Categoria: Notícias
-
Api security in serverless architectures: risks, patterns and recommended controls
Por que falar de segurança de APIs em serverless agora Quando empresas migram para funções serverless, muita gente pensa que a segurança “vem no pacote” junto com o provedor de nuvem. Só que segurança de api em serverless é uma área onde erros pequenos se transformam em incidentes grandes, justamente porque tudo escala muito rápido….
-
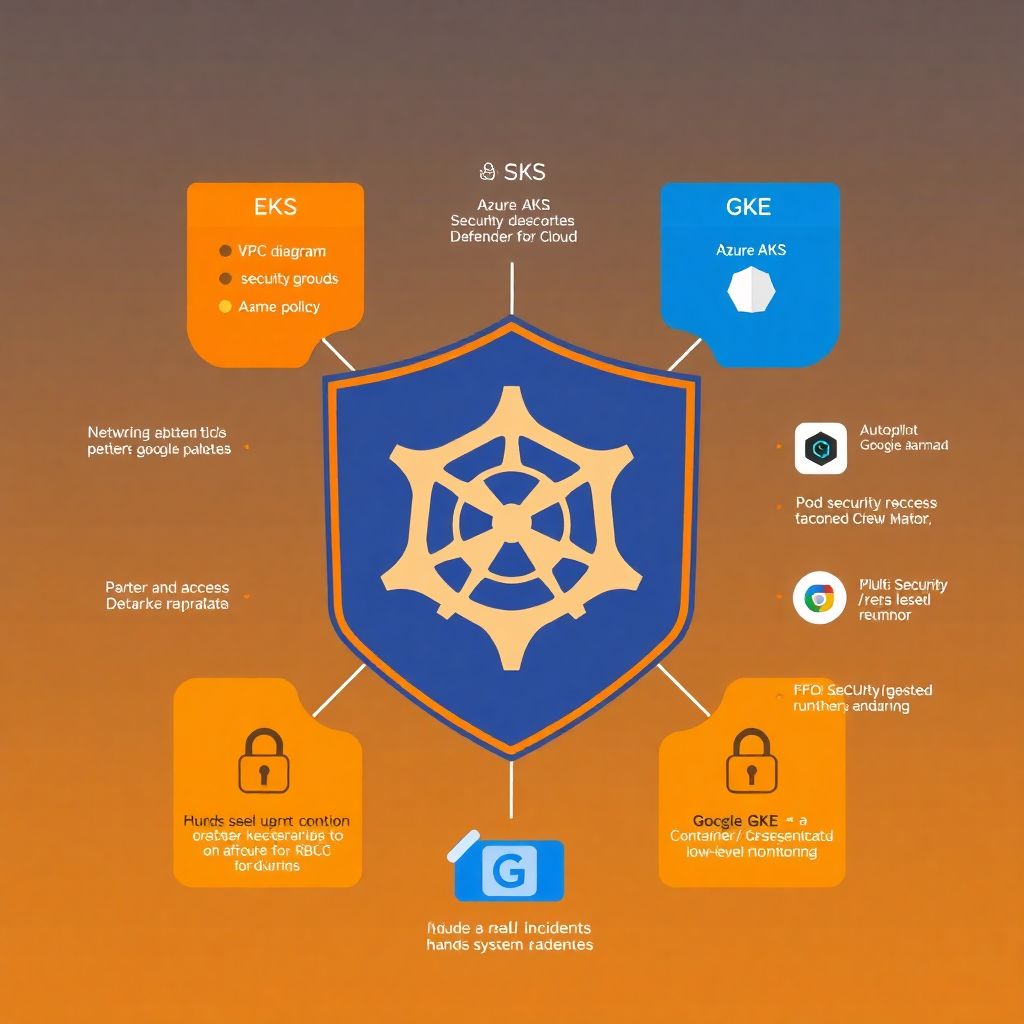
Kubernetes hardening best practices for managed clusters on Eks, Aks and Gke
Por que hardening em Kubernetes gerenciado ainda é um assunto espinhoso Hardening de clusters Kubernetes gerenciados (EKS, AKS, GKE) parece simples na teoria: o provedor cuida do plano de controle, você cuida do resto. Na prática, 2024–2026 mostraram que a maioria dos incidentes em cloud não vem de zero-days, mas de configurações frouxas, permissões demais…
-
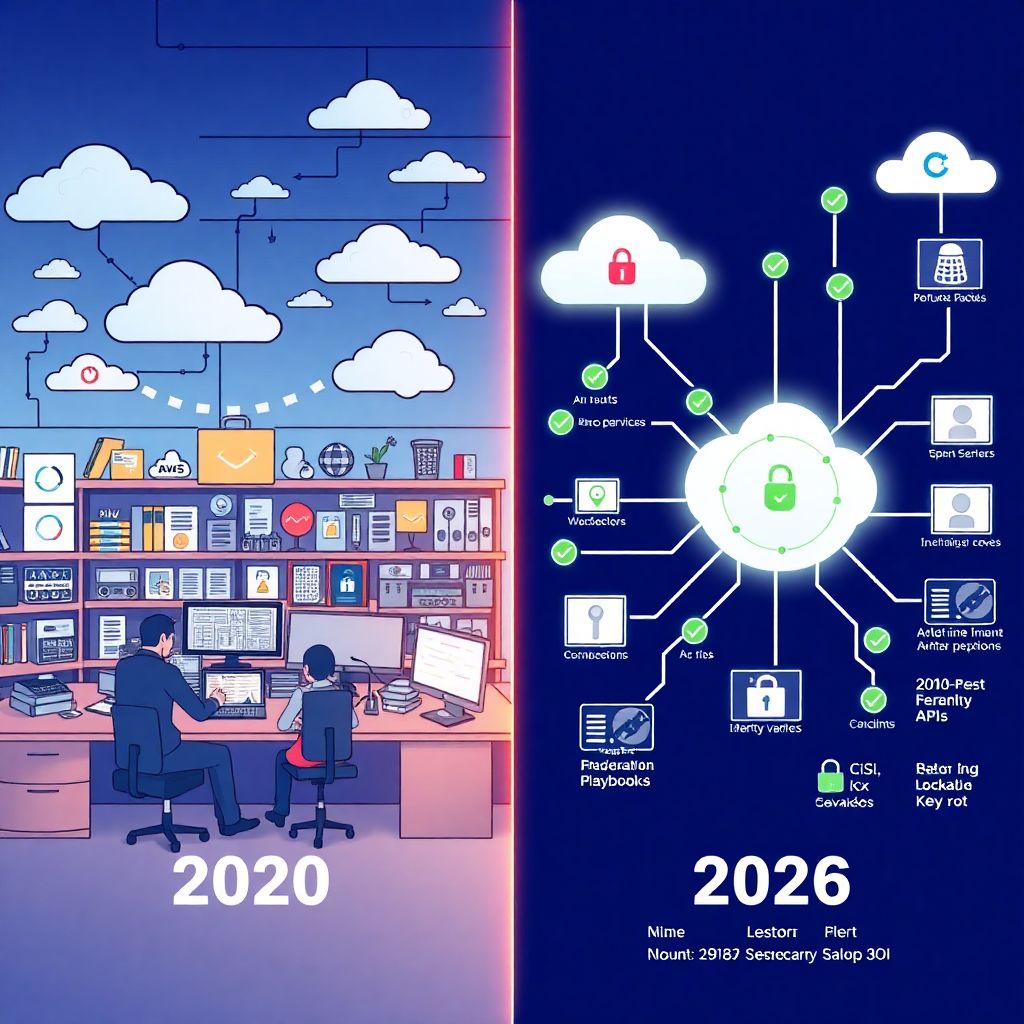
Cloud cybersecurity trends: Ai, security by design and new regulations
Por que falar de cibersegurança em cloud em 2026 é diferente de falar em 2020 Se em 2020 muita empresa ainda discutia se “valia a pena ir para a nuvem”, em 2026 o debate mudou completamente: agora a pergunta é como manter a segurança em nuvem para empresas num cenário em que tudo é distribuído,…
-
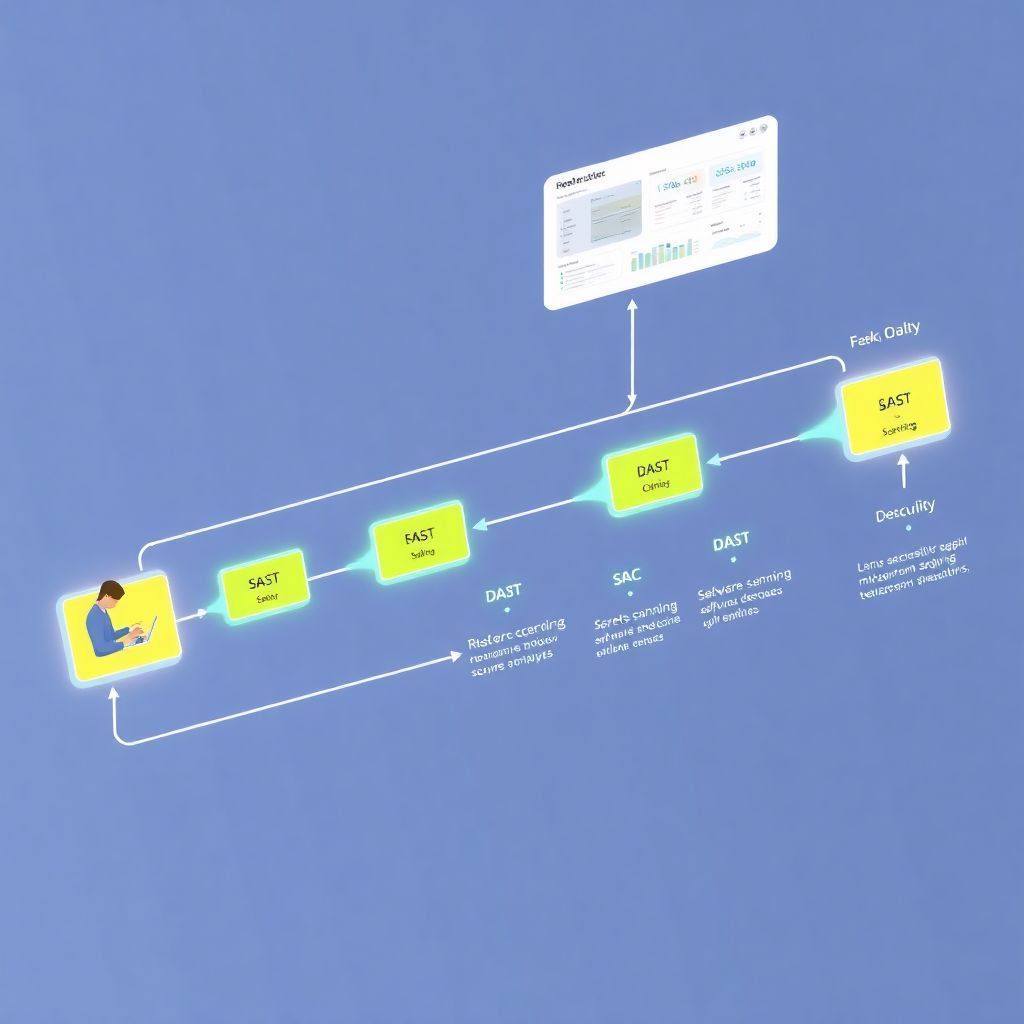
Devops pipeline security with Sast, Dast and iac scanning without slowing developers
Por que segurança em pipelines DevOps mudou muito até 2026 Se você ainda olha para segurança em pipelines DevOps como um “check” no fim da esteira, está perdendo o bonde de 2026. Hoje, SAST, DAST e scanner IaC já não são mais só “extras”, e sim peças centrais de plataformas devsecops completas, integradas desde o…
-

Cspm tools comparative review: key cloud security metrics that really matter
If you’ve ever tried to compare CSPM tools side by side, you know the feeling: every vendor says they’re “AI‑driven”, “cloud‑native” and “context‑aware”. After the third demo, everything sounds the same. So let’s strip away the marketing and look at what *really* matters when doing uma revisão comparativa de ferramentas CSPM — focusing on metrics,…
-

Cloud data encryption at rest and in transit without hurting performance
Por que criptografia na nuvem parece lenta (e por que não precisa ser) A percepção comum é simples: “se eu criptografar tudo, meu app vai ficar mais lento”. Na prática, o problema quase nunca é a criptografia em si, e sim: – Escolha errada de algoritmos ou modos de operação – Má arquitetura de chaves…
-

Cloud data protection at rest and in transit with end‑to‑end encryption
Why data protection in the cloud is no longer optional When companies move everything to the cloud, they don’t just move servers; they move their risks. Files, logs, backups, analytics data – all of this lives either “at rest” in storage or “in transit” moving between services. Both states are attack surfaces. Over the last…
-

How to assess cloud security maturity using recognized frameworks
Entendendo maturidade de segurança em cloud Quando a gente fala em maturidade de segurança em cloud, está falando de quão repetível, mensurável e bem integrado é tudo que você faz para proteger workloads, dados e identidades. Não é só “ter firewall e MFA”; é ter processo, automação e métricas claras. Uma boa avaliação de segurança…
-
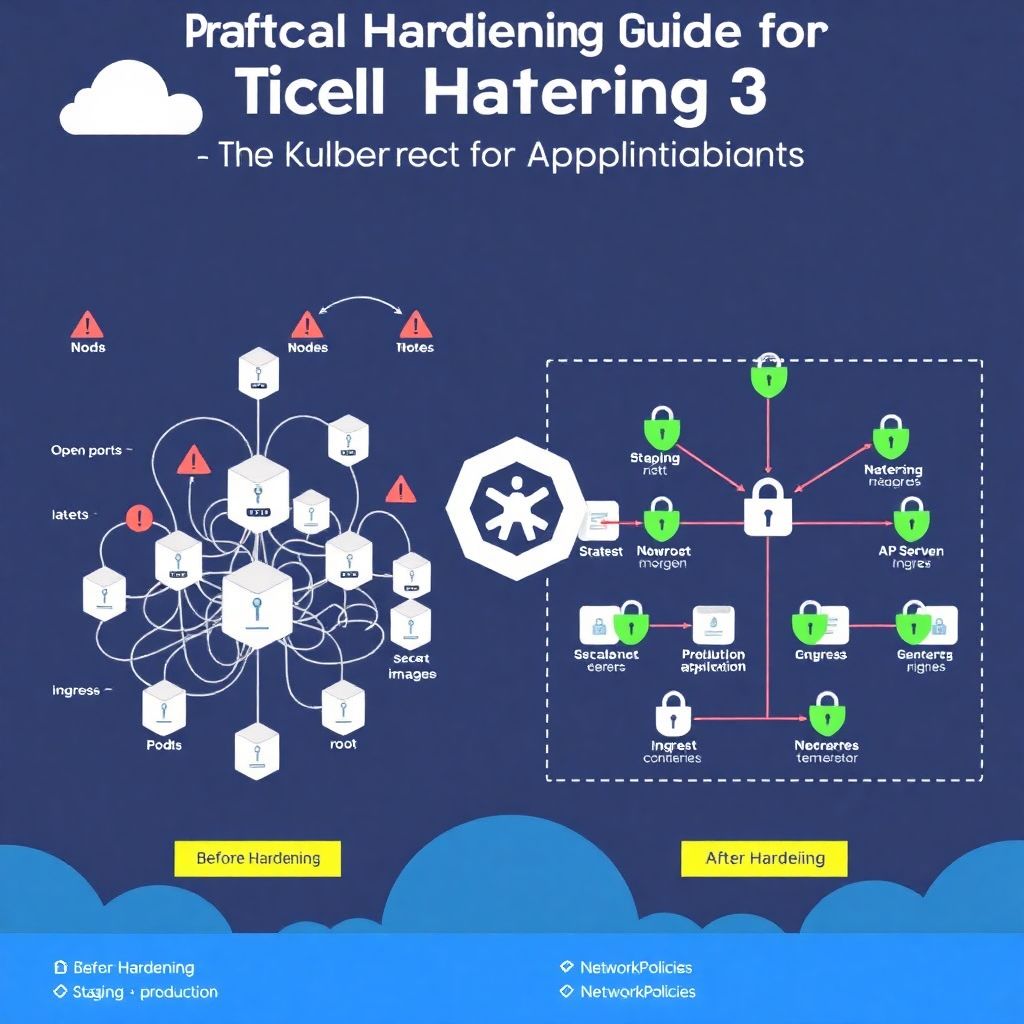
Practical kubernetes hardening guide from cluster to secure production applications
Por que falar de hardening em Kubernetes agora, e não “когда‑нибудь потом” Kubernetes давно перестал быть игрушкой для энтузиастов: сегодня это стандарт для продакшн‑инфраструктуры в банках, финтехе, медицине, e‑commerce и геймдеве. И чем популярнее платформа, тем активнее её изучают атакующие. Hardening Kubernetes em produção уже не про «дополнительный плюс к резюме», а про базовую гигиену…
-
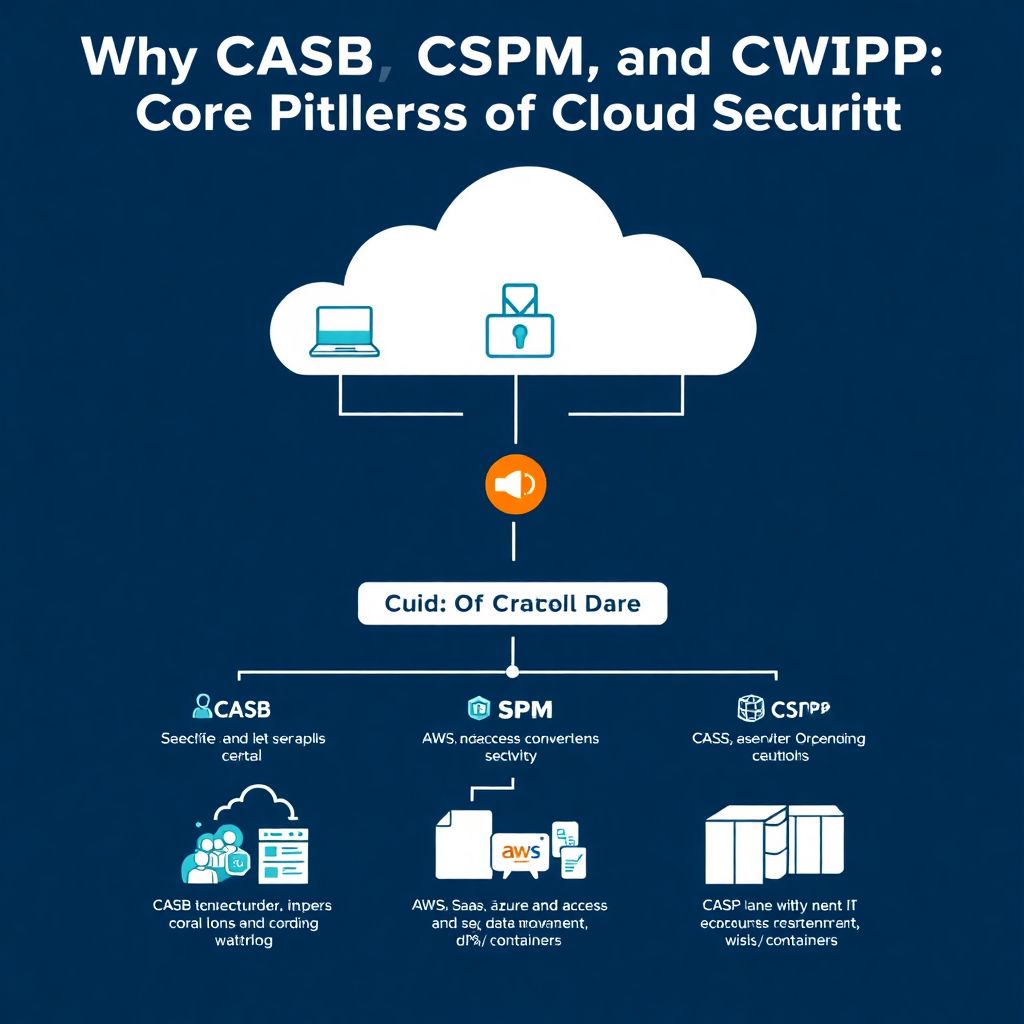
Casb, Cspm and Cwpp comparison: when to use each and integrate in your security stack
Why CASB, CSPM and CWPP became core to cloud security The shared‑responsibility gap in the real world Most teams discover CASB, CSPM and CWPP the hard way: after a nasty incident or an expensive audit. Cloud providers protect their infrastructure, but you’re on the hook for configs, identities, data and workloads. That creates a wide…