Container and Kubernetes security means controlling risks across images, runtime, cluster and network: from Dockerfile basics and RBAC to admission controls, scanning and incident response. In a Brazilian pt_BR context, you can reach strong segurança em containers docker and segurança em kubernetes em produção even with limited budget, using open source tools and managed services wisely.
Essential security highlights for containerized environments
- Define a clear threat model for each application and environment (dev, staging, production).
- Secure the full image lifecycle: Dockerfile, build pipeline, scanning and signing.
- Harden runtime: isolation, least privilege, enforced policies and read-only filesystems.
- Apply melhores práticas de segurança em kubernetes: RBAC, admission controllers, secrets and upgrades.
- Segment the network with CNI policies, service mesh and zero-trust principles.
- Continuously monitor logs, metrics and audit trails and test incident response playbooks.
- Leverage ferramentas de segurança para kubernetes e containers and serviços gerenciados de segurança para containers e kubernetes when team or budget is constrained.
Threat modeling and risk assessment for container workloads
Threat modeling for container workloads is a structured way to understand how an attacker could abuse your images, registries, Kubernetes cluster and underlying infrastructure. Instead of securing everything equally, you identify critical assets, trust boundaries and the most likely abuse paths.
In practice, you map the application architecture (microservices, databases, message queues), the Kubernetes resources (namespaces, ServiceAccounts, Ingress, NetworkPolicy) and the external dependencies (cloud services, CI/CD, registry, VPN). For Brazilian teams, this often includes on-prem clusters plus cloud providers like AWS, Azure or GCP.
Then you walk through typical threat categories: compromised developer laptop, poisoned base image, leaked CI credentials, misconfigured RBAC, exposed dashboard, breakout from container to node, and lateral movement inside the cluster. Tools like STRIDE or simple attack trees help structure this discussion without requiring a security PhD.
Risk assessment comes from combining likelihood and impact. A small startup running non-sensitive workloads might accept some risks that a fintech or health company in Brazil cannot. Document 5-10 top risks per application, define minimal mitigations for each, and review them when you change architecture or when there is a new high-profile Kubernetes vulnerability.
Secure image lifecycle: build pipelines, scanning, and hardening
Securing the image lifecycle is about controlling what goes into your container images, how they are built, how you verify them, and how you keep them up to date. This is the foundation of segurança em containers docker and applies equally to other runtimes like containerd and CRI-O.
-
Start from minimal, trusted base images
- Prefer distro-less or minimal images (for example,
gcr.io/distroless/base, Alpine with care, vendor-provided slim images). - Pin versions explicitly in your Dockerfile and avoid
latest. - For low-resource teams, at least standardize a small set of vetted base images used across all projects.
- Prefer distro-less or minimal images (for example,
-
Harden Dockerfiles and build configurations
- Use multi-stage builds to keep tooling (compilers, package managers) out of the final image.
- Run as non-root: add a dedicated user and use
USER app. - Avoid copying entire folders blindly; use
.dockerignoreto exclude secrets, Git metadata and temporary files.
-
Enable image scanning in CI/CD
- Integrate scanners like Trivy, Grype or Clair into your pipeline.
- Fail builds on high-severity vulnerabilities or at least add a manual approval step.
- If CI minutes are expensive, schedule nightly scans of images already in the registry and open tickets automatically.
-
Sign images and verify provenance
- Use Sigstore Cosign or Notary v2 to sign images during CI.
- Store signatures in the registry and enforce verification via admission controllers in Kubernetes.
- For smaller teams, start by signing only production images from main branches, then expand coverage.
-
Keep images patched and reduce lifetime
- Rebuild images regularly to pick up base image security fixes.
- Tag images immutably (for example,
app:1.3.2) rather than overwriting tags, and clean up unused images from the registry. - Use automation (for example, Renovate, Dependabot) to open pull requests when base images or dependencies have new versions.
-
Restrict registries and image sources
- Allow pods to pull only from approved registries (private registry, ECR, GCR, ACR).
- Block public Docker Hub usage in production unless the image is mirrored and vetted.
- On constrained environments, at least run a local registry cache and manually vet public images that you mirror.
Runtime protection: isolation, least privilege, and policy enforcement
Runtime protection is about how containers behave once they are running: what they can access, how isolated they are, and which security policies protect the host and the network. This is central to segurança em kubernetes em produção, especially when workloads are multi-tenant or Internet-facing.
-
Isolation at the container and node level
- Disable privileged containers and hostPath mounts unless there is a clear, documented need.
- Use Pod Security Admission (or legacy PodSecurityPolicy replacement) to enforce baseline and restricted profiles.
- For workloads with different trust levels, use separate node pools and taints/tolerations to avoid noisy neighbor risks.
-
Least privilege for Linux capabilities and filesystem
- Drop default Linux capabilities with
securityContext.capabilities.drop: ["ALL"]and add only what you need. - Mount root filesystem as read-only and use separate writable volumes only when required.
- For stateful workloads where full read-only is hard, at least protect sensitive paths like
/etcand/var/run.
- Drop default Linux capabilities with
-
Policy as code with admission controllers
- Use Kyverno or OPA Gatekeeper to encode rules: no privileged pods, required labels, approved registries, resource limits.
- Start with audit mode to see violations, then switch to enforce mode for production namespaces.
- In smaller teams, maintain a shared policy library and apply it via GitOps (Argo CD, Flux) for consistency.
-
Runtime detection and response
- Deploy tools like Falco, Cilium Tetragon or eBPF-based agents to detect suspicious syscalls and behavior.
- Send alerts to a central system (for example, Grafana, ELK, Loki, Datadog) and define clear triage playbooks.
- If resources are limited, focus on a small set of rules: unexpected outbound connections, shell spawned in containers, writes to sensitive directories.
-
Secret management and access control
- Avoid embedding secrets into images or environment variables checked into Git.
- Use Kubernetes Secrets with envelope encryption, or integrations with KMS/HashiCorp Vault/Secrets Manager.
- Restrict which ServiceAccounts can read which secrets via RBAC and limit their token usage.
Kubernetes cluster hardening: control plane, RBAC and admission controls
Kubernetes cluster hardening focuses on protecting the API server, etcd, kubelet and the configuration that governs who can do what. Done correctly, this becomes one of the melhores práticas de segurança em kubernetes and prevents many real incidents (for example, attackers using anonymous access or over-privileged accounts).
Benefits of a hardened Kubernetes control plane
- Reduces attack surface by closing unauthenticated or unused API endpoints and dashboards.
- Limits blast radius: compromised ServiceAccounts or kubeconfigs cannot control the entire cluster.
- Improves compliance posture for regulations that require least privilege and audit trails.
- Enables safer multi-team and multi-namespace environments across Brazilian squads and external partners.
- Makes it easier to adopt advanced tooling (for example, policy engines, service mesh) on top of a secure foundation.
Limitations and practical constraints to consider
- Complexity overhead: fine-grained RBAC and admission policies require maintenance and good documentation.
- Risk of self-inflicted outages if policies block critical system components or core workloads.
- Not all managed Kubernetes offerings expose every control plane setting, especially in low-cost tiers.
- Some add-ons or legacy tools expect broad permissions, which can conflict with strict RBAC designs.
- Teams with few engineers may struggle to keep up with control plane upgrades and API deprecations.
To balance benefits and limitations, start with managed control planes where possible (EKS, GKE, AKS, or local Brazilian providers) and focus your effort on RBAC, namespaces, and admission controls you can fully manage. When you cannot tune everything, prioritize disabling anonymous access, protecting etcd, and enforcing minimal ServiceAccount roles.
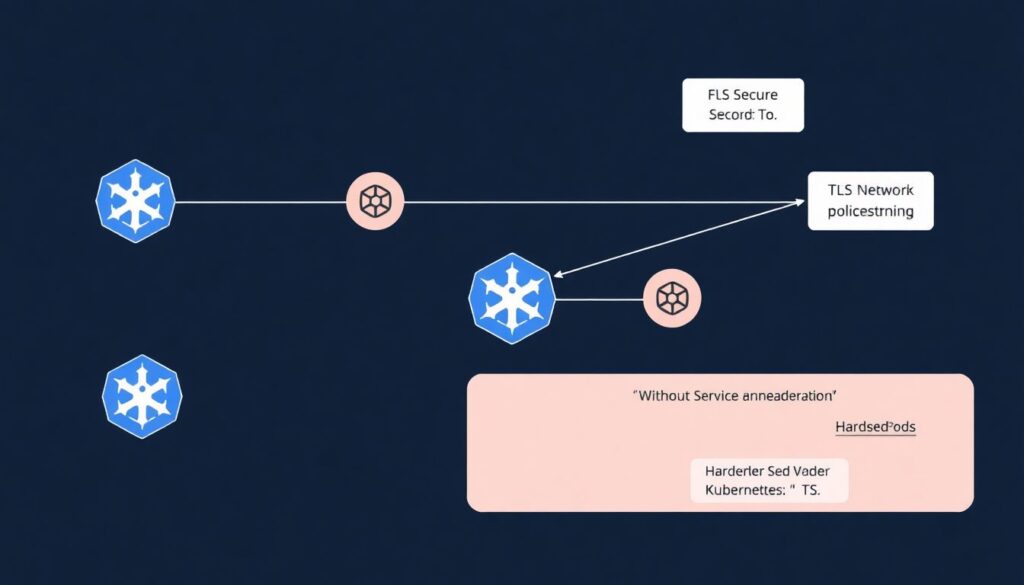
Network defenses: CNI choices, service mesh, and microsegmentation
Network security for containers and Kubernetes covers pod-to-pod traffic, ingress/egress, DNS, and external dependencies. It is common to overestimate what the default CNI provides and to underestimate the value of explicit NetworkPolicy and, when appropriate, service mesh.
Typical mistakes and myths include the following.
-
"The VPC or on-prem firewall is enough"
Perimeter firewalls do not see internal pod-level communication. Without NetworkPolicies, any pod in a namespace can usually talk to any other, which undermines zero-trust designs.
-
"Any CNI plugin automatically gives security"
Basic CNI implementations only provide connectivity. To get microsegmentation, you need NetworkPolicy support and explicit policies. Evaluate CNIs like Calico, Cilium or Weave Net based on your security requirements, not just installation simplicity.
-
"Service mesh is overkill for small teams"
Service mesh (for example, Istio, Linkerd, Kuma) does add complexity, but for TLS everywhere, traffic policies, and observability it can replace much custom code. Resource-constrained teams might start with mesh only for Internet-facing or highly sensitive namespaces.
-
"Allow-all NetworkPolicies are a good starting point"
Starting with allow-all policies negates their purpose. Better patterns: default deny per namespace plus allow rules per service. Implement gradually, starting with new apps where you know traffic flows.
-
"DNS and egress are not security concerns"
Many exfiltration paths use DNS or unrestricted egress. Control DNS queries where possible and restrict outbound traffic to necessary domains or CIDRs with egress policies, cloud provider egress controls, and firewall rules.
-
"Managed ingress controller means managed security"
Cloud-managed load balancers help, but misconfigured Ingress resources remain a major risk. Use TLS everywhere, strict host/path routing, and WAF where possible. For Brazilian production clusters, this is often a quick win for segurança em kubernetes em produção.
Monitoring, incident response and compliance for production systems
Production-ready security requires continuous visibility and the ability to respond quickly when something goes wrong. This is where many teams realize they need both internal tools and, often, serviços gerenciados de segurança para containers e kubernetes to extend coverage without adding headcount.
Consider a mini-case of a Brazilian fintech running a Kubernetes cluster for payment APIs:
-
Monitoring and log collection
- Deploy Prometheus and Grafana for cluster and application metrics.
- Use Fluent Bit or Fluentd to ship logs to Loki or Elasticsearch; tag logs with namespace, app, pod and node.
- Enable Kubernetes audit logs and send them to a central store as well.
-
Detection and alerting pipeline
- Configure alert rules for suspicious auth events (for example, many failed logins to the API server), high error rates and runtime security alerts from tools like Falco.
- Integrate alerts with Slack, email, or an incident management platform.
- For low-budget setups, start with a minimal set of alerts on ingress error rate, CPU spikes and pod restarts.
-
Incident response workflow
- Define playbooks: who is on-call, how to isolate a namespace, how to revoke a compromised token, how to rotate secrets.
- Use namespace-level network restrictions or temporarily scale pods to zero to contain suspicious workloads.
- Keep a script or runbook to collect forensic data:
kubectl describe pod,kubectl logs, node-level logs, and relevant cloud provider events.
-
Compliance and audit requirements
- Map regulatory requirements (for example, LGPD, PCI-DSS for payments) to concrete Kubernetes controls (RBAC, encryption, logging retention).
- Automate evidence collection: store policies as code in Git, keep change history, and generate periodic compliance reports.
- If internal expertise is limited, combine your tooling with managed SOC or cloud-native security services that specialize in compliance reporting.
-
Resource-conscious alternatives
- Use cloud-managed logging and monitoring instead of self-hosting when total cost, including operations, is lower.
- Adopt lightweight agents (for example, node-exporter, eBPF-based tools) instead of heavy sidecars for each pod.
- Regularly re-evaluate which dashboards and alerts are truly useful to reduce noise and maintenance effort.
Compact self-checklist for container and Kubernetes security
- Do all production images come from minimal, trusted bases, scanned and built in CI with non-root users?
- Are RBAC, namespaces and admission controllers enforcing least privilege and blocking dangerous pod specs?
- Do you have NetworkPolicies applied and tested for at least your most critical namespaces?
- Are secrets managed outside images and Git, with rotation procedures defined and documented?
- Can you detect and respond to a suspicious pod within minutes, using documented runbooks and working alerts?
Practical clarifications on container and Kubernetes security
How is container security different from traditional VM security?
Containers share the host kernel, so isolation is weaker than with full VMs. You secure images, orchestrator configuration and runtime behavior instead of only hardening the OS. Kubernetes adds an API-driven control plane and multi-tenant scheduling challenges not present in simple VM setups.
Do I need a service mesh to be secure in production?
No, a service mesh is not mandatory for segurança em kubernetes em produção. You can achieve strong security with basic tools: TLS termination at ingress, strict NetworkPolicies, and hardened workloads. Mesh becomes attractive when you need mTLS everywhere, advanced traffic policies and rich observability.
Which security tools are essential for a small Kubernetes team?
As a minimum, use an image scanner in CI, Kubernetes RBAC, some form of policy engine (Kyverno or Gatekeeper), and centralized logging and metrics. From there, you can add runtime detection like Falco and more advanced ferramentas de segurança para kubernetes e containers as your maturity grows.
Are managed Kubernetes services more secure than self-managed clusters?

Managed services usually provide a hardened control plane, automatic upgrades and built-in security integrations. However, you are still responsible for workload configuration, RBAC, NetworkPolicies and secrets. Serviços gerenciados de segurança para containers e kubernetes can help but do not replace secure design and good operational practices.
How can I improve security without increasing cloud costs too much?
Prioritize configuration changes over new products: restrict RBAC, enable Pod Security Admission, use minimal images and enforce NetworkPolicies. Reuse existing observability stacks for security alerts and adopt open source tools instead of heavy commercial platforms when budgets are tight.
Should every container run as non-root?
Yes in almost all cases. Running as non-root reduces the impact of a container escape or application compromise. Only a few system-level workloads truly require root; for them, document the justification and add extra protections like dedicated nodes and stricter monitoring.
How often should I update base images and dependencies?
Update whenever there are security fixes for your base images or critical libraries and rebuild images regularly. Automated dependency update tools can open pull requests as soon as new versions are available, but you still need tests and a safe rollout strategy.