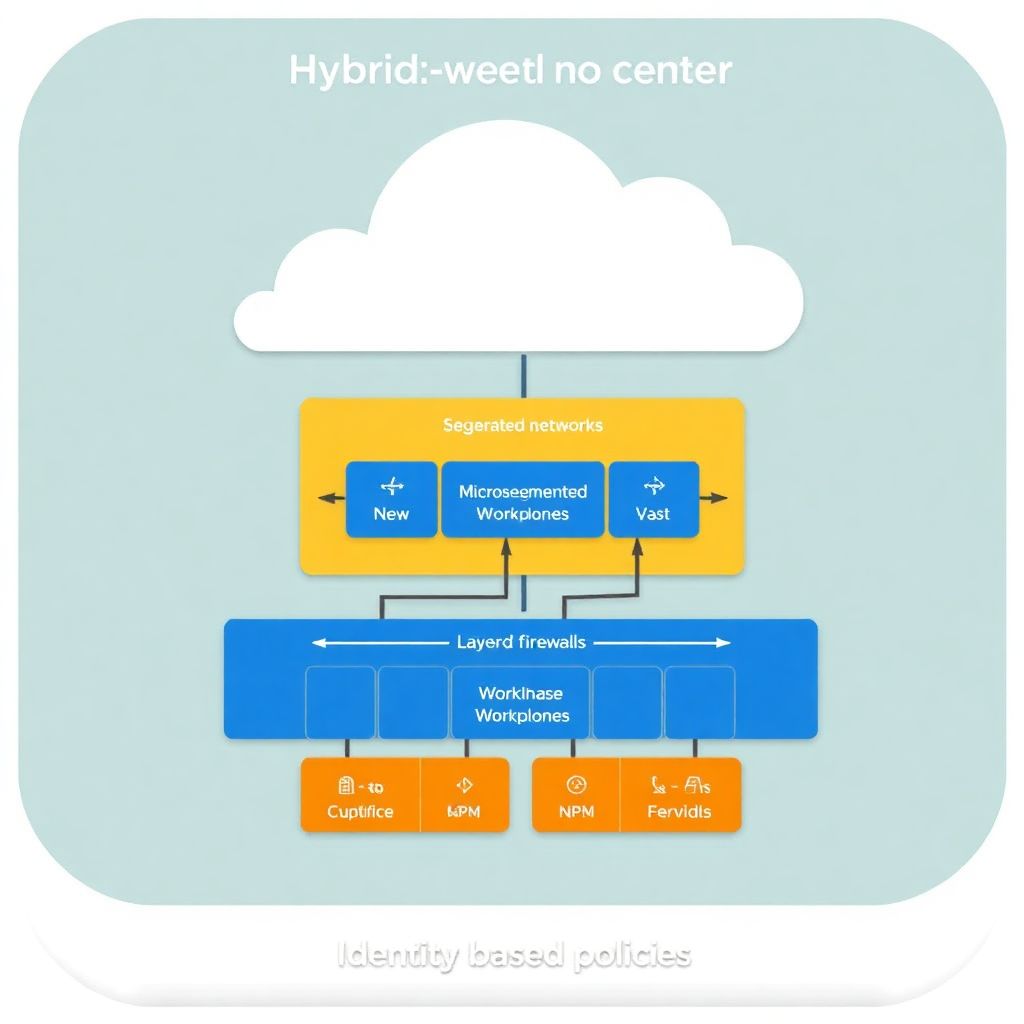
Hybrid cloud network segmentation and microsegmentation start with mapping workloads and trust boundaries, then designing layered controls across on‑prem and cloud. Use security groups, firewalls, and identity‑aware policies to isolate tiers, apply least privilege, and enforce Zero Trust consistently. Validate with logging, testing, and a safe, phased rollout to reduce disruption.
Critical Implementation Milestones
- Document business‑critical applications, data flows, and trust boundaries across on‑premises and cloud environments.
- Choose segmentation patterns for data center, cloud VPC/VNet, and branch edges that align with Zero Trust principles.
- Standardize tools and APIs: firewalls, cloud-native controls, and plataformas de zero trust e microsegmentação para cloud híbrida.
- Implement and test microsegmentation policies in monitor‑only mode before enforcing blocks.
- Automate policy deployment and validation with CI/CD pipelines and configuration management.
- Continuously monitor logs, adjust rules, and rehearse incident response playbooks.
Mapping Workloads and Trust Boundaries
This approach fits organizations running critical workloads both on‑prem and in public cloud, consuming segmentação de rede em cloud híbrida serviços from providers or building in‑house controls. It is less suitable where networks are tiny, flat, and manually managed, or where you lack basic inventory and logging.
Follow these practical steps to discover and map safely:
- Inventory workloads across all environments – Collect virtual machines, containers, serverless functions, and PaaS services in your data center and clouds (AWS, Azure, GCP). Use CMDBs, cloud tags, and orchestration tools rather than manual spreadsheets wherever possible.
- Classify applications and data sensitivity – Group workloads into business services (payments, HR, CRM) and mark data types (personal, financial, internal). Map which apps expose internet‑facing endpoints and which are internal only.
- Map communication paths – Capture real traffic flows with safe, read‑only methods: flow logs, packet mirrors, or agent‑based discovery in soluções de microsegmentação de redes em nuvem híbrida. Identify east‑west (app to app) and north‑south (client to app) flows.
- Define trust boundaries – Draw boundaries around user zones, DMZ, application tiers, and data tiers. Consider compliance zones (e.g., regulated data), admin networks, and third‑party connections as separate trust areas.
- Prioritize high‑value segments – Rank applications by business impact and exposure, then select a first wave for microsegmentation. Start with scoped segments (e.g., production web‑to‑app tier) to keep the rollout safe and controlled.
Designing Layered Network Segmentation
Before changing anything in production, confirm that you have the required tools, access, and guardrails. The focus is to combine coarse‑grained segmentation with fine‑grained microsegmentation in a hybrid topology.
Required tools and access
- Access to cloud consoles and APIs for VPC/VNet, security groups, and network ACLs (ferramentas de segurança para segmentação de rede em cloud híbrida).
- Administrative access to data center firewalls (physical or virtual) and any SD‑WAN or overlay network controllers.
- Microsegmentation platform or agents, or at least host‑based firewalls that can be centrally managed.
- Logging platforms: flow logs, firewall logs, endpoint logs, SIEM or log analytics workspace.
- Change management process to approve and schedule rule deployment with rollback options.
Layered segmentation model
Design layers with clear responsibilities:
- Perimeter segmentation: internet edge, partner connections, VPN termination.
- Environment segmentation: separate production, staging, and development networks.
- Application‑tier segmentation: web, application, and database tiers, with distinct network segments.
- Identity‑aware microsegmentation: per‑workload policies using identities, labels, or tags.
Segmentation approaches comparison
| Approach | Scope | Typical Tools | Strengths | Limitations |
|---|---|---|---|---|
| Traditional VLAN / Subnet Segmentation | On‑prem networks | Switch ACLs, routers, firewalls | Clear isolation, mature operations | Coarse‑grained, complex in large environments |
| Cloud Native Security Groups | Single cloud VPC/VNet | SGs, NSGs, NACLs | Tight integration, tag‑based controls | Harder to unify across clouds and on‑prem |
| Overlay / SD‑WAN Segmentation | Branches and data centers | SD‑WAN controllers, virtual networks | Central control, supports multiple sites | Requires compatible hardware/clients |
| Host‑Based Microsegmentation | Workload level (VMs, containers) | Agents, host firewalls, eBPF | Fine‑grained, identity‑aware policies | Requires agents, careful change management |
| Zero Trust Access Platforms | User to app and app to app | plataformas de zero trust e microsegmentação para cloud híbrida | Strong identity, encryption, posture checks | Typically gradual migration, integration effort |
Compact migration checklist
| Step | Action | Safe‑Rollout Note |
|---|---|---|
| 1 | Enable logging and traffic discovery | Read‑only only; no blocking rules yet. |
| 2 | Define segments and tagging standards | Apply tags/labels without changing policies. |
| 3 | Deploy microsegmentation agents | Start in monitor mode for selected apps. |
| 4 | Create allow‑lists based on observed flows | Simulate impact before enforcing. |
| 5 | Gradually enforce blocks with back‑out plan | Use change windows and automated rollback. |
Implementing Microsegmentation Policies
The following steps show a safe and practical way to implement microsegmentation across a hybrid environment using common tools. Adapt command syntax to your preferred stack and always test in a non‑production environment first.
-
Standardize labels and identity for workloads – Decide how you will identify workloads: tags (env, app, tier), service accounts, or AD groups. Apply labels consistently across on‑prem and cloud to support unified policies.
- Example (Linux, cloud init):
ENV=prod APP=payments TIER=web - Example (Kubernetes):
labels: app: payments, tier: web, env: prod
- Example (Linux, cloud init):
-
Deploy microsegmentation agents or enable host firewalls – Roll out agents first in monitor‑only mode on a limited set of servers. If using native controls, standardize iptables/firewalld, Windows Firewall, or cloud‑integrated host firewalls.
- Example (Linux, safe baseline):
iptables -P INPUT ACCEPT; iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT - Keep default policies permissive until you verify observed flows.
- Example (Linux, safe baseline):
-
Discover and validate application flows – Use your microsegmentation console or logging platform to view all flows between tagged workloads. Confirm with application owners that each flow is required and document any temporary or migration‑related traffic.
- Prefer allow‑list (default deny) designs, but start from observed allow flows.
-
Define policy groups and intents – Create logical policy groups (e.g.,
prod-web,prod-app,prod-db) and express rules as high‑level intents.- Example intent: “prod‑web can talk to prod‑app on 443 only”.
- Example intent: “only backup service can reach prod‑db on backup port”.
-
Write and test policies in simulation mode – Many soluções de microsegmentação de redes em nuvem híbrida support simulation or audit modes. Enable policies as “log‑only” to detect what would be blocked.
- Example pseudo‑policy:
ALLOW prod-web TO prod-app PORT 443; DENY prod-web TO prod-db ANY - Monitor for simulated violations and fix missing flows before enforcement.
- Example pseudo‑policy:
-
Gradually enforce blocking with guardrails – Move from simulation to enforcement on low‑risk segments first. Use maintenance windows and documented rollback commands.
- Keep an emergency rule or playbook ready: for example, a “temporary relax” policy that allows intra‑segment traffic if a critical incident occurs.
- Always validate application health (synthetic tests, probes) immediately after each enforcement step.
-
Integrate with hybrid cloud controls – Align host‑level microsegmentation with cloud security groups and on‑prem firewalls. Avoid conflicting rules by defining a clear responsibility model: perimeter vs. east‑west vs. workload.
- Use consultoria em segmentação e microsegmentação de redes corporativas if you lack internal expertise to design the responsibility matrix.
- Document which platform is the “source of truth” for each layer of policy.
Быстрый режим
For teams that already have basic inventory and logging, this fast‑track algorithm helps you reach safe enforcement faster:
- Pick one critical but well‑understood application and tag all its workloads consistently (env, app, tier).
- Enable agents or host firewalls in monitor mode and capture flows for a defined observation period.
- Convert observed flows into explicit allow‑list rules, test them in simulation, then enforce during a maintenance window.
- Automate rule deployment for this application via scripts or IaC, then replicate the pattern across other apps.
Hybrid Cloud Connectivity and Security Controls
Use this checklist to validate that connectivity and controls across your hybrid environment are correctly implemented and safe:
- All hybrid links (VPN, Direct Connect, ExpressRoute, SD‑WAN) are documented with clear ownership and configuration baselines.
- Encryption in transit is enforced for all site‑to‑site tunnels and user‑to‑app connections, including private links.
- Routing rules avoid unintended “backdoor” paths between environments, especially between dev/test and production.
- Cloud VPC/VNet peering and on‑prem routes are restricted to required subnets only, not broad “any‑to‑any” ranges.
- Perimeter and cloud firewalls implement explicit allow‑lists for hybrid traffic, aligned with your microsegmentation policies.
- Identity‑aware access is in place for administrative access, preferably via Zero Trust or bastion hosts instead of direct RDP/SSH.
- DNS resolution paths are clearly defined to avoid cross‑environment leakage or unintended name resolution.
- Logging is enabled on all gateways and firewalls; logs are centralized and retained for investigations.
- Regular connectivity tests and failover drills confirm that hybrid paths work as expected under normal and degraded conditions.
Automation and Orchestration for Policy Enforcement
When automating policies for segmentação de rede em cloud híbrida serviços, avoid these frequent mistakes that can lead to outages or blind spots:
- Automating before standardizing tags and naming – scripts become brittle when labels are inconsistent across environments.
- Committing policy changes directly to production without a staging environment and automated tests.
- Mixing manual and automated changes on the same objects (security groups, firewall rules) without a clear ownership model.
- Not implementing idempotent scripts, resulting in duplicate or conflicting rules on repeated runs.
- Embedding environment‑specific values (IPs, ports, IDs) directly in scripts instead of using variables or templates.
- Skipping “dry‑run” or plan steps when using Infrastructure as Code tools, which removes a key safety net.
- Failing to version‑control policy files and Playbooks, making it hard to audit who changed what and when.
- Ignoring error handling and rollback logic, which can leave partial, inconsistent policies deployed.
- Not rotating automation credentials or using overly privileged service accounts for orchestration.
Monitoring, Audit and Incident Response Paths

Different organizations can choose among several patterns for operating and responding to segmentation‑related events. These alternatives can be combined where appropriate:
- Centralized SOC with integrated microsegmentation console – Logs from firewalls, agents, and cloud platforms feed a single SIEM; the SOC operates both detection and response. Best when you already have a mature SOC and can integrate more tools.
- DevSecOps‑driven model per product team – Product teams own their segmentation policies and monitoring dashboards, using guardrails defined by a platform security team. Suitable for organizations with strong DevOps culture and automation.
- Managed security services provider (MSSP) – Outsource monitoring, tuning, and some incident response to a partner, especially when introducing new ferramentas de segurança para segmentação de rede em cloud híbrida. Works well if you lack 24×7 coverage or in‑house expertise.
- Consulting‑led transition model – Engage consultoria em segmentação e microsegmentação de redes corporativas for design and initial implementation, then gradually transition operations to internal teams with documented runbooks and training.
Common Deployment Challenges and Solutions
How do I avoid breaking production traffic when enabling microsegmentation?
Start in monitor or simulation mode, build policies from observed flows, and enforce only during maintenance windows. Always have a documented rollback plan and test synthetic transactions for key applications immediately after policy changes.
How can I manage different policies across multiple clouds and on‑premises?
Define a common tagging and identity strategy, then use tools or platforms that can abstract policies across environments. Where a single platform is not available, express policies as code with shared templates and enforce them through CI/CD pipelines.
What if some legacy systems cannot run agents for microsegmentation?
Use network‑based segmentation (firewalls, VLANs, VRFs) around those systems and enforce strict perimeter rules. Combine this with jump hosts or Zero Trust access for administrative connections, and plan a long‑term modernization path.
How do I convince application owners to adopt stricter segmentation?
Show them concrete risk scenarios, then propose a phased rollout starting with read‑only monitoring and simulation. Involve them in validating required flows and provide clear evidence that safe guardrails and rollback options are in place.
How can I test segmentation policies before going live?
Use non‑production environments that mirror production as closely as possible, including IP ranges and routing. Run integration and performance tests, simulate failure scenarios, and, where possible, use canary enforcement for a subset of workloads.
What is the role of Zero Trust in hybrid cloud segmentation?
Zero Trust provides the overarching principle: never trust, always verify, and use strong identity for every connection. In practice, this means combining network segmentation with identity‑aware policies, encryption, and continuous evaluation of device and user posture.
How often should I review and update segmentation policies?
Review policies regularly as part of change management for new applications, migrations, and decommissions. Additionally, plan periodic holistic reviews to remove obsolete rules, tighten broad allows, and incorporate lessons from incidents or audits.