Serverless security in the cloud depends on treating each function as a small, internet-exposed application: harden inputs, minimize permissions, secure the build pipeline, and monitor runtime behavior. Focus on least‑privilege IAM, strict dependency control, event validation, and dedicated monitoring platforms for serverless architecture instead of relying only on traditional VM or container defenses.
Security executive summary for serverless environments
- Model serverless functions as untrusted entry points; validate all events (HTTP, queues, streams, schedulers, webhooks).
- Apply strict least‑privilege IAM per function; never share broad roles across unrelated functions.
- Lock down the supply chain: pinned dependencies, signed artifacts, and automated vulnerability scanning.
- Use dedicated plataformas de monitoramento e segurança para arquitetura serverless, not only generic logs.
- Design for resource limits and throttling to mitigate denial‑of‑wallet and resource exhaustion attacks.
- Continuously test with security-focused CI gates and prepare incident playbooks specific to serverless workflows.
Threat model and risk taxonomy specific to serverless
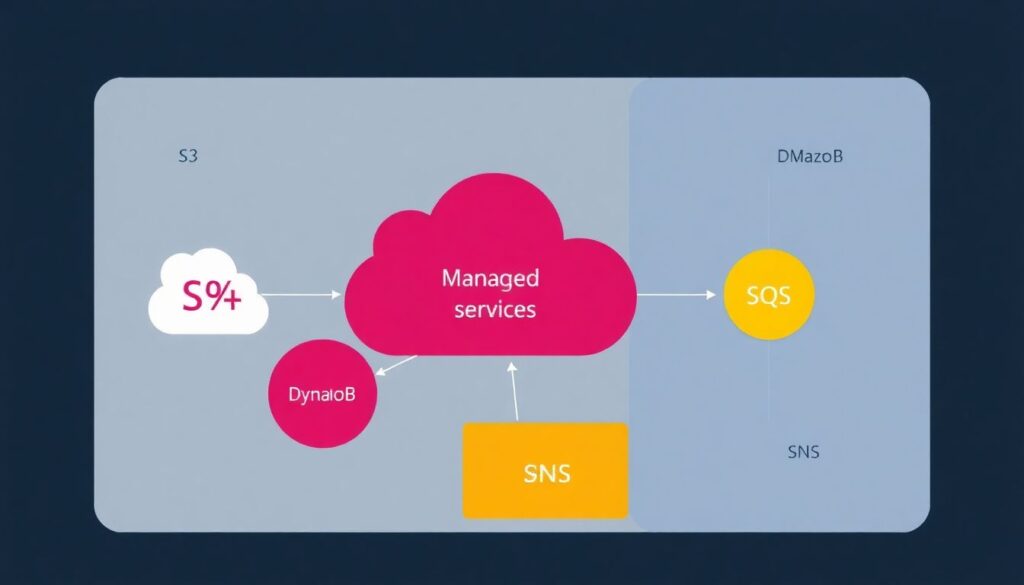
Serverless shifts many responsibilities to the cloud provider, but you still own identidade, código, dados e integrações. When planning segurança em serverless na nuvem, threat modeling must reflect event‑driven flows, ephemeral compute, and heavy dependency on managed services.
When serverless security patterns are a good fit
- Workloads with clear, small, event‑driven responsibilities (e.g., API endpoints, data transformation jobs, async workers).
- Teams already comfortable with IaC (CloudFormation, CDK, Terraform, Pulumi) and basic IAM concepts.
- Environments heavily using managed services (S3, DynamoDB, SQS, SNS, EventBridge, API Gateway) in AWS or equivalents.
- Projects needing fast iteration, short-lived experiments, and fine‑grained scaling while maintaining governance.
Threat categories specific to serverless
- Event injection and confused deputy: attackers manipulate event sources (e.g., S3 object keys, queue messages) to trigger dangerous code paths or abuse cross‑service permissions.
- Over‑privileged functions: a single compromised function can access unrelated data because it has a broad IAM role.
- Untrusted dependencies and layers: malicious or outdated libraries, Lambda Layers, or containers compromise multiple functions at once.
- Denial‑of‑wallet/resource exhaustion: high concurrency, long execution time, or recursive invocations lead to excessive cost or throttling.
- Insecure configuration of triggers: misconfigured API Gateway, S3, or queue policies expose functions publicly or bypass authentication.
- Data exposure via logs and env vars: secrets and PII accidentally logged or stored in environment variables.
When serverless may not be the best option
- Heavy stateful workloads or long‑running jobs that exceed function time limits and are hard to break into idempotent steps.
- Scenarios requiring very low‑level network controls (custom IDS inline, raw sockets) not exposed in managed runtimes.
- Legacy stacks with large monolithic frameworks that are hard to split into small, cold‑start‑friendly functions.
- Environments with strict on‑prem or air‑gapped constraints where managed cloud services are not allowed.
Function-level vulnerabilities: input handling, deserialization, and resource exhaustion
To implement boas práticas de código seguro em aplicações serverless, you need a minimum toolset and access model that makes safe defaults easy and risky patterns visible.
Prerequisites and recommended access
- Cloud account and IAM access
Have a non‑root account with permissions to manage functions, IAM roles, and logging. In AWS, this usually means a developer or DevOps role with access to Lambda, IAM, CloudWatch, and your main data services (e.g., S3, DynamoDB). - Infrastructure as Code (IaC) tooling
Use CloudFormation, AWS CDK, Terraform, or Pulumi to define functions, triggers, and IAM. This allows security reviews and pull‑request based approvals for all changes. - Language‑level security libraries
Install input validation, serialization, and crypto libraries appropriate for your stack (e.g., Joi/Zod for Node.js, Marshmallow/Pydantic for Python, class‑validator for TypeScript). - Static and dependency analysis tools
- Static analysis (SAST) integrated into CI (e.g., CodeQL, SonarQube, Semgrep) focused on input handling and injection flaws.
- Dependency scanning (SCA) for your runtime and Lambda Layers (e.g., Dependabot, Renovate, Snyk, Trivy, OWASP Dependency‑Check).
- Access to monitoring and logs
Ensure you can configure log retention and alerts in CloudWatch or equivalent, plus any plataformas de monitoramento e segurança para arquitetura serverless you use (Datadog, New Relic, Lumigo, Dynatrace, etc.).
Baseline defensive patterns for each function
- Strict input validation: treat API Gateway events, SQS messages, stream records, and S3 events as untrusted. Use schemas for body, headers, and path/query parameters; reject early if invalid.
- Safe deserialization: avoid unsafe formats (e.g., Python pickle, Java native serialization) and disable features that allow code execution during deserialization.
- Timeouts and memory limits: set conservative values per function to limit resource exhaustion and amplify the effect of malicious workloads.
- Idempotent logic: design handlers to safely retry without double‑charging or corrupting state, using idempotency keys or conditional writes.
- Output encoding: encode outputs according to the sink (JSON, HTML, SQL, logs) to reduce injection risk in downstream services.
Examples of safe patterns
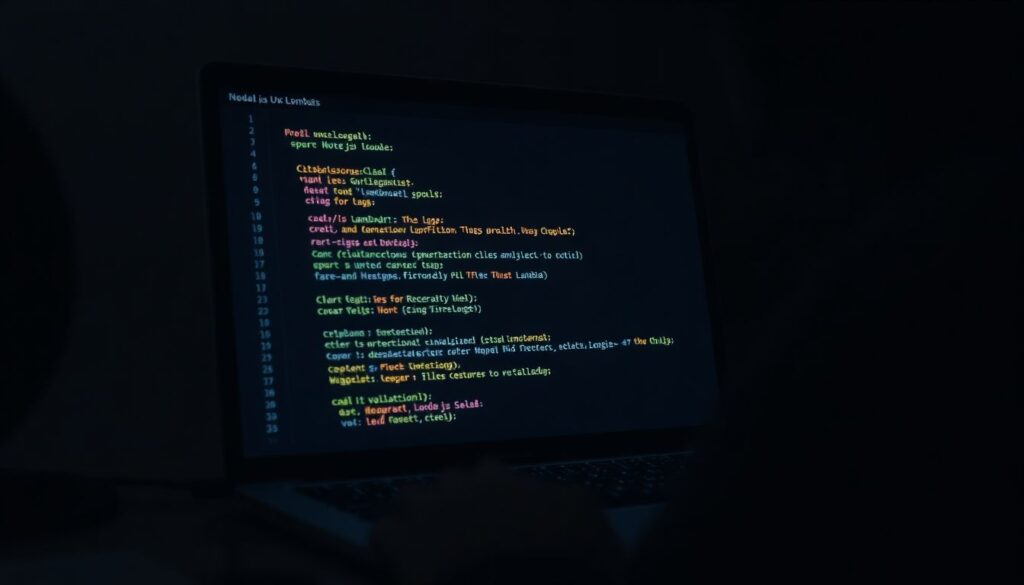
Example (Node.js Lambda behind API Gateway) validating input and enforcing timeouts in code in addition to platform limits:
exports.handler = async (event) => {
const start = Date.now();
const deadlineMs = 800; // internal safety margin
const body = JSON.parse(event.body || "{}");
if (typeof body.email !== "string") {
return { statusCode: 400, body: "Invalid email" };
}
if (Date.now() - start > deadlineMs) {
throw new Error("Internal timeout");
}
// business logic...
};This complements platform timeouts and reduces the blast radius of slow dependencies.
Identity, access and least-privilege patterns for ephemeral compute
Identity and access control is where a compromise becomes a breach. There are safe, incremental steps to implement least privilege for ephemeral compute without breaking productivity, especially when you plan how to proteger funções Lambda serverless from the start.
Risk considerations before you change permissions
- Over‑restricting IAM too quickly can break production flows; test changes in non‑prod stages first.
- Event‑driven architectures have many hidden paths; ensure all triggers are mapped before cutting permissions.
- Shared roles across multiple functions amplify blast radius; refactoring them may require tagging and discovery work.
- Excessive inline policies make audits hard; prefer reusable managed policies with clear names and scope.
- Map functions, triggers, and data flows
Start by listing all functions, their triggers, and the resources they touch.- Export your configuration from IaC or via cloud APIs (e.g., AWS Config, Lambda/ListFunctions, EventBridge, S3 notifications).
- Identify functions with multiple triggers (API + SQS + schedule), as they often accumulate excessive permissions.
- Create one execution role per function or small bounded group
Avoid a single broad role used by dozens of functions. Instead:- Define a dedicated role for each function, or at most for tightly related ones in the same bounded context.
- Name roles and policies by business capability, not by team (e.g.,
role-orders-write-dynamodb).
- Design least-privilege policies based on required actions
For each function, list exactly what it needs to do (e.g.,GetObjectfrom one bucket,PutItemin one table).- Use granular resource ARNs instead of
*(e.g., one S3 bucket prefix, one DynamoDB table). - Avoid wildcards in actions; prefer explicit verbs (
s3:GetObject,dynamodb:PutItem).
- Use granular resource ARNs instead of
- Use condition keys to further restrict access
Where possible, add IAM conditions:- Limit access from specific VPCs or source services (e.g.,
aws:SourceArnfor S3 or EventBridge triggers). - Use tags to restrict what a function can touch (e.g., S3 objects with specific tags).
- Limit access from specific VPCs or source services (e.g.,
- Separate data-plane and control-plane permissions
Functions should rarely need to manage infrastructure.- Data plane: read/write to S3, DynamoDB, queues, and APIs for normal operations.
- Control plane: create or modify resources; keep these in CI/CD roles, not in runtime functions.
- Integrate authentication and authorization at the edge
For HTTP APIs, offload authN/Z from functions whenever possible.- Use API Gateway authorizers or identity services (Cognito, Auth0, custom JWT validation) before invoking functions.
- Pass only necessary claims to the function, and perform business‑level authorization checks there.
- Continuously audit and right-size permissions
Review logs and access analyzer tools regularly.- Enable IAM Access Analyzer or similar tools to detect unused or overly permissive policies.
- Iteratively shrink permissions based on actual usage patterns observed in logs.
Secure build and supply-chain controls for serverless artifacts
Securing the build and supply chain for serverless is as important as runtime hardening. Many of the melhores ferramentas de segurança para serverless aws and other clouds focus on this layer, because a compromised artifact quickly propagates to hundreds of functions.
Checklist to validate your build and supply-chain posture
- All functions and infrastructure are defined through IaC, with changes reviewed via pull requests and code review.
- CI pipelines include static analysis (SAST) and dependency scanning (SCA) on every commit to main and before deployment.
- Dependencies are version‑pinned (no loose ranges like
^or~in production) and regularly updated with automated PRs. - Lambda deployment packages or container images are built in a dedicated, isolated build environment, not on developer laptops.
- Build outputs are signed (e.g., using Sigstore/cosign for images) and the deployment pipeline verifies signatures before publish.
- Only CI/CD roles can deploy or update functions; interactive consoles are restricted to read‑only or emergency break‑glass accounts.
- Lambda Layers and shared libraries go through the same review and scanning as application code, with clear ownership.
- Secrets are never embedded into code or artifacts; they are injected at runtime via secrets managers or parameter stores.
- SBOMs (Software Bill of Materials) are generated for function packages or images and stored for later incident investigations.
- Third‑party plugins in CI/CD pipelines are reviewed and updated regularly to reduce the risk of supply‑chain compromise.
Runtime protections: sandboxing, isolation, and observability
Even with secure code and artifacts, runtime misconfigurations can expose you. Platforms provide basic sandboxing, but you need explicit controls for observability and isolation, especially when you rely on plataformas de monitoramento e segurança para arquitetura serverless.
Common mistakes to avoid in runtime configuration
- Placing highly sensitive functions in a public subnet with outbound internet access, instead of private subnets with controlled egress.
- Disabling or failing to configure function‑level concurrency limits, making the system vulnerable to cost and capacity exhaustion.
- Using the same environment variables (and secrets) across dev, staging, and production stages without proper isolation.
- Logging raw tokens, passwords, or full PII payloads in CloudWatch or third‑party monitoring tools.
- Ignoring cold start and reuse behavior: writing code that assumes a fresh environment on every invocation, leading to data leakage across tenants.
- Not enabling structured logging and correlation IDs, which makes incident triage slow and incomplete.
- Aggregating logs but not defining alerts for suspicious patterns (e.g., many failed auth attempts, spikes in error rates, unexpected regions).
- Allowing direct internet exposure of function URLs or API endpoints without WAF or rate limiting in front.
- Running all functions in one shared VPC security group, making network‑level isolation impossible.
- Deploying observability agents or extensions without reviewing their permissions and data access.
Testing, deployment gates and incident response tailored to serverless
Testing and incident handling for serverless must respect its event‑driven nature and tight integration with managed services. There is no single correct stack; choose an approach that matches your maturity and regulatory needs while keeping the steps safe and understandable.
Alternative implementation patterns and when to use them
- Lightweight, function-centric security for small teams
Best when you have a few services and a small team.- Use simple unit tests with mocked events plus basic SAST/SCA in CI.
- Manually define canary or linear deployments with health checks via CloudWatch alarms.
- Prepare minimal runbooks: how to disable a trigger, roll back a version, and rotate credentials.
- Platform-integrated security gates
Suitable when you rely heavily on AWS native tools.- Use AWS CodePipeline/CodeBuild with built‑in and third‑party scanners, and require passing checks before promotion.
- Integrate AWS Config, Security Hub, and IAM Access Analyzer to evaluate serverless resources against policies.
- Define incident response playbooks that trigger via EventBridge on specific findings or CloudWatch metrics.
- Centralized, multi-cloud security platform
Fits organizations running in multiple clouds or with strong compliance needs.- Adopt specialized ferramentas de segurança para serverless aws and equivalents on other providers, integrated into a central dashboard.
- Run continuous posture management across functions, APIs, and data stores, with auto‑generated tickets for misconfigurations.
- Standardize incident classification (e.g., data leakage, supply‑chain event, credential abuse) and response steps across all stacks.
- Security-as-code with strict policy enforcement
Appropriate for highly regulated sectors.- Describe security policies as code (Open Policy Agent, custom rules) applied to IaC and CI/CD stages.
- Block deployments that violate minimal baselines (e.g., wildcard IAM, public buckets, missing logs) automatically.
- Combine runtime anomaly detection with pre‑approved auto‑remediation for well‑understood failure modes.
Common implementation doubts and clarifications
How is serverless security different from container or VM security?
You rely more on managed services and less on OS hardening. Network controls are coarser, while identity and event validation become central. You focus on least‑privilege IAM, secure event sources, and code‑level protections rather than patching operating systems or managing long‑lived hosts.
What are essential steps to protect AWS Lambda functions?
To proteger funções Lambda serverless, give each function its own minimal IAM role, validate all inputs from triggers, set strict timeouts and memory, store secrets in a managed secrets service, and enable detailed logging with alerts. Use IaC so every change is reviewable and auditable.
Which tools should I start with for serverless security on AWS?
Begin with cloud‑native capabilities (IAM Access Analyzer, Config, CloudWatch, Security Hub), then add melhores ferramentas de segurança para serverless aws such as SAST/SCA scanners integrated in CI and optional specialized serverless observability platforms if your environment is complex.
How do I apply secure coding practices in multiple serverless languages?
Define cross‑language boas práticas de código seguro em aplicações serverless: strict input validation, safe deserialization, proper output encoding, and error handling that does not leak secrets. Then complement them with language‑specific linters and frameworks that enforce these patterns automatically.
Do I still need a WAF in front of serverless APIs?
Yes, for internet‑facing HTTP endpoints, a WAF helps block common web attacks before they hit your functions. Combine it with authentication at API Gateway, rate limiting, and function‑level validation for defense in depth instead of replacing code defenses.
How should I monitor a large serverless environment effectively?
Standardize structured logs, correlation IDs, and metrics across all functions. Centralize data into one or more plataformas de monitoramento e segurança para arquitetura serverless and configure alerts for anomalies in errors, latency, and access patterns. Regularly test alerting paths and on‑call processes.
Can I reuse roles and shared layers across teams safely?
You can, but carefully. Shared roles increase blast radius; prefer narrowly scoped, per‑function roles. Shared Lambda Layers must be owned, scanned, and versioned rigorously. Treat them as critical dependencies with the same controls as your main application code.