Advanced network segmentation and microsegmentation in public cloud means combining coarse VPC/subnet isolation with fine‑grained, identity‑aware policies at workload and service level. For pt_BR environments, prioritize simple, auditable controls, progressive rollout, and clear rollback paths while aligning with zero‑trust. Start with critical workloads, then gradually expand segmentation coverage.
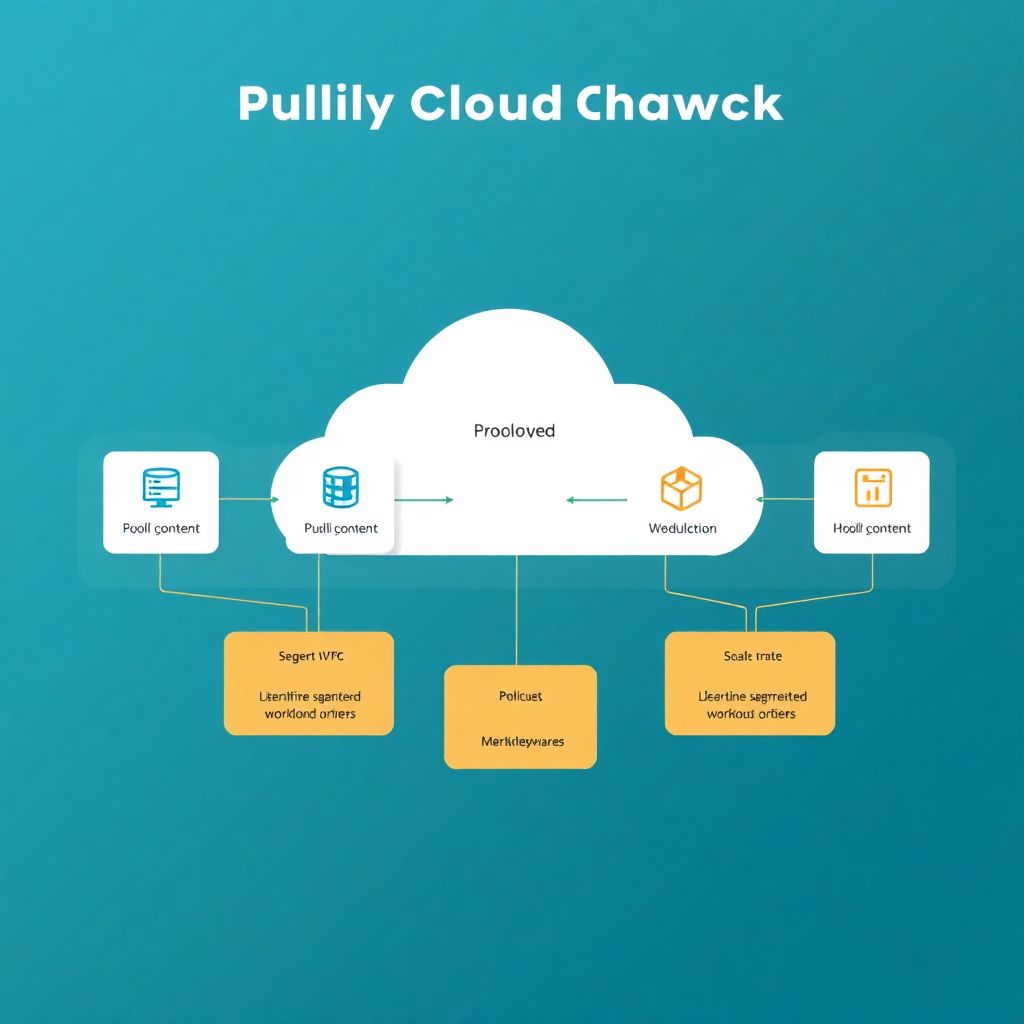
Essential design principles for cloud network segmentation
- Use layered segmentation: VPCs/VNets/Subnets for coarse isolation, security groups/NSGs for stateful controls, and microsegmentation for workload‑level policies.
- Design policies around application flows and identities, not only IPs or ports, to support dynamic cloud scaling.
- Start with high‑value assets and risky paths, then iteratively refine segment boundaries and rules.
- Automate policy generation, testing, and deployment via CI/CD and infrastructure‑as‑code.
- Continuously monitor traffic, validate intent vs. reality, and tune rules based on observed behavior.
- Always define safe rollback steps and blast‑radius limits before enforcing new segmentation policies.
Mapping workload trust boundaries and dependency graphs
Advanced segmentação avançada de rede na nuvem makes sense when you have business‑critical workloads, compliance requirements, or multi‑tenant environments. It is most effective when you know which services must talk to which, and which paths are sensitive (payments, PII, admin APIs, backups, monitoring).
When you should avoid or postpone deep microsegmentação em cloud pública:
- Teams lack basic inventory of services, ports, and dependencies; focus first on visibility and documentation.
- Legacy applications break easily with minor network changes; start with observability and non‑enforced policies.
- No automation or IaC: purely manual rule management quickly becomes unsafe and error‑prone.
- There is no owner for segmentation policy decisions; clarify responsibility (Cloud, Security, or Platform team).
Practical steps to map trust boundaries:
- Inventory workloads by business function (billing, analytics, customer‑facing APIs, internal tools).
- Identify data sensitivity levels (public, internal, confidential, regulated) and tag workloads accordingly.
- Capture dependencies using flow logs, APM, or service mesh telemetry (who talks to whom, on which ports).
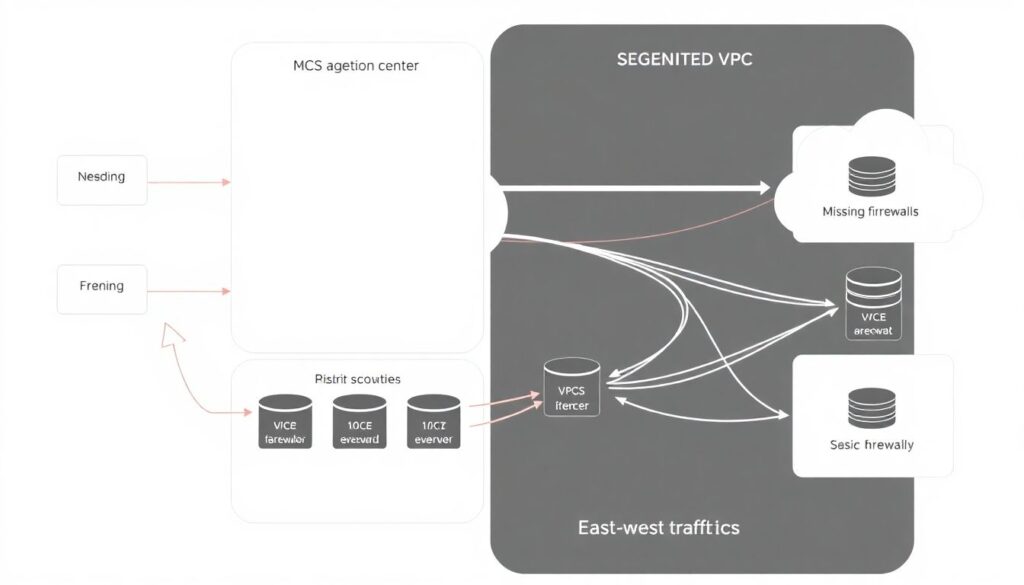
- Group workloads into trust zones: internet‑facing, partner‑facing, admin, data, and build/deploy.
- Document allowed flows between zones (e.g., Web → App → DB) and block all others by design.
Selecting segmentation primitives: VPCs, subnets, security groups and overlays
For Brazilian organizations evaluating ferramentas para segmentação de rede em nuvem pública, most stacks mix native cloud primitives with additional overlays or soluções de segurança com microsegmentação em cloud. Choose tools that your team can operate safely and that integrate with your existing CI/CD and identity stack.
| Approach | Granularity | Typical Use | Pros | Cons / Risks |
|---|---|---|---|---|
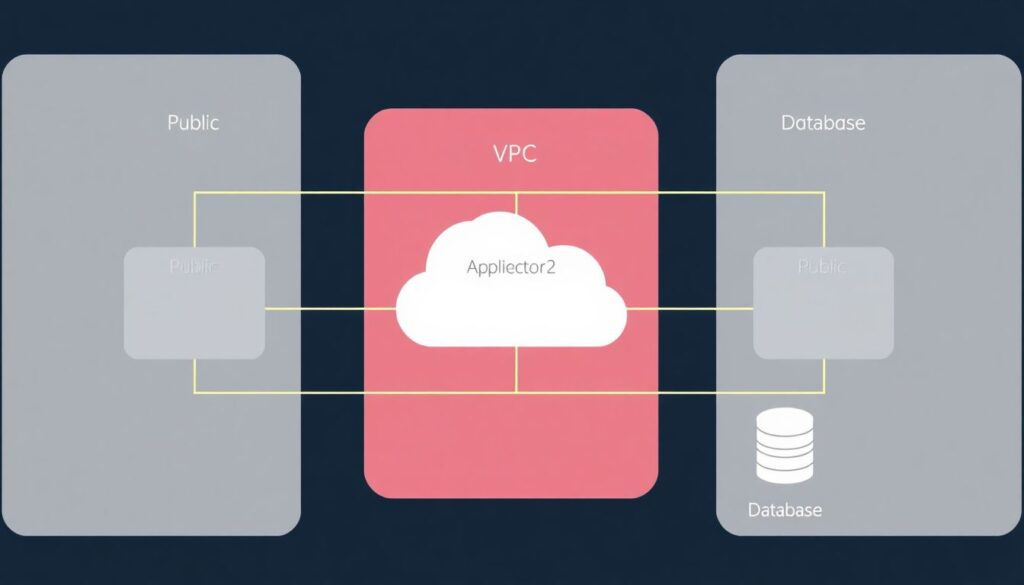
| VPC / VNet | Coarse (per environment / tenant) | Isolate prod vs. dev, tenants, or regulatory domains | Strong blast‑radius control, simple mental model | Too coarse for app‑level least privilege, more peering complexity |
| Subnet / Subnet tiers | Medium (per tier or function) | Public/DMZ, app, data tiers; zoning admin vs. non‑admin | Clear separation, integrates with routing and firewalls | IP‑based segmentation; refactors can be disruptive |
| Security Groups / NSGs / Firewall rules | Fine (per instance or NIC) | Control east‑west and inbound access at workload level | Native, cheap, easy to automate, stateful | Rules can sprawl; IP‑oriented, harder with dynamic scaling |
| Microsegmentation (agents / service mesh) | Very fine (per service, identity, or process) | Zero‑trust, compliance, multi‑tenant apps, container workloads | Identity‑aware, portable across clouds, great visibility | Additional complexity, agents/sidecars, must manage policy lifecycle |
What you typically need in terms of access and tooling:
- Cloud admin or network‑admin permissions to manage VPC/VNet, subnets, route tables, and firewalls.
- Permissions for security groups/NSGs and cloud firewalls (AWS Security Groups and NACLs, Azure NSGs and Azure Firewall, GCP firewall rules and VPC Service Controls).
- Ability to enable and read flow logs and telemetry (VPC Flow Logs, NSG Flow Logs, Cloud Logging, etc.).
- For overlays and microsegmentation: ability to deploy agents or sidecars on hosts, VMs, and clusters.
- Infrastructure‑as‑Code (Terraform, Pulumi, CloudFormation, ARM/Bicep) plus CI/CD integration.
Short, concrete examples of segmentation primitives:
- AWS – Lock DB to app security group only
aws ec2 authorize-security-group-ingress --group-id sg-db --protocol tcp --port 5432 --source-group sg-app - Azure – NSG rule for Web → App
az network nsg rule create --nsg-name app-nsg --name allow-web-to-app --priority 200 --direction Inbound --access Allow --protocol Tcp --destination-port-ranges 8080 --source-address-prefixes WebSubnetCIDR - GCP – Firewall restricting SSH to bastion
gcloud compute firewall-rules create allow-ssh-from-bastion --network=prod-vpc --allow=tcp:22 --source-tags=bastion --target-tags=admin-host
Identity- and context-aware microsegmentation: service mesh and agent approaches
Before diving into a step‑by‑step rollout of melhores práticas de microsegmentação para segurança em cloud, keep in mind these risk and limitation highlights:
- Over‑restrictive policies can break critical paths; always test in observe/dry‑run mode first.
- Agent or sidecar failures can impact data plane; plan for graceful degradation and maintenance windows.
- Mis‑aligned identity mapping (service accounts, tags, labels) leads to unexpected access grants or denials.
- Multi‑cloud or hybrid environments require consistent tagging and naming; drift increases risk of gaps.
- Define segmentation objectives and scope
Start with a small, high‑value scope such as a single business application or cluster in your public cloud. Define what you want to protect (e.g., payment API, internal admin console) and what “blocked” traffic looks like.
- Pick 1-2 representative environments (e.g., staging and a non‑critical production slice).
- List explicit in‑scope services, namespaces, or VMs.
- Choose between service mesh and host agents
For containerized workloads (Kubernetes, ECS, AKS, GKE), a service mesh (Istio, Linkerd, Consul) often makes identity‑aware policies simpler. For mixed VM and on‑prem estates, host‑based agents or kernel firewalls work better.
- Service mesh: great for HTTP/gRPC, mTLS, and per‑service identities.
- Agents: cover non‑Kubernetes VMs and legacy apps with process‑aware policies.
- Establish identity and labeling standards
Define a consistent scheme: cloud tags, Kubernetes labels, and service accounts that represent roles (web, app, db, admin). Policies should target these identities, not IPs.
- Example label set:
app=myapp,tier=web|app|db,env=prod|stage,owner=squad‑x.
- Example label set:
- Enable telemetry‑only mode first
Most microsegmentation platforms and meshes support observe/allow‑all modes that log flows without blocking. Turn this on to learn traffic patterns and generate candidate policies.
- In Istio, start with permissive mTLS and authorization policies that audit but do not deny.
- In agent products, avoid default‑deny until you have validated baseline rules.
- Generate and review candidate policies
Use flow logs and telemetry to propose “allow‑lists” per identity. Review rules with application owners to confirm which flows are essential vs. noise.
- Collapse duplicate rules by identity and port to reduce policy size.
- Mark flows that are temporary (migration, batch jobs) to avoid hard‑coding them.
- Implement least‑privilege rules in non‑prod
Apply microsegmentation policies in a staging environment first, with default‑deny between identities and explicit allows for known flows.
- Example Istio AuthorizationPolicy for app → db:
apiVersion: security.istio.io/v1beta1 kind: AuthorizationPolicy metadata: name: allow-app-to-db spec: selector: matchLabels: app: db rules: - from: - source: principals: ["cluster.local/ns/prod/sa:app-sa"] to: - operation: ports: ["5432"]
- Example Istio AuthorizationPolicy for app → db:
- Gradually enable enforcement with rollback paths
Shift from observe to enforce in narrow slices: one namespace, one ASG, or one zone at a time. For each rollout, define how to revert fast if something breaks.
- Maintain a “last known good” policy bundle in your repo.
- Prepare scripts to disable agents or relax policies quickly (e.g., switch to allow‑all profile).
- Integrate with CI/CD and change management
Treat microsegmentation policies as code alongside application deployments. Each new service or port should come with its own segmentation diff.
- Require reviews from both app owners and security engineers.
- Use pipelines to run policy validation tests before applying to production.
- Continuously refine based on alerts and incidents
Monitor denies, latency changes, and error rates after enforcement. Tweak rules to reduce false positives without widening access unnecessarily.
- Feed blocked‑flow logs into SIEM to spot scanning, lateral movement, or misconfigurations.
Policy orchestration, CI/CD integration and automated enforcement
Use this checklist to verify that orchestration and enforcement are safe and sustainable:
- Policies live in version control with clear owners, code reviews, and change history.
- Each application repository includes its own segmentation definitions (e.g., SG rules, mesh policies).
- CI/CD pipelines validate policies syntactically and run basic reachability tests before applying.
- Deployments use progressive strategies (canary, blue/green, or per‑AZ rollout) for new rules.
- Every change has a documented rollback command set and time‑boxed change window.
- Drift detection is enabled: actual cloud rules are periodically compared to policy‑as‑code.
- Approvals are risk‑based: changes that widen access to sensitive zones require higher‑level review.
- Automation can pause or abort rollouts when health checks or SLOs degrade after policy changes.
- Cross‑cloud policy templates exist so that equivalent controls are enforced across major providers.
Observability, telemetry and threat detection across segmented zones
Frequent mistakes when instrumenting segmented environments:
- Relying only on perimeter logs and ignoring east‑west traffic inside VPCs/VNets.
- Not enabling flow logs at the right level (VPC, subnet, NSG, firewall), losing context needed to tune microsegmentation.
- Mixing production and non‑production logging destinations, complicating incident response and retention policies.
- Failing to correlate network telemetry with identity (service account, user, role), making investigations slower.
- Alerting only on denies, not on unusual allows (e.g., rare cross‑zone access to sensitive data).
- Ignoring performance impact: added hops (proxies, sidecars, firewalls) can introduce latency and packet drops.
- No synthetic tests to ensure that “allowed” traffic remains healthy after rule changes.
- Under‑provisioned logging pipelines causing dropped logs during peak or attack scenarios.
Validation, risk-based testing and incident playbooks for segmented estates
Alternatives and complementary approaches you can consider, and when they are appropriate:
- Strong perimeter plus basic tiered segmentation: Use VPC/VNet plus public/app/db tiers with conservative firewall rules. Suitable for smaller teams or early‑stage migrations where full microsegmentation would overload operations.
- Software‑defined perimeter (SDP) and ZTNA: Focus on user‑to‑app access (VPN replacement, identity‑based access brokers) rather than deep east‑west microsegmentation. Useful when remote workforce and partner access are the primary risks.
- Managed cloud security services: Rely on provider‑native services (AWS Network Firewall, Azure Firewall, GCP Cloud Armor plus VPC SC) and managed microsegmentation platforms. Fits organizations lacking in‑house network security expertise.
- Host‑based hardening with minimal network controls: Emphasize OS hardening, EDR, and application‑level auth while keeping network rules simple. Reasonable for homogeneous fleets where changing the network layer is difficult or risky.
Practical answers to recurring operational concerns
How do I start microsegmentation in a legacy‑heavy environment safely?
Begin with visibility: enable flow logs, install agents or sidecars in monitor‑only mode, and map dependencies. Select one non‑critical application, apply least‑privilege rules in staging, then gradually expand. Maintain clear rollback steps and avoid touching shared legacy components first.
What if a segmentation rule breaks a production service?
Plan for this in advance: keep previous policies versioned, deploy rules progressively, and have scripts ready to revert changes quickly. Use health checks and alerts that automatically pause or roll back CI/CD pipelines when errors spike after rule deployment.
How can I manage policies across multiple public cloud providers?
Create an abstract policy model (identities, zones, intents) and generate provider‑specific implementations (SGs, NSGs, firewall rules, mesh policies). Use IaC and templates to ensure consistency, and regularly audit that effective rules in each cloud match your central definitions.
Do I still need traditional firewalls if I use microsegmentation?
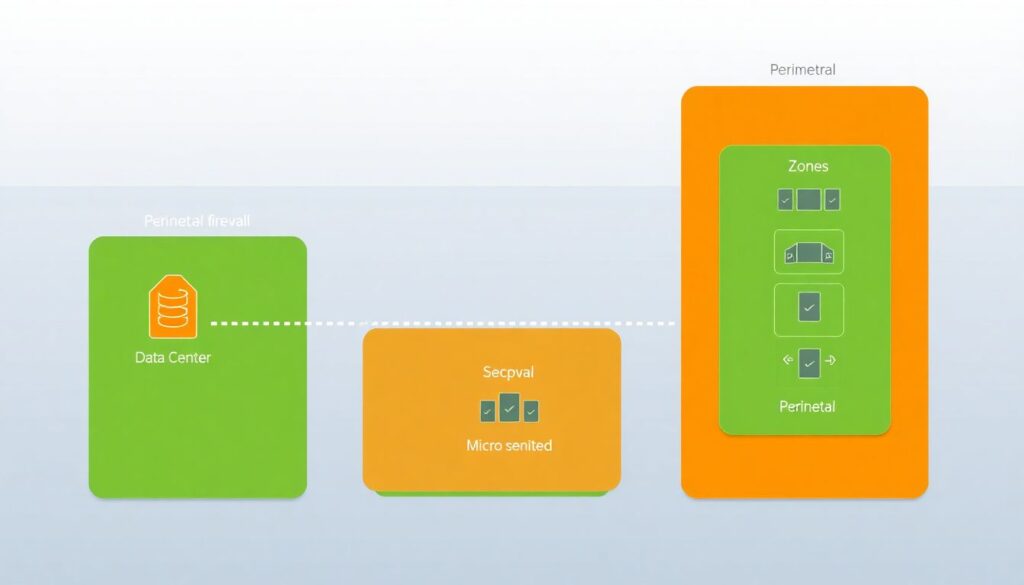
Yes, perimeter firewalls remain important to block unsolicited internet traffic and enforce coarse controls. Microsegmentation complements them by enforcing least‑privilege inside the environment. You typically keep both, but you can simplify perimeter rules as internal policies mature.
How do I explain the value of microsegmentation to non‑technical stakeholders?
Frame it as limiting the spread of attacks and outages: even if one server is compromised, segmentation prevents attackers from freely moving to databases or critical systems. Emphasize reduced blast radius, improved compliance posture, and clearer visibility into who accesses what.
What metrics show that my segmentation strategy is working?
Track reduced number of open paths to sensitive zones, stability of policies over time, mean time to detect lateral‑movement attempts, and frequency of segmentation‑related incidents. Also monitor change‑related outages; a mature program keeps them low while tightening controls.
Is microsegmentation overkill for small teams or startups?
Deep microsegmentation may be excessive early on. Start with clean VPC/VNet design, minimal open ports, and simple identity‑based access. Introduce finer microsegmentation only for high‑value data or once operational maturity and automation justify the added complexity.