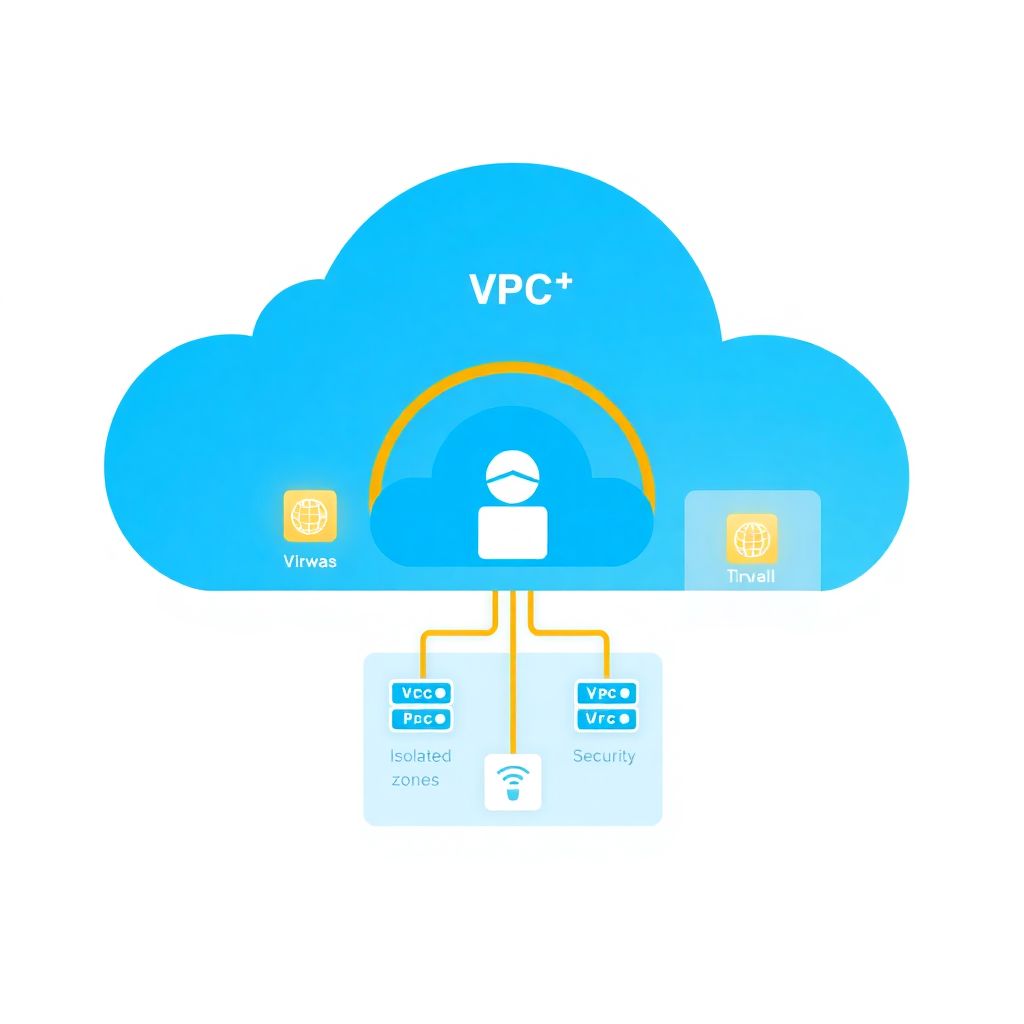
Effective VPC/VNet segmentation means splitting your cloud network into clearly scoped zones (prod/non‑prod, tiers, shared services) with least‑privilege traffic between them. You combine subnets, route tables, firewalls, security groups and microsegmentation policies to reduce blast radius. Start simple, automate everything, and tighten rules iteratively with good logging.
Pillars of effective VPC/VNet segmentation
- Design VPC/VNet boundaries by business domain, environment and compliance needs, not only by project.
- Use separate subnets and route tables for internet, partner and internal traffic flows.
- Centralize ingress/egress with firewalls and dedicated inspection VPCs/VNets.
- Harden security groups/NSGs as the primary workload filter and keep them stateful.
- Adopt microsegmentation with tags/labels and identity, not just IPs and ports.
- Automate enforcement with Infrastructure as Code and security policies as code.
- Continuously monitor logs, flows and events to tune rules and detect drift.
Designing VPC/VNet boundaries and subnet topology
In practice, “segmentação de rede em VPC como implementar” starts with choosing the right number of VPCs/VNets and how they connect. Over‑segmenting increases operational overhead; under‑segmenting increases blast radius. The right balance depends on your environments, data sensitivity and organizational structure in Brazil (pt_BR context) and beyond.
Typical baseline:
- Separate VPCs/VNets per environment: prod, non‑prod, maybe shared‑services.
- Use separate accounts/subscriptions/projects for strong isolation of regulated workloads.
- Standardize CIDR ranges, avoiding overlap between regions and clouds (AWS, Azure, GCP).
Compare ease vs risk:
- Fewer, larger VPCs/VNets: easier peering and routing, but a misconfigured rule can expose more assets.
- More, smaller VPCs/VNets: harder to manage, but compromise is more contained (preferred for critical or payment workloads).
A common topology for microsegmentação em nuvem AWS Azure melhores práticas is three subnet types per VPC/VNet:
- Public (only for load balancers, bastions, API gateways).
- Private‑app (application and API tiers, no direct internet).
- Private‑data (databases, caches, message brokers).
Basic examples by cloud:
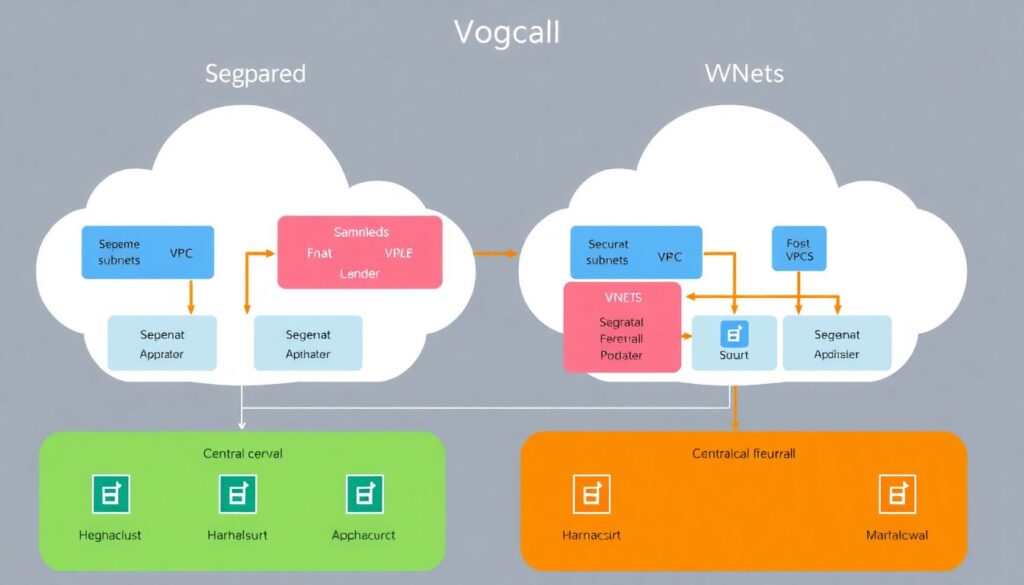
- AWS: one VPC per environment, subnets split by AZ and tier (public, private‑app, private‑data), peered to a shared security VPC with inspection appliances.
- Azure: one hub VNet with Azure Firewall and VPN/ExpressRoute, multiple spoke VNets (prod‑app, prod‑data, dev‑app) peered via hub‑and‑spoke.
- GCP: Shared VPC in a host project, separate service projects for prod and non‑prod, subnets per region and tier.
| Cloud | Core isolation construct | Typical use | Risk if mis‑designed |
|---|---|---|---|
| AWS | VPC + subnet + security group | Environment and tier separation | Flat VPC can expose many apps via one bad SG rule |
| Azure | VNet + subnet + NSG | Hub‑and‑spoke with central firewall | Over‑reused NSGs allow lateral movement between spokes |
| GCP | VPC + subnet + firewall rules | Shared VPC for multi‑project governance | Project‑wide rules accidentally open all subnets |
Minimal AWS example to create clearly separated subnets:
aws ec2 create-vpc --cidr-block 10.10.0.0/16
aws ec2 create-subnet --vpc-id vpc-123 --cidr-block 10.10.1.0/24 # public
aws ec2 create-subnet --vpc-id vpc-123 --cidr-block 10.10.2.0/24 # app
aws ec2 create-subnet --vpc-id vpc-123 --cidr-block 10.10.3.0/24 # data
Network ACLs, security groups and perimeter enforcement
Once boundaries are set, the next question is como configurar políticas de segurança e firewall em VPC e VNet so that rules are enforceable and maintainable. Focus on stateful workload‑level controls first (security groups, NSGs, GCP firewall rules) and use stateless NACLs only for coarse filtering or special cases.
-
Use NACLs sparingly for coarse subnet boundaries
NACLs are stateless and evaluated before security groups/NSGs. Use them for simple deny‑lists, such as blocking known bad IP ranges or enforcing “no internet” on data subnets.# AWS NACL example: block inbound RDP to private subnets aws ec2 create-network-acl-entry --network-acl-id acl-123 --rule-number 100 --protocol tcp --rule-action deny --ingress --port-range From=3389,To=3389 --cidr-block 0.0.0.0/0 -
Rely on security groups/NSGs as the main segmentation tool
They are stateful and attached to NICs or instances, which simplifies microsegmentation. Design them per role (web, app, db) instead of per individual VM/container.# AWS SG: allow app->db only on 5432 aws ec2 authorize-security-group-ingress --group-id sg-db --protocol tcp --port 5432 --source-group sg-app -
Centralize north‑south traffic through dedicated firewalls
Place an AWS Network Firewall, Azure Firewall, or GCP Cloud Firewall / third‑party appliance in a shared security VPC/VNet for all internet and partner connectivity. This is where many serviços de consultoria em segmentação de VPC e VNet focus first, because mis‑secured edges are high‑impact. -
Define explicit default‑deny posture
For each tier, ensure inbound rules default to “deny” and only allow specific sources and ports. Outbound rules should also be constrained, especially from app tiers to internet.# Azure NSG: deny internet egress from data subnet az network nsg rule create --nsg-name nsg-data --resource-group rg-prod --name DenyInternetEgress --priority 200 --direction Outbound --access Deny --protocol '*' --source-address-prefixes 10.20.3.0/24 --destination-address-prefixes Internet --destination-port-ranges '*' -
Compare enforcement trade‑offs across clouds
AWS security groups are purely allow‑lists; Azure NSGs and GCP firewall rules support explicit denies. This changes how you model block rules. Use labels (GCP) and application security groups (Azure) to avoid IP‑centric rules wherever possible. -
Log and test before tightening
Enable VPC Flow Logs (AWS), NSG Flow Logs (Azure), and VPC Flow Logs (GCP) before aggressive lockdown. In Brazil‑focused teams, ensure logs are sent to centralized SIEM that complies with LGPD and local retention needs.
Applying microsegmentation: workload-level policy models
Microsegmentation reduces lateral movement inside a VPC/VNet by enforcing fine‑grained policies between workloads, often using identity, tags or labels. Compared to coarse segmentation, it is more secure but harder to operate without automation and proper ferramentas de segurança para microsegmentação em VPC e VNet.
Typical scenarios and approaches:
-
Tier‑based segmentation (simple, easier to adopt)
Problem: Web servers should talk to app servers, but not directly to databases or other environments.
Recommended: Security groups/NSGs per tier and explicit allow rules between them, with no “* to *” anywhere.
Example:# GCP: allow app to db by network tag gcloud compute firewall-rules create app-to-db --direction=INGRESS --action=ALLOW --rules=tcp:5432 --source-tags=app --target-tags=db -
Environment isolation (prod vs non‑prod)
Problem: Dev/test workloads often run vulnerable versions and must not reach prod data.
Recommended: Separate VPCs/VNets and accounts/subscriptions with no direct peering, or tightly controlled transit with strong firewalls and inspection. Microsegmentation ensures even if peered, only limited APIs are reachable. -
Application‑centric segmentation (tags/labels, preferred for scale)
Problem: IP addresses are dynamic and ephemeral (auto‑scaling groups, AKS/EKS/GKE).
Recommended: Use application tags (Azure ASGs), AWS resource tags + SGs, and GCP network tags/labels so policies follow the workload identity.# Azure: NSG rule using Application Security Group az network asg create -g rg-prod -n asg-app az network nsg rule create -g rg-prod --nsg-name nsg-db --name AllowAppToDb --priority 100 --direction Inbound --access Allow --source-asgs asg-app --destination-port-ranges 1433 --protocol Tcp -
Zero‑trust service‑to‑service policies
Problem: Even inside the same subnet, compromised workloads pivot laterally.
Recommended: mTLS and identity‑based policies (service accounts, managed identities, SPIFFE IDs). Combine with network policies (for Kubernetes: Calico/Cilium/Azure Policy for AKS/GKE Autopilot) to limit pod‑to‑pod communication. -
Partner and B2B integrations
Problem: External partners connected via VPN/Direct Connect/ExpressRoute should reach only specific APIs.
Recommended: Dedicated “partner” subnets and SGs/NSGs that allow only API gateway endpoints, never raw app or database ports. Many serviços de consultoria em segmentação de VPC e VNet start engagements by mapping these overly broad partner connections. -
High‑risk data zones
Problem: PCI, healthcare or personal data under LGPD require strict isolation.
Recommended: Dedicated VPC/VNet per regulatory boundary, limited peering, encrypted traffic, and microsegmentation that only exposes the minimal required services (tokenization APIs, not raw databases).
Managing east‑west traffic: service mesh, proxies and sidecars
Microsegmentation is incomplete without controlling east‑west traffic between services. Service meshes, L7 proxies and sidecars add powerful controls but also complexity. Choose the lightest mechanism that achieves your security objectives and fits your team’s operational maturity.
Advantages of meshes, proxies and sidecars
- Consistent mTLS enforcement across clusters and clouds (Istio, Linkerd, AWS App Mesh, Azure Application Gateway Ingress, GCP Anthos Service Mesh).
- L7‑aware policies (HTTP methods, paths, headers) instead of only IP/port rules, reducing false positives.
- Central traffic visibility with standardized metrics and traces per service, critical for tuning segmentation policies.
- Gradual rollout and canary features that help you test stricter policies before enforcing them globally.
- Cross‑cloud abstraction for hybrid AWS/Azure/GCP traffic, simplifying governance in multinational or pt_BR‑centric enterprises.
Limitations and risks to consider
- Operational overhead: meshes introduce new control planes, CRDs and failure modes that intermediate teams may struggle to run.
- Latency and resource use: sidecars consume CPU/memory; enforcing many L7 rules can affect p95 latency.
- Misconfigured policy risk: centralized policies can accidentally block critical east‑west traffic and cause outages.
- Overlapping controls: duplicated rules between mesh and SGs/NSGs complicate troubleshooting (you must define clear ownership).
- Compliance interpretation: regulators may still demand low‑level network segmentation even if L7 controls are strong.
# Example: Istio AuthorizationPolicy to restrict traffic to a service
apiVersion: security.istio.io/v1beta1
kind: AuthorizationPolicy
metadata:
name: allow-api-from-web
namespace: prod
spec:
selector:
matchLabels:
app: api
rules:
- from:
- source:
principals: ["cluster.local/ns/prod/sa/web-sa"]
Automation and IaC patterns for reproducible segmentation
Segmentation only works long‑term if it is reproducible and version‑controlled. Terraform, AWS CloudFormation, Azure Bicep and GCP Deployment Manager make it easier to codify VPC/VNet designs, but there are recurring mistakes and myths that increase risk.
-
Myth: “We can design VPCs/VNets manually first, IaC later”
This leads to drift and undocumented exceptions. Define at least the core network (VPC/VNet, subnets, route tables, security groups/NSGs) in code from day one. -
Error: Copy‑pasting overly permissive rules
Terraform modules that embed 0.0.0.0/0 “temporary” rules quickly spread across environments. Always parameterize CIDRs and ports and set safe defaults that force explicit overrides. -
Myth: “More modules automatically means better design”
Over‑modularization hides security logic and makes reviews harder. Prefer a few well‑documented modules that expose key segmentation decisions as inputs. -
Error: Not validating plans with policy‑as‑code
Without tools like Open Policy Agent (OPA), AWS Config, Azure Policy or GCP Organization Policy, unsafe changes slip into production. Integrate checks into CI before apply. -
Myth: “Tools replace security architecture”
Even the best ferramentas de segurança para microsegmentação em VPC e VNet cannot compensate for a poor conceptual model. Start from trust boundaries, data flows and blast radius, then encode that model in code and tools. -
Error: Ignoring multi‑cloud differences
Cloning AWS patterns into Azure/GCP without adaptation causes surprises (for example, explicit deny semantics, default egress behavior). Document cloud‑specific nuances in your modules.
# Terraform snippet: minimal VPC segmentation pattern (simplified)
module "vpc" {
source = "./modules/vpc"
name = "prod"
cidr = "10.30.0.0/16"
public_subnets = ["10.30.1.0/24"]
app_subnets = ["10.30.2.0/24"]
data_subnets = ["10.30.3.0/24"]
enable_flowlogs = true
}
Visibility, logging and operational response for segmented networks
Segmentation reduces attack surface but also complicates troubleshooting. Without strong observability and clear runbooks, teams may respond to incidents by randomly opening firewalls, undoing hard‑won security. A simple, well‑practiced workflow avoids that risk.
Mini case: a Brazilian fintech migrates to AWS with strict microsegmentation and soon hits intermittent payment API failures. Engineers suspect SG rules and temporarily widen them, accidentally exposing the API to the internet.
Improved approach:
- Enable flow logs and send them to a central analytics stack (CloudWatch Logs + Athena, Azure Log Analytics, GCP Cloud Logging) with dashboards per segment.
- Define escalation runbooks that instruct engineers how to use logs to validate whether traffic is blocked by SG/NSG, NACL, mesh policy or app logic.
- Allow only time‑bounded emergency overrides, applied via IaC with automatic rollback and audit trail.
# Example: query AWS VPC Flow Logs (Athena) to see blocked traffic
SELECT srcaddr, dstaddr, dstport, action, count(*) AS hits
FROM vpc_flow_logs
WHERE dstport = 443
AND action = 'REJECT'
AND dstaddr = '10.30.3.25'
GROUP BY srcaddr, dstaddr, dstport, action
ORDER BY hits DESC;
Checklist ending for self‑assessment:
- Have you clearly documented which VPCs/VNets exist, why, and how they connect?
- Are all security groups/NSGs and firewalls default‑deny with only necessary ports and sources allowed?
- Do microsegmentation policies rely on identities/tags instead of static IPs wherever possible?
- Is segmentation defined and reviewed via IaC and policy‑as‑code before deployment?
- Can your team trace and fix blocked traffic using logs and runbooks without broad “allow all” changes?
Practical answers to recurring segmentation issues
How many VPCs or VNets should I create for a medium‑size environment?
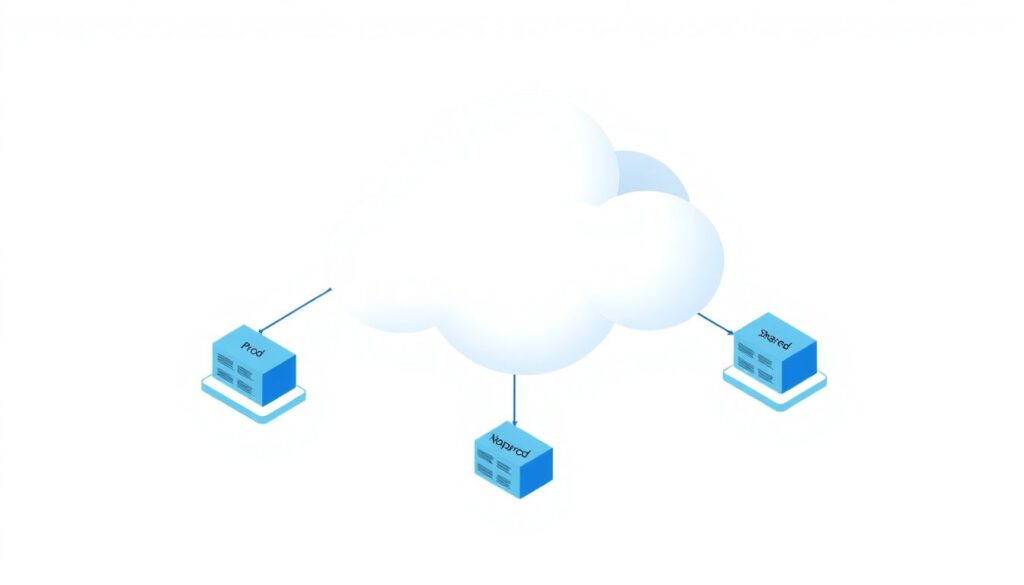
Start with at least separate VPCs/VNets for prod, non‑prod and shared services. Add more only when you have clear reasons such as regulatory isolation, very noisy tenants or strong blast‑radius requirements. Fewer, well‑segmented networks are easier to operate than many poorly designed ones.
Where do I start with microsegmentation in AWS, Azure and GCP?
Begin with tier‑based security groups/NSGs or firewall rules (web, app, data) and enforce least privilege between tiers. Then gradually introduce identity‑ or tag‑based rules and, if needed, a service mesh for critical services. Avoid jumping straight into complex meshes without mastering basic SG/NSG hygiene.
How do I avoid breaking applications when tightening segmentation?
First, enable flow logs everywhere and capture current allowed traffic. Simulate new rules in a staging environment or with monitoring‑only policies if available. Roll out stricter rules gradually, monitoring for rejects and having a documented rollback plan, instead of bulk changes in production.
Should I use NACLs heavily for microsegmentation?
No. NACLs are best for coarse subnet boundaries and rare special cases. For microsegmentation, prioritize stateful, workload‑attached controls such as security groups, NSGs and identity‑based or tag‑based policies. Overusing NACLs makes troubleshooting harder and usually adds risk without real benefit.
When does a service mesh make sense for segmentation?
A service mesh is worth its complexity when you have many services, strict compliance, and a need for consistent mTLS and L7 policies across clusters and clouds. For smaller or simpler environments, start with basic network and application‑level controls before adopting a mesh.
How can I integrate segmentation with CI/CD pipelines?
Define VPC/VNet, subnet and firewall configurations as code and run policy‑as‑code checks in CI before deployment. Require peer review for segmentation changes and use separate pipelines or stages for prod vs non‑prod. This keeps changes auditable and reduces the chance of accidental exposure.
Do I need external consulting services to design segmentation?
Smaller teams can start with cloud reference architectures and internal security reviews. As complexity grows, specialized serviços de consultoria em segmentação de VPC e VNet can help validate the design, model threats and tune policies, especially for regulated or multi‑cloud environments.