Categoria: Notícias
-

Cloud key and secret management with Kms, Hsm and vaults: best practices
Cloud key and secret management in Brazil usually means combining a managed KMS for most keys, HSM only for the highest‑risk material, and a secrets vault for application credentials. Start with cloud‑native services, enforce least privilege, automate rotation, and standardize patterns across AWS, Azure and GCP to keep operations simple and auditable. Essentials: KMS, HSM…
-
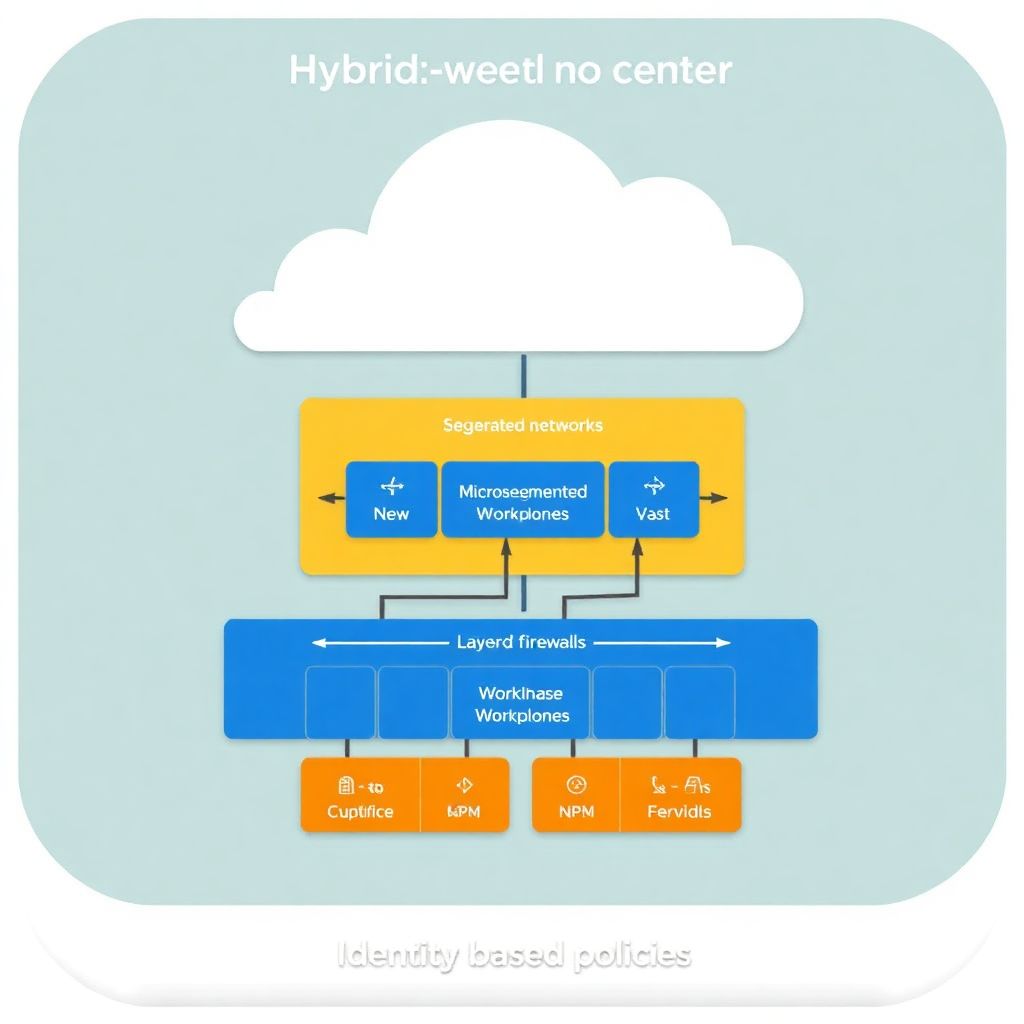
Segmentation and microsegmentation strategies for hybrid cloud networks
Hybrid cloud network segmentation and microsegmentation start with mapping workloads and trust boundaries, then designing layered controls across on‑prem and cloud. Use security groups, firewalls, and identity‑aware policies to isolate tiers, apply least privilege, and enforce Zero Trust consistently. Validate with logging, testing, and a safe, phased rollout to reduce disruption. Critical Implementation Milestones Document…
-

Practical hardening guide for accounts and identities in Aws, azure and Gcp
Hardening accounts and identities in AWS, Azure and GCP means eliminating standing admin access, enforcing strong authentication, segmenting tenants and projects, and continuously monitoring identity activity. Use organization-level guardrails, least privilege roles, secure MFA, managed secrets and well-tested incident playbooks tuned to the Brazilian context of segurança em nuvem aws azure gcp. Executive checklist: high-impact…
-

Siem and Soar cloud integration for faster incident response
To integrate SIEM and SOAR with AWS, Azure and GCP safely, start with a clear scope, use native cloud logging services, standardize data formats, and deploy a small pilot before scaling. Prioritize identity events, internet‑facing workloads and high‑value data. Use least‑privilege access, regional data controls and regular playbook testing. Core integration objectives and outcomes Achieve…
-

Sensitive data protection in cloud using encryption, tokenization and masking
For proteção de dados sensíveis na nuvem in Brazilian cloud environments, combine three layers: native at-rest and in‑transit encryption from your provider, application-level encryption or tokenization for the most critical identifiers, and data masking for non‑production and analytics. Choose per dataset: risk level, performance needs, integration effort and budget. Core safeguards for sensitive cloud data…
-

Cloud compliance and auditing: mapping controls to Lgpd, Iso 27001 and standards
To map cloud controls for LGPD, ISO 27001 and other standards safely, start by listing legal and contractual duties, then align them with concrete cloud configurations, logs and processes. Use a single control matrix, assign owners, define evidence per control, and automate monitoring with your cloud and GRC tools. Control mapping at a glance Use…
-

Security-driven cloud monitoring and observability with logs, metrics and traces
Security-oriented monitoring and observability in cloud means collecting and correlating logs, metrics, and traces to detect attacks, contain incidents, and prove compliance. In pt_BR environments this usually combines cloud-native logging, SIEM, and APM tools, with strict identity, encryption, and retention controls, plus runbooks for triage, investigation, and safe remediation. Security-focused executive summary: measurable observability goals…
-

Open source tools for cloud security in 2026: comprehensive review
For an intermediate team in Brazil seeking low-cost cloud protection in 2026, the most balanced stack is: Trivy for CSPM and SCA, Falco for runtime/CWPP, Cloud Custodian for cloud governance, Open Policy Agent for policy-as-code, and Wazuh or OpenSearch for centralised alerting. Start small, automate, then expand coverage gradually. Budget-focused snapshot of leading open-source cloud…
-
Cloud incident detection and response runbook: practical guide for Soc teams
A practical cloud incident detection and response runbook for a SOC defines who does what, in which system, within which time, and how to prove the incident is contained. It links cloud-native logs, SIEM alerts, and safe response actions, so analysts in Brazil can execute repeatable, auditable steps under pressure. Critical Runbook Objectives for Cloud…
-

Ci/cd security automation for cloud-native applications in modern pipelines
To automate security in cloud-native CI/CD pipelines, start by modeling risks, then embed SAST, DAST and dependency checks into every merge, protect secrets with a managed store and ephemeral credentials, enforce policy-as-code on IaC, automate container and cluster hardening, and close the loop with observability and incident playbooks. Security priorities for automating CI/CD in cloud-native…