is not chasing the lowest list price, but modeling realistic traffic patterns. With billions of requests per month, tiny per‑request deltas can dwarf your savings elsewhere, especially on heavily cached, consumer‑facing apps.
Practical cost‑saving patterns
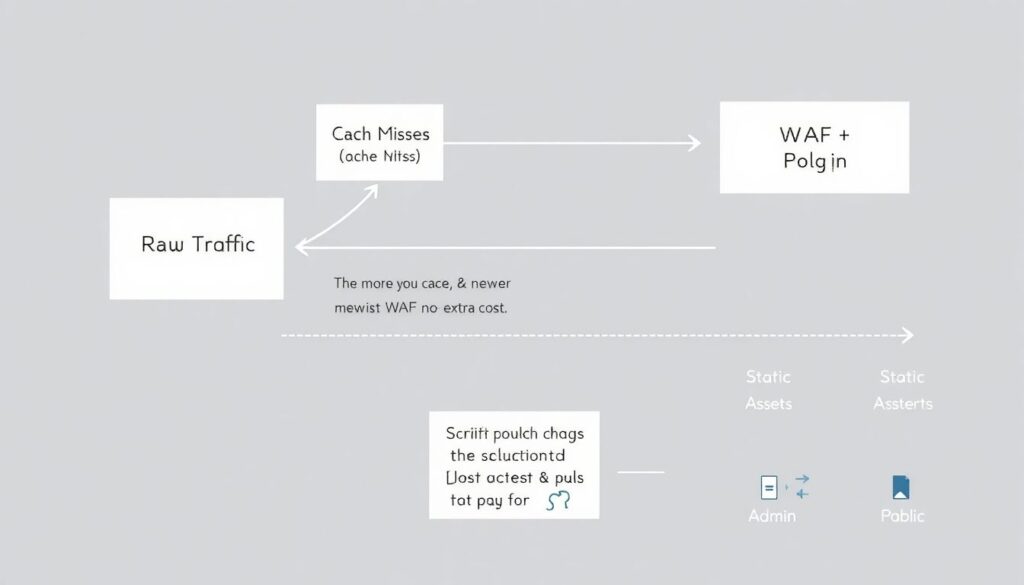
A simple cost diagram in words: [Raw traffic] hits [CDN cache] first, then only misses go to [WAF + origin]. The more you cache, the fewer WAF inspections you pay for. Many teams also split policies: strict rules for risky paths like /login or admin panels, lighter rules for static assets and public content. This selective inspection lowers latency and costs at the same time. Another win is consolidating multiple small apps behind one edge endpoint, so you share WAF policies instead of duplicating configs.
How to choose a managed WAF in 2026
Instead of hunting for abstract checklists on como escolher waf gerenciado em provedores de nuvem, ground the decision in how you actually build and run software. Map your pipelines, main programming languages, and identity sources. Then see which provider makes those flows feel natural instead of forced. If your teams already live in GitHub Actions plus Terraform, look at whose modules and examples are richer. If your SOC is centered on Sentinel or Chronicle, consider who plugs in with fewer custom connectors and brittle parsers.
Step‑by‑step selection process
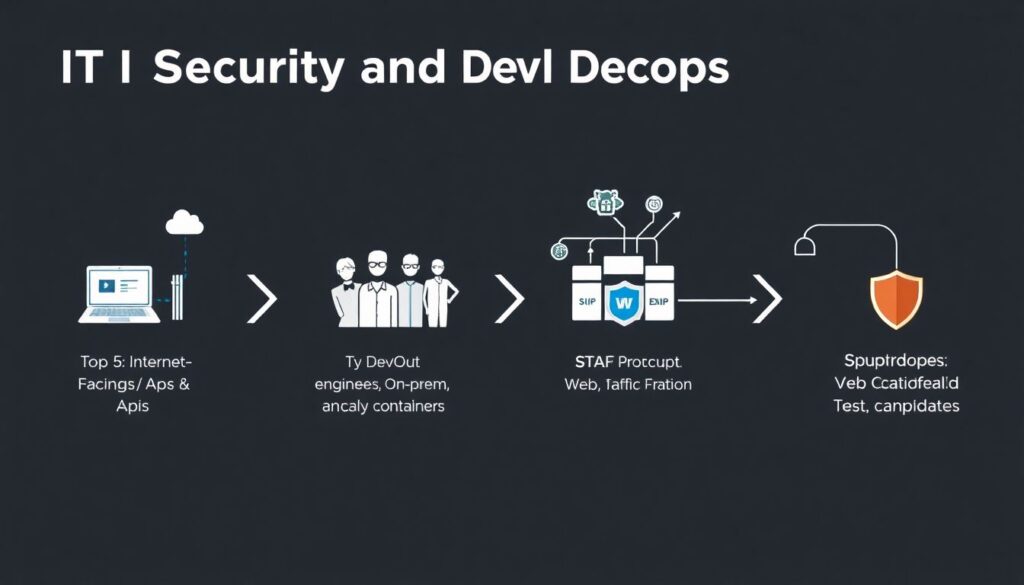
Use a simple numbered path to structure the choice:
1. List your top 5 internet‑facing apps and APIs and where they run today.
2. Identify who owns them and which tools they use for CI/CD and monitoring.
3. Map existing security tooling: SIEM, IAM, EDR, ticketing.
4. Prototype each candidate WAF with one real app, under real traffic.
5. Compare how quickly you can go from “new risk” to “updated policy in prod”.
If one platform turns this cycle into hours instead of days, that’s a strong signal.
Modern trends that should shape your choice
Three 2026 trends dominate managed WAF discussions. First, API‑first development: most value now sits behind JSON APIs, not HTML pages, so WAFs must understand OpenAPI, gRPC and GraphQL. Second, identity‑aware protections: rules that factor in device posture, session risk and user roles, not just IPs. Third, automation maturity: you want WAF configs in Git, reviewed like code, and rollouts tied to pipelines. Any serious evaluation of waf gerenciado aws vs azure vs google cloud should score providers against these trends, not just legacy OWASP checkboxes.
So, which one “wins”?
There is no single winner, but some patterns are emerging. If you are deeply invested in Microsoft’s ecosystem, Azure WAF plus Front Door usually becomes the melhor waf gerenciado em nuvem para empresas in that context. For teams living and breathing AWS, AWS WAF with Shield and Lambda still offers the most granular control. For global, API‑heavy, latency‑sensitive apps, many architects favor Cloud Armor’s edge footprint and ML‑assisted defense. The real win is picking one, integrating it deeply, and continuously tuning as threats and your architecture evolve.
