Categoria: Manuais
-

Siem and Soar integration with cloud providers: architecture and use cases
SIEM-SOAR cloud integration means centralizing security telemetry from AWS, Azure and GCP into a SIEM, then using SOAR to automate triage and response with safe, well‑scoped actions. For teams in Brazil, start small with high‑value use cases, enforce least privilege, test playbooks in “dry‑run” mode, and continuously tune detections. Concise technical summary of SIEM-SOAR cloud…
-

Security by design in cloud Ci/cd pipelines: how to implement secure workflows
To implement security by design in cloud CI/CD pipelines, start by treating the pipeline itself as a high-value production system. Model threats, harden architecture with least privilege, secure secrets and artifacts, add automated checks (SAST/SCA), and continuously monitor. Align choices with your cloud provider, existing tools, and team skill set. Foundational principles for security-by-design in…
-
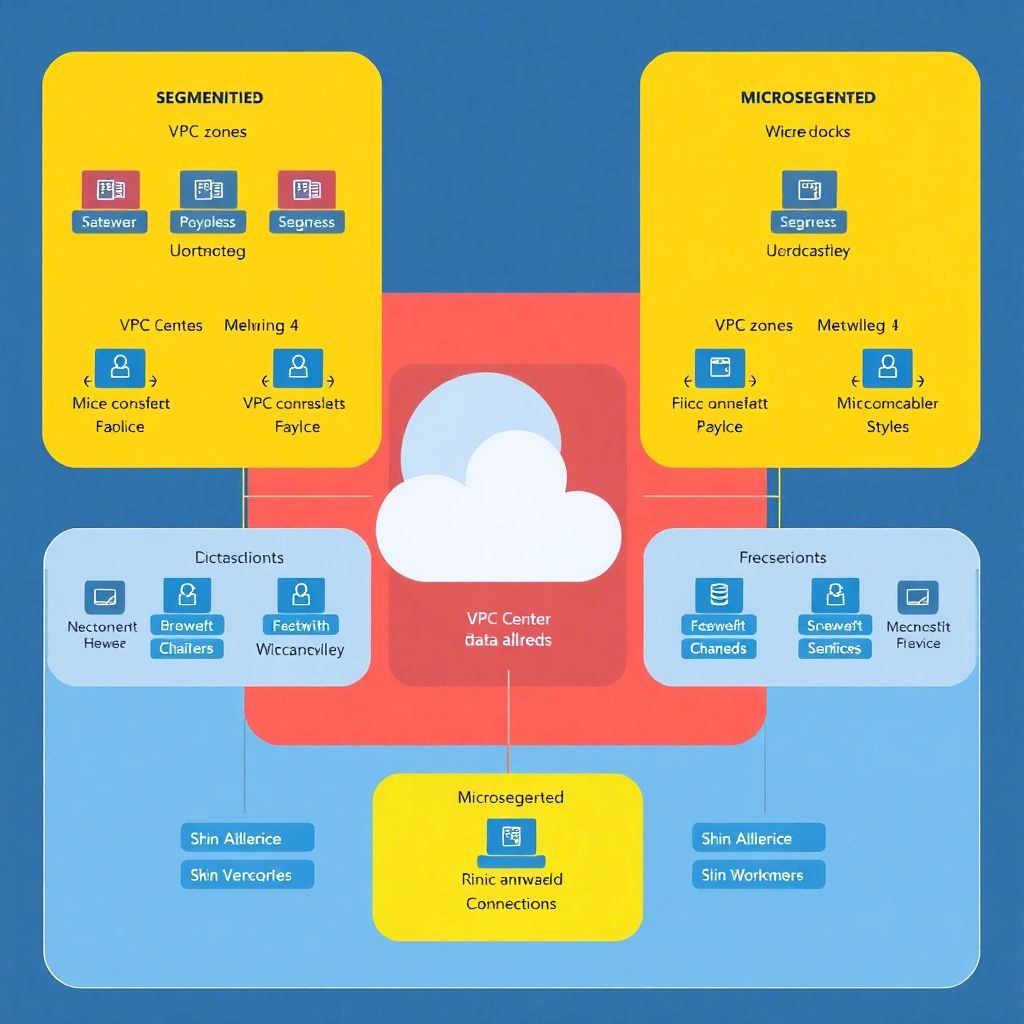
Network segmentation and microsegmentation in cloud: secure design and examples
Secure network segmentation and microsegmentation in cloud means grouping workloads by risk, identity and function, then enforcing least-privilege traffic rules at VPC/VNet and workload level. You define environment and application zones, label assets consistently, apply deny-by-default policies, and continuously validate flows with logging, tests and simple rollback options. Essential design checkpoints for network and microsegmentation…
-

Zero trust in cloud environments: principles, architecture and real use cases
Zero Trust em cloud means every access to your cloud resources is verified continuously, regardless of network location, device or user role. To apply it safely, map your identities, segment networks, encrypt sensitive data and enforce least privilege using cloud‑native controls plus focused third‑party tools where your provider is weaker. Core Principles Snapshot for Cloud…
-

Backup, disaster recovery and cyber resilience in modern cloud environments
Cloud backup, disaster recovery (DR) and cyber resilience in cloud environments mean combining automated backups, documented recovery objectives (RTO/RPO), tested runbooks and strong security controls. For empresas no Brasil, focus on multi-region backups, immutable storage, clear DR responsibilities, and regular restore drills aligned with your plano de continuidade de negócios em ambiente cloud. Operational priorities…
-

Multicloud security: challenges, common pitfalls and key architecture patterns
If you operate workloads across multiple clouds, multicloud security means building consistent controls for identity, network, data and operations across providers. If you do not define shared guardrails, then each cloud drifts, attack surface grows, and incident response becomes chaotic, especially for Brazilian organizations mixing global hyperscalers and local serviços. Executive summary: core multicloud security…
-

How to detect and respond quickly to security incidents in cloud infrastructures
To quickly detect and respond to cloud security incidents, you need three things: prepared environments (inventory, IAM, baselines), automated monitoring with tuned alerts, and a clear triage and containment playbook. This guide focuses on practical, low‑risk steps that intermediate teams in Brazil can apply across major cloud providers. Immediate action checklist for cloud-security incidents Confirm…
-

Cloud security regulations news and impact in brazil and worldwide
Cloud security regulation in Brazil and worldwide is tightening around privacy, resilience and accountability. For Brazilian companies, this means aligning conformidade LGPD segurança em cloud para empresas with sector rules, contract updates, stricter vendor due diligence and auditable controls, while monitoring global trends that affect cross-border data, incident notification and requirements for provedores de cloud…
-

Cloud cybersecurity trends: Ai, Sase, Cnapp and what’s next
Cloud security over the next years will be dominated by five practical trends: AI-assisted attacks and defenses, SASE consolidation for remote access, CNAPP to secure cloud-native workloads, stronger multi‑cloud data protection, and deep automation for detection/response. For Brazilian companies, these trends reshape budgets, architectures and how teams operate day to day. Executive summary: trend highlights…
-

Secure Iam configuration guide for identities and access in hybrid environments
To configure secure identities and access (IAM) in a hybrid environment, centralize identity, enforce strong MFA and conditional access, standardize least privilege across cloud and on‑prem, automate lifecycle, and deploy unified monitoring. This guide focuses on segurança IAM em ambiente híbrido with practical, low‑risk steps suitable for Brazilian enterprise contexts. Security Objectives and Risk Boundaries…