Why threat modeling in cloud workloads stopped being optional
Over the last three years, cloud has become the default place to run almost everything, and attackers have adapted faster than most teams. According to public breach reports up to 2023, more than 45–50% of major incidents had at least one cloud misconfiguration component, and roughly a third involved abuse of overly permissive IAM roles. When you run distributed services across regions, accounts and providers, guessing where things can break no longer works. That is exactly where threat modeling em cloud para arquiteturas distribuídas comes in: it gives you a structured way to ask “what can go wrong here?” before an adversary answers that question for you in production.
Real cases: when cloud threat models existed only on slides
Consider a fintech that moved its core payment APIs to Kubernetes on a major provider and proudly passed penetration tests twice. The invisible gap sat in their event‑driven architecture: a serverless function could be triggered by poisoned messages from a partner queue. Nobody modeled threats around that data flow, and an attacker eventually chained a queue injection with an SSRF in the function’s HTTP client, gaining access to internal metadata and sensitive configs. Incidents of this pattern have grown steadily in published reports since 2021, especially in financial and SaaS sectors. The lesson is blunt: any threat model that stops at “web app + DB” and ignores messaging, serverless and CI pipelines is a liability, not a safeguard.
From diagrams to decisions: como criar modelo de ameaças para workloads em nuvem
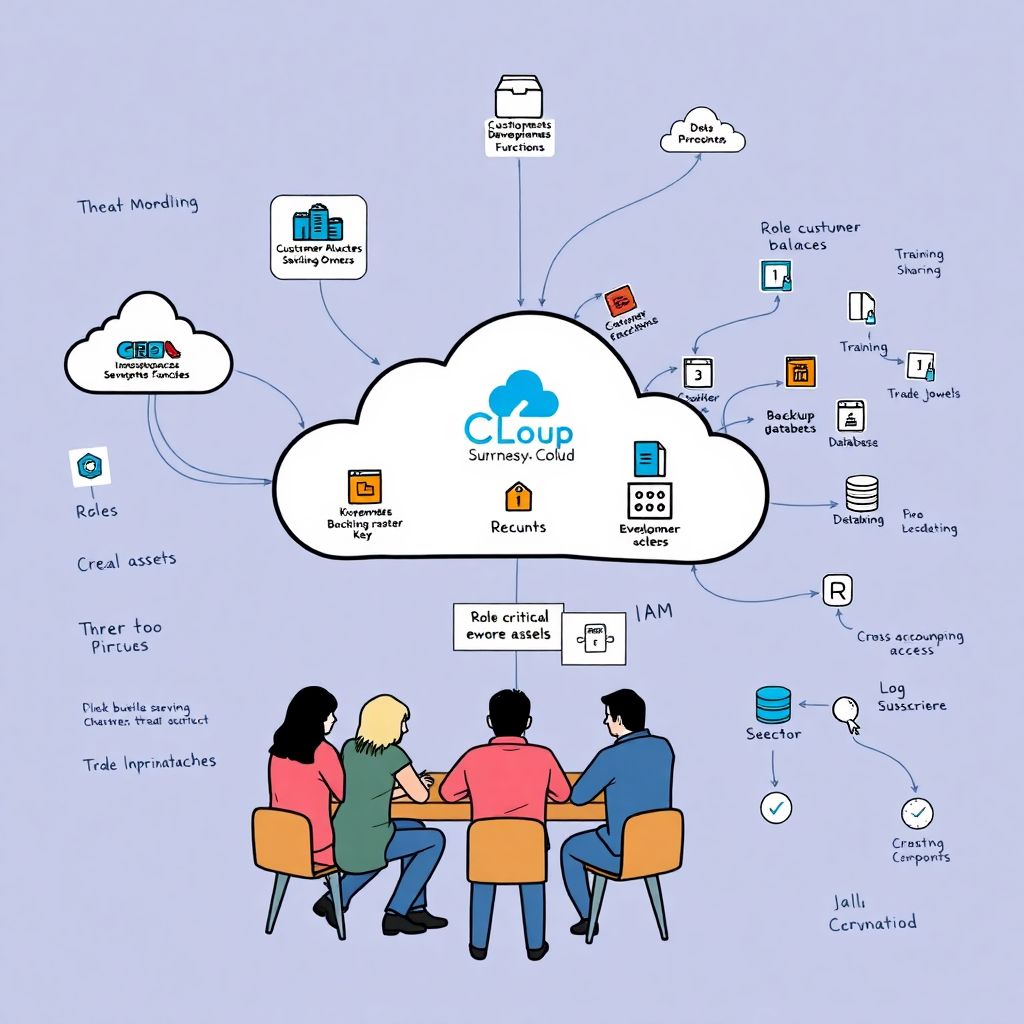
A practical model starts with brutal clarity about business impact, not with a pretty architecture diagram. First, map the crown‑jewel assets: customer balances, signing keys, training datasets, trade algorithms. Then describe, in plain language, which cloud services see or transform these assets and in which regions and accounts they live. Only after that should you sketch data flows and trust boundaries. When you ask como criar modelo de ameaças para workloads em nuvem, the key is to keep diagrams ugly but faithful and to annotate them with assumptions: where you rely on provider isolation, what identity federation does, and which components are ephemeral. Every future security decision will lean on those assumptions, so they must be visible and challengeable.
Non‑obvious attack paths in distributed cloud architectures

Traditional STRIDE‑style thinking catches SQL injection and broken auth; modern distributed designs introduce quieter routes. Cross‑account access via mismanaged roles can turn a dev account into a stepping stone into production. Shadow APIs exposed for internal tooling become entry points once a partner VPN is compromised. Data‑processing workloads that temporarily store decrypted blobs on worker nodes quietly bypass envelope encryption designs. In the last few years, incident post‑mortems repeatedly show attackers abusing control‑plane features (like snapshot sharing or log subscription) rather than smashing the front door. For effective threat modeling em cloud para arquiteturas distribuídas, you must deliberately walk through the control plane, IAM graph, and backup processes, not just the request path of customer traffic.
Alternative methods beyond classic STRIDE and checklists
While STRIDE and attack trees remain useful, they tend to nudge teams into producing thick documents that nobody reads twice. An alternative is scenario‑based modeling anchored in “abuse stories”: narrative descriptions of how a specific adversary would monetize a weakness in your workloads. Another underrated method is adversary‑driven mapping: start from real TTPs observed in frameworks like MITRE ATT&CK for Cloud and ask which are even possible in your setup. Red and blue teams in tech‑savvy organizations have increasingly used “threat‑in‑motion” exercises, where they replay a known breach from the last three years against a live staging environment. These approaches keep models living and testable instead of fossilized into compliance artifacts that never influence architectural choices.
Tools that help (and where they silently mislead)
Many teams rush to adopt ferramentas de threat modeling para cloud computing expecting automated diagrams to equal insight. Tools that ingest IaC templates and cloud configs are great at spotting missing encryption flags or public buckets, and they can highlight data flows you forgot you had. But they often miss business‑logic risks and cross‑provider chains, especially in hybrid or edge‑heavy setups. Use automation to cover breadth and hygiene, then layer human, contextual analysis on top. A productive pattern is to let tools generate an initial model, have architects and engineers correct it during a workshop, and then re‑feed those corrections as guardrails in CI. That loop prevents tools from drifting into false confidence while still scaling your coverage.
Multi‑cloud reality: practices that age well
Multi‑cloud is rarely about strategy and almost always about history: acquisitions, regional latency demands, or pricing pushes you there. In this chaos, melhores práticas de segurança e threat modeling em ambientes multi-cloud revolve around normalization. Normalize identity by introducing a central identity provider and mapping cloud‑native roles to human‑readable personas. Normalize logging by enforcing a minimal event schema across providers and sending it into one analytics plane. Normalize your threat categories: data exfiltration, control‑plane takeover, supply‑chain compromise, tenant breakout. With that baseline, every new workload triggers the same modeling routine, regardless of its cloud logo, and you can compare risks meaningfully instead of juggling three incompatible vocabularies in every design review.
Consulting versus in‑house: making expertise actually stick
Bringing in consultoria em threat modeling para aplicações em nuvem can speed‑run maturity, but it often degenerates into a pile of PDF reports and a few impressive diagrams. To avoid that, tie consultants’ work to concrete rituals: architecture review gates, incident‑response playbooks, backlog items. Ask explicitly for reusable threat libraries specific to your domains, not generic “web app” lists. Over the last years, organizations that reported durable gains were those that required joint sessions where product owners, SREs and developers co‑created models instead of being presented with polished outcomes. The goal is not to “own” a document; it is to embed a habit where teams instinctively sketch threats whenever they draw a new microservice or tweak data flows.
Professional tricks: making models fast, honest and revisitable
Seasoned practitioners avoid two extremes: endless workshops and one‑off exercises. A useful trick is the “90‑minute threat model”: constrain the session for a given service to that slot, forcing participants to prioritize only top abuse stories and critical assets. Another pro move is versioning models alongside code, treating them as first‑class artifacts updated with every major architectural change. You can also predefine a small set of “threat canvases” for typical patterns like public‑facing APIs, asynchronous data pipelines or internal admin tools, so engineers start from a tailored template instead of a blank page. These habits keep threat modeling lean enough that busy teams willingly engage with it rather than postponing it indefinitely.
Non‑obvious safeguards that pay off disproportionately
Some of the most effective defenses in distributed cloud setups look almost boring on the surface. Explicitly modeling and then restricting data egress paths—who can send data where and under which conditions—has prevented several high‑impact leaks documented since 2021. Investing in strong workload identity and short‑lived credentials closes many of the lateral movement scenarios that keep reappearing in incident reports. Another subtle but powerful safeguard is modeling dependency trust: internal services must declare which other services they are willing to trust by policy, not by default network reachability. When your threat models force you to answer “why should this service trust that one?”, many implicit, dangerous assumptions quickly surface and can be retired before attackers exploit them.
Measuring success: from diagrams to reduced incident impact
Threat modeling only matters if it changes behavior and metrics. Over the past few years, mature organizations have tracked outcomes like reduction in high‑severity misconfigurations found late in pen tests, faster containment times during cloud incidents, and fewer emergency hotfixes after new services launch. Teams that integrated models into their SDLC typically reported a visible drop in critical findings during third‑party assessments within one to two release cycles. You do not need perfect models to see value; you need just enough structure so that every new workload in the cloud launches with an explicit, reviewed story of how it might be attacked and what you are doing about it—before reality writes a more painful version of that story.