Zero Trust Network Access (ZTNA) and Security Service Edge (SSE) protect remote access to cloud resources by replacing flat VPN connectivity with identity‑centric, application‑level access. You authenticate users and devices, evaluate context (location, posture, risk), then grant least‑privilege access only to specific apps, continuously monitoring sessions and blocking or isolating risky behavior.
Essential Controls for ZTNA and SSE Implementations
- Enforce strong identity verification with MFA and device posture checks before granting any access.
- Publish only specific applications through ZTNA instead of exposing networks via broad VPN access.
- Apply least‑privilege policies with contextual conditions (user role, location, device, risk score).
- Inspect and control traffic with SSE controls such as SWG, CASB and DLP for cloud applications.
- Continuously monitor sessions and terminate or re‑authenticate on risk changes or suspicious behavior.
- Integrate ZTNA and SSE tightly with your IdP and logging/monitoring stack for traceability.
- Roll out incrementally, starting with a pilot and high‑value applications, validating user experience and security.
Understanding ZTNA and SSE: Principles and Threat Model
For teams in Brazil asking zero trust network access ztna o que é, ZTNA is a model where no user, device or network is trusted by default. Every request to an application is authenticated, authorized and inspected, regardless of location (on‑premises, home office or public Wi‑Fi).
SSE (Security Service Edge) groups network security capabilities such as secure web gateway (SWG), cloud access security broker (CASB), ZTNA and often DLP and firewall‑as‑a‑service into a cloud‑delivered platform. Instead of backhauling traffic to a data center, security is enforced close to the user and the application.
These approaches are ideal when you need soluções ztna para acesso remoto seguro to SaaS and IaaS, have many remote workers, and want consistent policies for on‑prem and cloud. They are less suitable if:
- Your environment has almost no remote access, and all systems are strictly isolated on‑premises.
- You rely heavily on legacy protocols or thick clients that ZTNA/SSE cannot proxy effectively.
- You lack basic identity hygiene (no central IdP, poor MFA coverage), making zero trust implementation fragile.
Before selecting plataformas zero trust e sse para empresas, be clear on your main risks: compromised credentials, unmanaged devices, lateral movement inside VPNs, and data exfiltration from SaaS. ZTNA and SSE directly address these by shrinking implicit trust and increasing visibility.
Architectural Patterns for Secure Remote Access to Cloud Resources
To design how to use ZTNA and SSE to como proteger acesso remoto a aplicações em nuvem, start by mapping where your applications live and how users connect today.
Core building blocks
- Identity Provider (IdP): Central SSO with MFA (e.g., SAML/OIDC) is mandatory. All access decisions should rely on IdP attributes and groups.
- ZTNA gateway or connector: A component deployed near your private apps (data center, branch, VPC/VNet) that establishes outbound connections to the ZTNA cloud and publishes specific applications.
- SSE platform: Cloud‑delivered security service that combines SWG, CASB and ZTNA, often integrated with endpoint agents or clientless proxies.
- Endpoint security: EDR/antivirus and posture assessment (OS version, disk encryption, jailbreak/root checks) used as conditions in access policies.
- DNS and network controls: For steering user traffic to the SSE service and blocking direct access to sensitive apps and cloud resources.
- Logging and SIEM: Central storage of ZTNA/SSE logs (authentication, authorization, policy decisions, data actions) for detection and forensics.
Reference access patterns
- Private web apps via ZTNA: Users access an external portal; the ZTNA gateway authenticates via IdP, evaluates device posture, then reverse‑proxies only allowed internal HTTP(S) apps.
- SaaS apps via SSE: All web traffic and cloud app access flows through an SSE point of presence, where SWG/CASB controls enforce acceptable use and DLP.
- Cloud workloads (IaaS/PaaS): Admin access is restricted via ZTNA, while service‑to‑service traffic uses cloud‑native controls (security groups, private endpoints) plus SSE inspection where feasible.
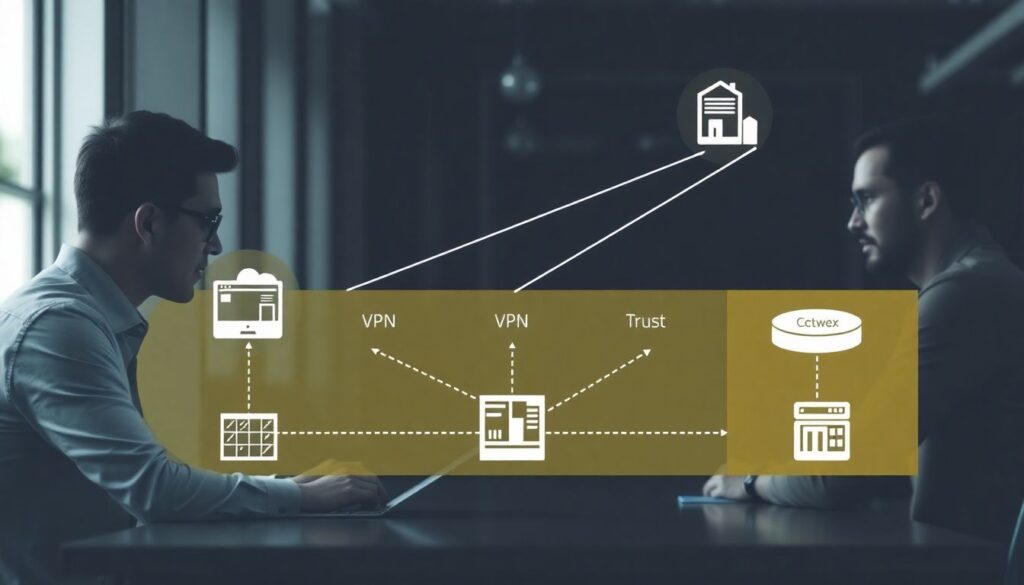
Comparative view: legacy VPN vs ZTNA+SSE
| Approach | Main Pros | Main Cons/Risks | Mitigation Tips |
|---|---|---|---|
| Traditional full‑tunnel VPN | Simple concept, supports many protocols, widely available on devices. | Broad network access, hard to enforce least privilege, lateral movement, limited app‑level visibility. | Restrict VPN subnets, segment networks, add strong MFA and monitoring of privileged users. |
| ZTNA only | Application‑level access, reduced attack surface, no inbound firewall openings to apps. | May not cover all traffic types, limited data protection without SSE, risk of mis‑scoped policies. | Start with high‑value web apps, validate policies with read‑only access, combine with DLP where possible. |
| ZTNA + SSE platform | Unified access and traffic inspection, consistent policies for SaaS and private apps, better user experience. | Higher complexity, vendor lock‑in risk, misconfiguration can break connectivity or create blind spots. | Implement gradually, maintain fallback paths, document policies clearly, test with varied user profiles. |
Policy Design: Least Privilege, Contextual Access and Session Controls
Before the detailed steps, be aware of key risks and limitations when implementing ZTNA/SSE policies:
- Overly permissive policies recreate VPN‑like flat access, undermining zero trust benefits.
- Overly strict or unstable conditions (e.g., aggressive geoblocking) may lock out legitimate users.
- Missing break‑glass access can block incident response during platform or IdP outages.
- Inconsistent group mappings between IdP and ZTNA/SSE break policy logic and create shadow access paths.
- Insufficient logging retention makes later investigations and compliance audits difficult.
-
Inventory and classify applications
List all applications that will move from VPN to ZTNA/SSE, including URL, protocol, environment and data sensitivity.- Group apps into tiers (e.g., public‑like, internal, confidential, highly regulated).
- Identify which apps are web‑based and easier to onboard first.
-
Map identities, roles and ownership
Align each application with its business owner, user groups and admins in your IdP.- Ensure every application has clear security and operational owners.
- Normalize IdP groups (naming, membership) to avoid ad‑hoc exceptions.
-
Define baseline access conditions
Decide which conditions must always be present before access is even considered.- MFA for all remote access, especially for admins and sensitive apps.
- Minimum device posture (managed device, updated OS, no known compromise).
- Block high‑risk geographies or TOR exit nodes where applicable.
-
Create least‑privilege policies per application
For each app, define which user groups can access which environment (dev, test, prod) and with what rights.- Prefer role‑based access mapped from IdP claims rather than individual user rules.
- Separate admin interfaces or paths and require stronger conditions (e.g., corporate device only).
-
Incorporate contextual and risk‑based controls
Extend policies to consider context signals, such as IP reputation, device health, and user risk scores.- Require step‑up MFA when risk increases, rather than silently blocking at first.
- Restrict sensitive apps from unmanaged or mobile devices if business allows.
-
Define session controls and data protections
Use SSE capabilities to govern what users can do after access is granted.- Limit downloads or copy/paste from sensitive SaaS to unmanaged devices.
- Monitor for bulk downloads, mass sharing or anomalous API usage.
- Set session timeouts and re‑authentication intervals based on app sensitivity.
-
Design monitoring and alert thresholds
Decide which events should trigger alerts and automated responses.- Multiple denied access attempts, impossible travel or rapid IP changes.
- Policy bypass attempts, such as direct access to app IPs outside ZTNA/SSE.
-
Document exceptions and break‑glass paths
For rare cases where standard policies do not work, define tightly controlled exceptions.- Time‑bound access with explicit approvals and enhanced logging.
- Out‑of‑band access for incident responders during IdP or network outages.
Step-by-Step Deployment: From Pilot to Full-Scale Rollout

Use this checklist to validate that your ZTNA/SSE rollout is progressing safely and effectively:
- IdP is integrated with the ZTNA and SSE platforms, with test users and groups synced correctly.
- A small pilot group (IT and friendly business users) can access 1-3 low‑risk apps through ZTNA without VPN.
- Logs from ZTNA/SSE (auth, access, policy hits) flow reliably into your SIEM or log platform.
- Fallback access (e.g., legacy VPN) is documented and restricted, used only when ZTNA/SSE is unavailable.
- Initial policies are reviewed by security and application owners before applying to larger user populations.
- Performance and latency are measured from Brazil and other key regions to main cloud providers.
- Help desk runbooks exist for common user issues (MFA failure, device not compliant, blocked download).
- User communication explains why access paths change, how to use the new portal/agent, and how to report issues.
- High‑value and admin applications are migrated later, with specific test plans and rollback criteria.
- Legacy VPN dependencies are tracked and reduced over time, with clear end‑of‑life dates.
Integrations: Identity, CASB, SWG and Cloud Service Providers
Integrations are where many ZTNA and sse security service edge fornecedores projects stumble. Watch for these common mistakes:
- Relying on local ZTNA user stores instead of central IdP, creating inconsistent access and extra credential stores.
- Not standardizing SAML/OIDC attributes, leading to broken group‑based policies between IdP and SSE.
- Enabling CASB in “monitor only” mode indefinitely, so data protection policies never actually block risky actions.
- Failing to integrate SWG with endpoint agents, which allows users to bypass HTTP/HTTPS inspection.
- Misconfiguring cloud provider routes or private endpoints, leaving direct paths that bypass ZTNA and SSE.
- Overlapping URL categories and app definitions between SWG and CASB, causing unpredictable rule evaluation.
- Ignoring API‑based CASB integrations for major SaaS platforms, missing shadow IT and risky app usage.
- Not synchronizing security incident workflows between SSE alerts and your existing SOC tooling.
- Skipping joint testing with cloud teams before enforcing traffic redirection for production workloads.
Monitoring, Detection and Incident Playbooks for ZTNA/SSE Environments
When full ZTNA+SSE deployment is not immediately possible, or when requirements are very specific, consider these alternative or complementary approaches:
- Hardened VPN with micro‑segmentation: Keep VPN for some use cases, but enforce strict network segments, just‑in‑time access and strong MFA while you gradually introduce ZTNA.
- Cloud‑native access controls: For some IaaS/PaaS services, use provider features (private endpoints, identity‑aware proxies, just‑in‑time admin) combined with CASB/SWG, even before full ZTNA coverage.
- Reverse proxy and WAF for specific apps: For a small number of critical web apps, a hardened reverse proxy with WAF and SSO can provide some zero trust characteristics with less architectural change.
- Managed security services: If your team lacks expertise, partner with a provider experienced in ZTNA and SSE who can operate the platform while you retain policy ownership.
Regardless of the chosen mix, define incident playbooks that describe how to respond to signals such as anomalous sessions, mass downloads from SaaS, or repeated ZTNA denials for admin accounts.
Practical Clarifications on Common Deployment Obstacles
How is ZTNA different from a traditional VPN for remote access?
VPN provides network‑level access, placing the device inside your internal network. ZTNA grants access only to specific applications after identity and posture checks, keeping networks hidden. This reduces lateral movement risk and allows more granular, context‑aware policies.
Can I start with ZTNA without deploying the full SSE stack?
Yes. Many organizations begin by publishing a few private web apps through ZTNA while keeping existing SWG or VPN solutions. Over time, you can add CASB, SWG and DLP features to move towards a full SSE architecture.
What if some legacy applications cannot work behind ZTNA?

Keep a restricted VPN or jump host for those specific protocols while you modernize or replace them. Apply strong segmentation, monitoring and time‑bound access, and prioritize modernization of the highest‑risk legacy apps.
How do I minimize user disruption during migration from VPN to ZTNA?
Run VPN and ZTNA in parallel for a transition period, onboarding a small pilot group first. Provide clear instructions, update documentation, and ensure help desk staff are prepared to support the new access method.
Do I need agents installed on all endpoints to use ZTNA and SSE?
Agent‑based deployments provide stronger posture checks and coverage, but many ZTNA and SSE platforms also support agentless or browser‑based access. For unmanaged devices, browser‑based ZTNA plus CASB/SWG controls is often the most practical option.
How should I prioritize which applications move to ZTNA first?
Start with high‑impact, web‑based internal apps that are widely used and currently exposed via VPN. Then move to administrative portals and sensitive apps, using lessons from the first wave to fine‑tune policies and user communication.
What logging is essential for effective monitoring and incident response?
Collect authentication events, policy decisions, session start/stop, denied access attempts and key data actions (downloads, shares, uploads). Forward these logs to your SIEM, correlate with IdP and endpoint events, and define alerts for risky combinations.
