Zero Trust in cloud environments is a security model where no user, device, workload, or network is trusted by default, even inside your VPC or corporate VPN. Every access request is strongly authenticated, authorized, and continuously evaluated using identity, device posture, context, and risk, with fine-grained policies and segmentation.
Executive summary: Zero Trust essentials for cloud environments
- Zero Trust cloud segurança replaces implicit network trust with identity-, context-, and risk-based decisions for every request.
- Compared with perimeter firewalls and VPNs, Zero Trust is harder to design initially but reduces lateral movement and blast radius.
- Identity, device posture, and workload identities become the primary control plane, not IPs and subnets.
- Microsegmentation and service-level policies are mandatory to protect east-west traffic in multi-cloud and hybrid topologies.
- Automation and telemetry are critical; manual rule management does not scale for implementação zero trust na nuvem.
- Reference architectures and opinionated platforms shorten time-to-value but require alignment with your operating model.
- Common pitfalls: copying on-prem designs to cloud, over-trusting VPNs, and skipping continuous verification for “internal” apps.
Core principles of Zero Trust tailored for cloud platforms
In cloud platforms, Zero Trust means designing security around identities, applications, and data rather than around network locations. Instead of trusting anything because it sits in a private subnet, each request is evaluated using signals such as identity assurance, device health, workload tags, and behavior anomalies.
Compared to traditional perimeter-centric architectures, Zero Trust demands tighter integration with identity providers, cloud-native controls, and plataformas zero trust para ambientes multi-cloud. This increases initial complexity but dramatically reduces the risk of credential theft, misconfigured security groups, and flat internal networks being abused by attackers or malware.
Zero Trust cloud segurança in Brazil and other regions using pt_BR environments must also respect local compliance, data residency, and the specifics of each cloud provider. A practical view is: assume breach, minimize blast radius, verify each action, and log everything needed to investigate and tune policies.
At a high level, Zero Trust in the cloud rests on five core principles: strong identity for users and workloads, least-privilege access, microsegmentation, continuous verification and monitoring, and automated enforcement. Each of these has direct implementation constructs in major clouds (IAM, security groups, service mesh, conditional access, policy-as-code).
Identity and access controls: implementing adaptive authentication
Identity is the main control point for soluções zero trust para empresas. Adaptive authentication combines multiple signals to decide how, when, and whether to grant access.
- Centralize identity: Use a single IdP for workforce and a cloud IAM for workloads. Integrate SSO with all major SaaS and internal apps to reduce local accounts and “shadow” identity stores.
- Strong authentication: Enforce phishing-resistant MFA (FIDO2, security keys, modern platform authenticators) especially for privileged access and sensitive cloud consoles.
- Context-aware policies: Adapt access requirements based on device compliance, user role, location, and risk signals (impossible travel, anomalous behavior) instead of fixed rules.
- Just-in-time and least privilege: Replace permanent admin roles with time-bound elevation; grant permissions only for specific tasks or projects and revoke them automatically.
- Workload identities: Use managed identities, service principals, or workload identity federation instead of static API keys or long-lived secrets embedded in code or CI pipelines.
- Granular authorization: Enforce access at the application and API layer (ABAC/RBAC), not only via network controls. Tie policies to attributes like project, data classification, and environment.
- Continuous session evaluation: Re-evaluate risk throughout the session; trigger step-up authentication or revoke tokens on suspicious behavior or device posture changes.
Microsegmentation and network architecture in multi-cloud setups
Microsegmentation limits the impact of an attacker who already has some level of access. In multi-cloud scenarios, it must work consistently across VPCs, VNets, and on-prem networks, often via service meshes, cloud firewalls, and software-defined per-workload policies.
- Environment segmentation: Strictly isolate dev, test, staging, and production networks. Prevent direct connectivity from low-trust environments into production; use controlled CI/CD paths instead.
- Application tier separation: Segment presentation, API, and data layers using security groups, network security policies, and service meshes. Only allow explicit, minimal flows (for example: web → API → DB).
- Workload identity-based access: Use labels, tags, and identities instead of IPs to define communication rules. This makes policies portable across regions and clouds and simplifies refactoring.
- Multi-cloud connectivity: For plataformas zero trust para ambientes multi-cloud, route traffic through a central Zero Trust access layer or cloud security broker instead of full mesh VPNs that create a huge trust zone.
- East-west visibility: Instrument network telemetry (flow logs, service mesh metrics) to see lateral movement attempts and tune microsegmentation without breaking legitimate traffic.
- Legacy and hybrid integration: For on-prem systems, use application-level proxies or identity-aware gateways to front legacy apps, avoiding direct flat network extensions into the cloud.
Data protection: classification, encryption, and tokenization strategies
Zero Trust focuses heavily on the data itself. For implementação zero trust na nuvem, classification and encryption decisions should be consistent across providers and aligned with business impact, not only with technical convenience.
- Advantages of robust data classification and encryption
- Clear mapping between sensitivity levels and required controls (encryption, access approval flows, monitoring intensity).
- Cloud-native encryption-at-rest and in-transit are easier to standardize and automate than custom solutions.
- Tokenization and field-level encryption reduce the exposure of personal or financial data in logs, analytics, and lower environments.
- Helps prioritize Zero Trust investments towards the data stores that really matter (crown jewels).
- Improves compliance alignment (LGPD and similar laws) through demonstrable controls over personal data.
- Limitations, risks, and trade-offs to watch
- Over-classification leads to operational friction and developers bypassing controls to deliver features on time.
- Key management complexity; poorly rotated or centrally exposed keys undermine all encryption benefits.
- Tokenization can complicate analytics and data science if not planned with reversible vs. irreversible uses in mind.
- Relying only on provider-managed defaults without reviewing configurations can create blind spots in multi-cloud setups.
- Excessive encryption layers may increase cost and latency without proportionate risk reduction.
Automation, telemetry, and continuous policy enforcement
Zero Trust is fragile without automation and good telemetry. Manual rule creation and ticket-based access approvals do not scale for modern cloud workloads and frequently introduce inconsistent or conflicting policies.
- Myth: Zero Trust is a “one-time migration”. In reality, policies must evolve continuously with new applications, identities, and threats. Treat it as an operating model, not a project.
- Myth: More rules mean more security. Large, unstructured rule sets usually hide misconfigurations. Prefer high-level, attribute-based policies enforced via automation and policy-as-code.
- Mistake: No centralized logging strategy. Scattered logs across clouds, SaaS, and on-prem prevent effective detection and response. Use a SIEM or data lake with normalized events.
- Mistake: Ignoring user and developer experience. Overly strict controls with no exception path drive shadow IT and insecure workarounds. Balance trust decisions against usability and provide clear, quick remediation flows.
- Myth: VPN equals Zero Trust. VPNs extend networks; Zero Trust reduces implicit trust. Relying solely on VPNs for remote access keeps the same lateral movement risks inside your cloud workloads.
- Mistake: No feedback loop from incidents. Failing to translate incident learnings into new policies and detections keeps you vulnerable to repeat attacks.
Reference architecture blueprint: components, flows, and integration patterns
An arquitetura de referência zero trust cloud helps avoid ad‑hoc designs. A typical blueprint for Brazilian enterprises using multiple providers might combine identity-centric access, cloud-native controls, and specialized Zero Trust platforms.
A simplified reference architecture usually includes:
- Central Identity Provider (IdP) with SSO and MFA for workforce access.
- Cloud IAM and workload identities in each provider for services and automation.
- Zero Trust Network Access (ZTNA) or identity-aware proxy in front of internal apps and admin consoles.
- Service mesh or cloud firewalls for microsegmentation and service-to-service policies.
- Data protection services: KMS/HSM, DLP, tokenization for sensitive datasets.
- SIEM/SOAR or logging platform aggregating cloud, IdP, and application events.
- Policy-as-code engine (for example: Terraform with guardrails, OPA, or cloud-native policy frameworks).
High-level request flow (user to internal web app):
- User connects via ZTNA portal and is redirected to the IdP for SSO and MFA.
- IdP evaluates risk (device compliance, location, behavior) and issues a short-lived token.
- ZTNA checks the token, maps user attributes (role, group, department) to access policies, and forwards traffic only to allowed apps.
- Inside the cloud, microsegmentation rules and service mesh policies ensure the web app can call only specific APIs and databases.
- All decisions and traffic metadata are logged to the SIEM for monitoring and tuning.
Compared to a classic VPN plus flat VPC approach, this arquitetura de referência zero trust cloud is more complex to deploy but significantly reduces the risk of a single compromised laptop or credential providing wide access to your entire environment.
To compare adoption effort and risk between approaches:
| Approach | Ease of initial deployment | Ongoing operational complexity | Residual lateral movement risk | Fit for multi-cloud |
|---|---|---|---|---|
| Traditional VPN + flat VPCs | Relatively easy (well-known pattern) | Moderate (manual firewall rules, IP management) | High (one foothold often reaches many systems) | Poor (complex meshes, overlapping IPs) |
| Network-centric Zero Trust (microsegmentation only) | Medium (requires re-architecture of subnets and rules) | High (large rule sets, hard troubleshooting) | Medium (better containment but identity blind spots) | Medium (policies must be duplicated per cloud) |
| Identity-centric Zero Trust with ZTNA + microsegmentation | Harder (IdP, ZTNA, app integration, culture change) | Medium (automation and policy-as-code reduce toil) | Low (fine-grained, context-aware controls) | Good (policies based on identity and tags, not IP) |
Many organizações choose soluções zero trust para empresas that bundle several of these components (IdP, ZTNA, CASB, posture management). These platforms accelerate Zero Trust adoption but can introduce lock-in, so they should be evaluated against cloud-native options and your long-term multi-cloud strategy.
Quick implementation self-check

- Have you defined a minimal reference architecture and phased roadmap instead of isolated Zero Trust pilots?
- Are identities (users and workloads) centralized with strong MFA and just-in-time privileges?
- Is there clear segmentation between environments and critical applications, with policies tied to attributes, not IPs?
- Do you have unified logging and monitoring across IdP, clouds, and Zero Trust components?
- Is policy management automated (infrastructure-as-code, CI/CD) rather than handled through manual firewall tickets?
Practical queries on deployment, scaling and troubleshooting
How do I start Zero Trust in the cloud without redesigning everything?
Begin with identity: consolidate SSO, enforce MFA, and protect admin access to cloud consoles. Then introduce ZTNA for a few internal apps and tighten network access around critical workloads. Expand microsegmentation and policy automation iteratively instead of a big-bang migration.
Which is safer: VPN access or ZTNA for internal cloud applications?
ZTNA is generally safer for cloud workloads because it grants access per application based on identity and context, not broad network reach. VPNs extend your internal network to the endpoint, which increases lateral movement risk if the device or credentials are compromised.
How can I avoid breaking applications when I implement microsegmentation?
Start in “observe” mode using flow logs or a service mesh to learn traffic patterns. Create policies based on actual dependencies, then enforce them gradually, starting with non-critical environments. Always involve application owners in reviewing and validating proposed rules.
Do I need a dedicated Zero Trust platform, or can I use only cloud-native tools?
You can go far with cloud-native IAM, firewalls, and logging, especially in a single-cloud strategy. Dedicated Zero Trust platforms add consistency and visibility across multi-cloud and SaaS but must be evaluated for integration effort, feature overlap, and vendor lock-in.
How do I measure whether my Zero Trust efforts are reducing risk?
Track metrics like reduced standing privileges, smaller reachable attack surface from a single compromised account, time to detect and contain incidents, and coverage of critical apps with ZTNA and microsegmentation. Use tabletop exercises and red teaming to validate assumptions.
What are typical performance impacts of Zero Trust controls?
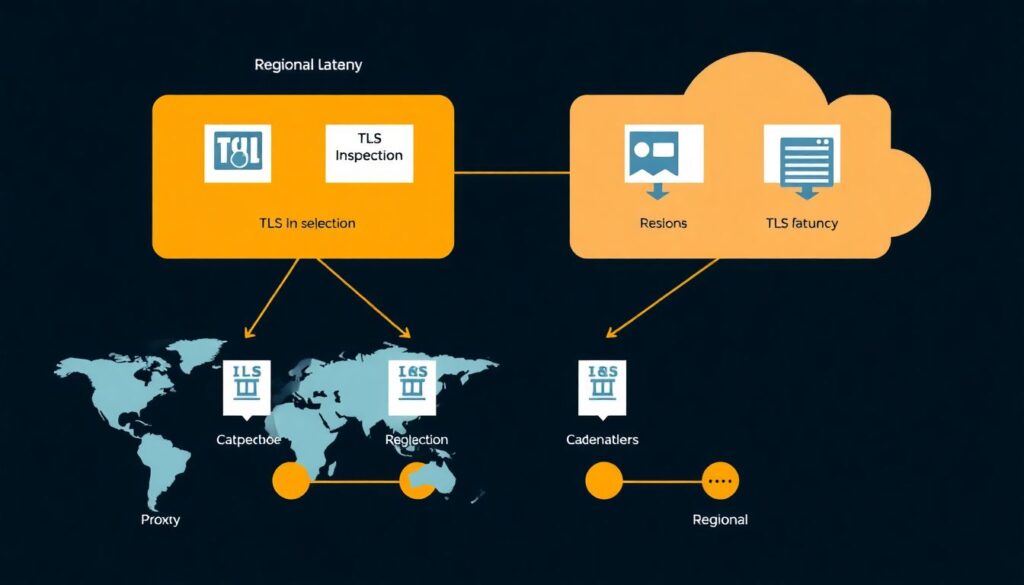
There can be small latency increases from proxies, additional TLS handshakes, and inspection. Well-designed architectures mitigate this with regional deployments, caching, and modern protocols. Most organizations find the trade-off acceptable compared with the risk reduction gained.
How does Zero Trust work for legacy on-prem systems connected to the cloud?

Place identity-aware proxies or ZTNA connectors in front of legacy apps, so access is controlled by modern identity and policy engines. Avoid flat network extensions; instead, limit connectivity to specific application flows and monitor them closely.