Categoria: Notícias
-

Advanced Iam implementation guide: roles, policies, least privilege and temp roles
Implement advanced IAM by first mapping identities and trust boundaries, then designing a clear role taxonomy and naming. Author granular, version-controlled policies, enforce least privilege with approvals, and use temporary roles for risky operations. Continuously monitor, audit, and automatically remediate drift across AWS, Azure, and GCP using safe, reversible changes. Practical implementation checklist Define business-critical…
-

News & trends: recent cloud attacks and key lessons for stronger security
Recent cloud attacks show repeating patterns: abused identities, misconfigurations, and supply‑chain gaps. If you run workloads in public cloud, then you must treat identity, configuration baselines, and third‑party access as primary attack surfaces. If you improve monitoring, response, and architecture together, then you drastically reduce impact even when incidents happen. Executive summary: recent cloud incidents…
-

Docker image security in containers: comparing open source analysis tools
For most pt_BR teams, start with Trivy as the primary scanner de facto for Docker images, then complement it with Grype for cross-checking and TruffleHog for secret hunting. Clair, Anchore Engine and Dagda fit more specialized, heavier setups. Prioritize fast, automated CI scans over rare, manual deep-dives. Security highlights at a glance Trivy is the…
-

Recent cloud provider attacks: key lessons and how to prepare your business
Recent attacks on cloud providers show that tenant security depends on both provider controls and your own configuration. Focus on reducing blast radius, hardening identities and control planes, validating vendor promises, and rehearsing incident response for provider‑side failures. This guide gives concrete, safe steps for Brazilian companies using public cloud. Immediate lessons from recent supply‑chain…
-

Cloud compliance: how to meet Lgpd, Gdpr and Iso 27001 in full cloud
To meet LGPD, GDPR and ISO 27001 requirements in a cloud-only infrastructure, start by mapping personal data, defining controller/processor roles, and restricting providers to compliant regions. Then implement strong IAM, encryption, monitoring, and incident response. Document everything as evidence and regularly reassess risks, contracts, and cloud services as your environment evolves. Essential compliance priorities for…
-
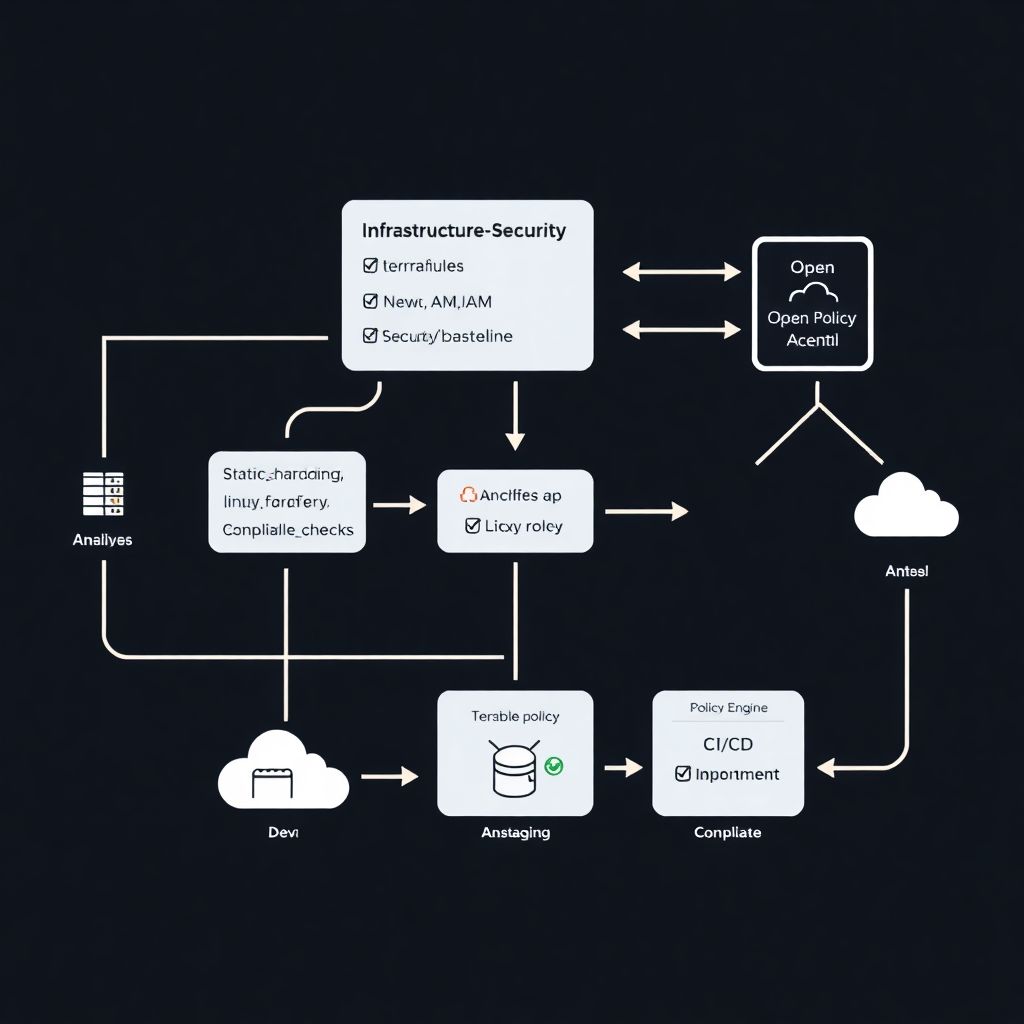
Security automation with infrastructure as code policies using terraform and ansible
Por que falar de segurança com Infrastructure as Code agora? Security automation with Infrastructure as Code (IaC) stopped being a “nice-to-have” the moment attackers começaram a versionar os próprios ataques. If your cloud, network and Kubernetes clusters are still configured “by hand” while the rest of the pipeline is automated, you’re basically leaving the front…
-

Cnapp tools review: unifying Cspm, Cwpp and Ciem in one security platform
Por que vale a pena revisar ferramentas de CNAPP hoje Cloud Native Application Protection Platform (CNAPP) deixou de быть buzzword e virou requisito básico para qualquer equipe que leva segurança em nuvem a sério. Em vez de manter CSPM, CWPP e CIEM separados, a ideia é consolidar visibilidade, detecção e correção em uma única camada…
-
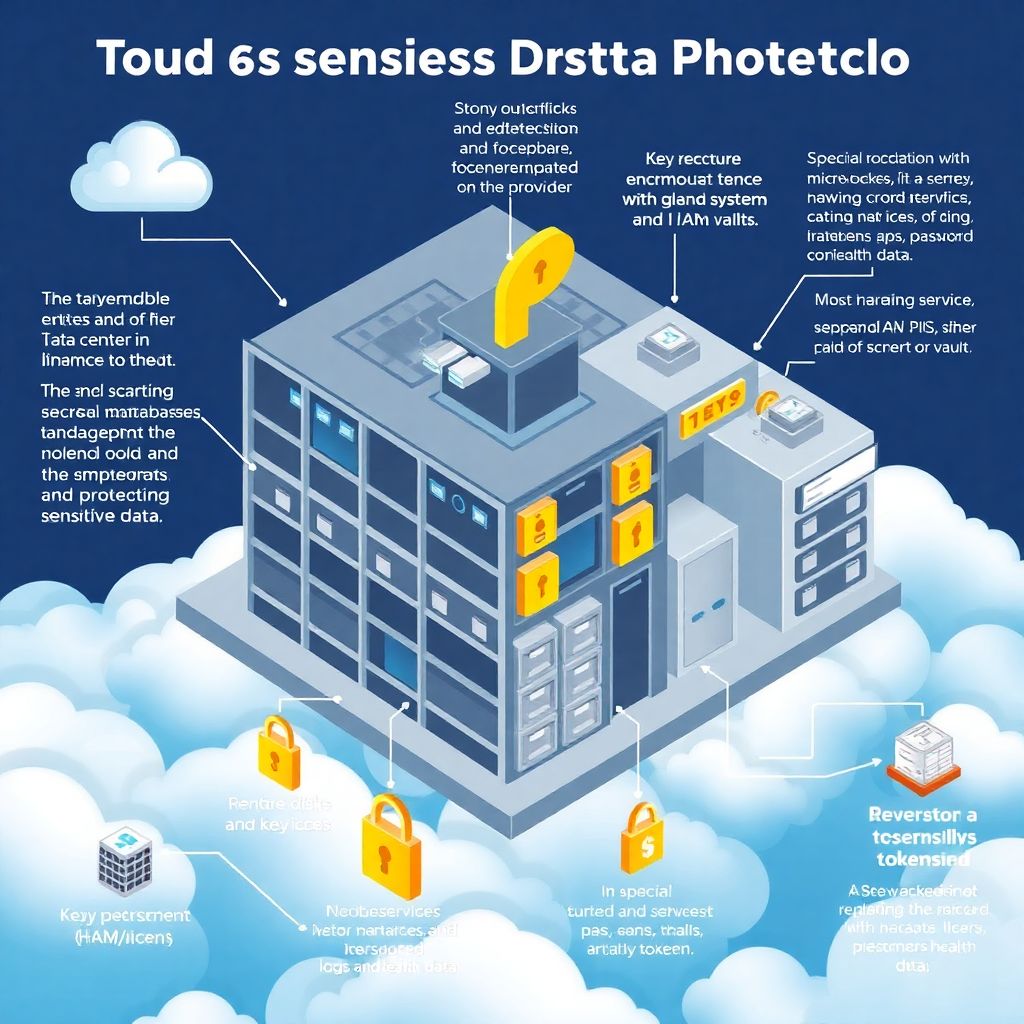
Sensitive data protection in the cloud with encryption, tokenization and classification
Why cloud data protection is trickier than it looks When you move critical workloads to the cloud, you don’t just change where your data lives — you fundamentally change how it’s accessed, shared and attacked. Proteção de dados sensíveis na nuvem is less about one magic product and more about putting several well‑designed layers in…
-

How to structure a cloud Iam program for effective identity and access management
Entendendo de onde veio o IAM em nuvem A gestão de identidades nasceu bem antes da nuvem ganhar força. Nos anos 90 и начале dos 2000 компании se viravam com diretórios locais, como o clássico Active Directory, e controles de acesso baseados em rede interna e VPN. A lógica era simples: se você está “dentro”…
-
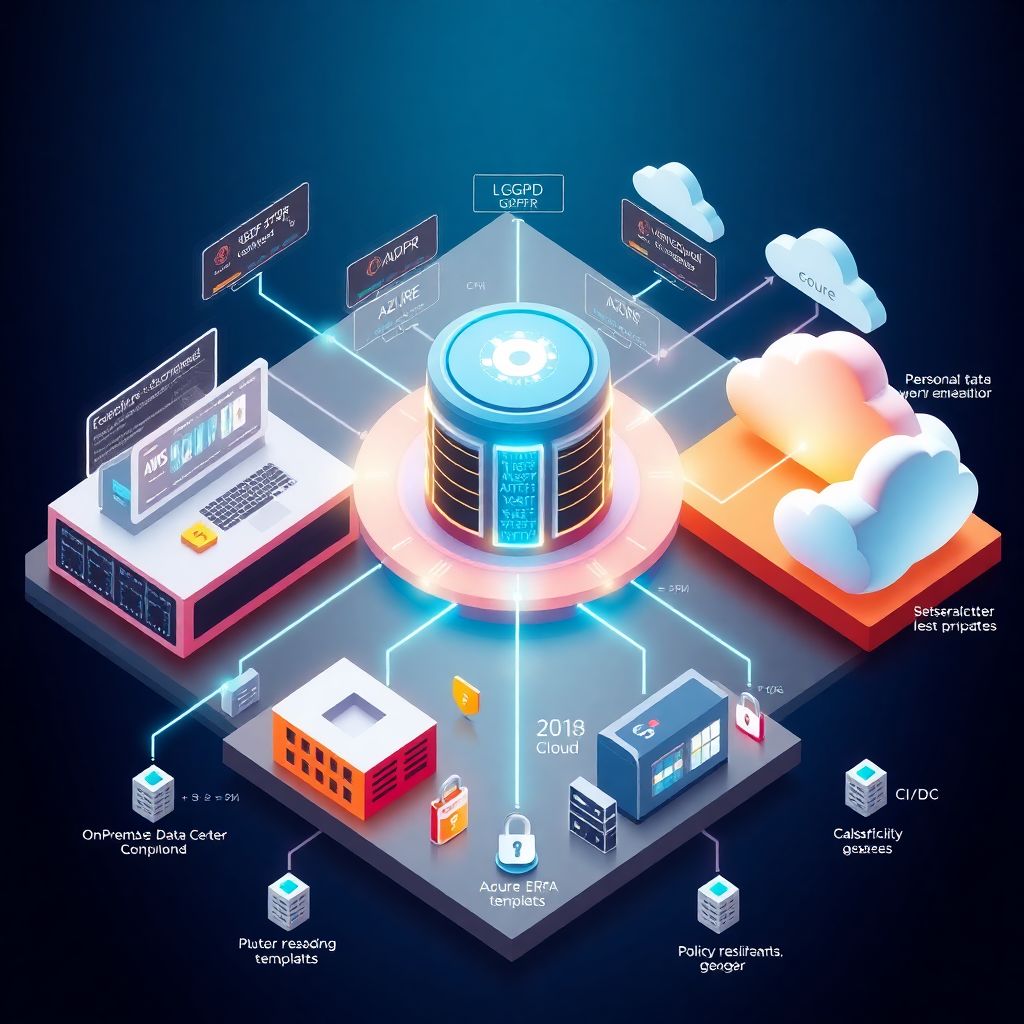
Compliance in hybrid cloud: meeting Lgpd, Gdpr and Iso 27001 requirements
Por que compliance em cloud híbrida ficou tão complicado de repente? Nos últimos três anos, o jogo mudou forte. Cloud híbrida e multicloud viraram padrão, LGPD e GDPR começaram a “doer no bolso” com multas reais, e a ISO 27001 deixou de ser só um selo bonito para virar critério de contrato. Ao mesmo tempo,…