Categoria: Guias
-

Serverless incident monitoring and response: challenges and best practices
Serverless incident monitoring and response means collecting focused telemetry from functions, detecting failures or attacks quickly, and executing repeatable runbooks that are safe to automate. For teams in Brazil (pt_BR context), this guide gives concrete patterns, tool choices, and step‑by‑step actions that work across AWS and multi‑cloud environments. Core objectives for serverless incident monitoring Detect…
-
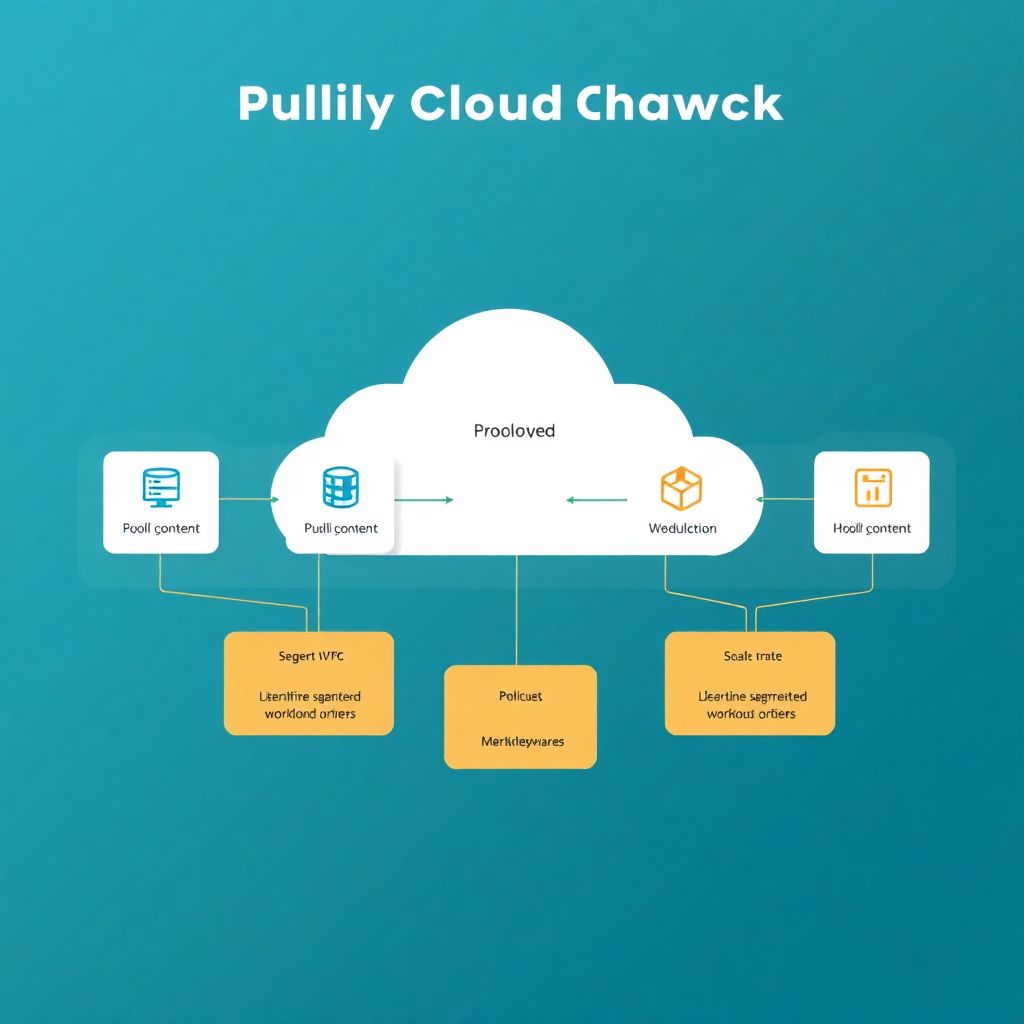
Advanced network segmentation and microsegmentation strategies in public cloud
Advanced network segmentation and microsegmentation in public cloud means combining coarse VPC/subnet isolation with fine‑grained, identity‑aware policies at workload and service level. For pt_BR environments, prioritize simple, auditable controls, progressive rollout, and clear rollback paths while aligning with zero‑trust. Start with critical workloads, then gradually expand segmentation coverage. Essential design principles for cloud network segmentation…
-

Cloud backup and disaster recovery manual: Rpo, Rto, restore testing pitfalls
Use business-focused cloud backup and disaster recovery to define RPO and RTO per workload, automate backups, and frequently test restores. Start with critical systems, choose a solução de disaster recovery em nuvem that matches your compliance and latency needs, and document clear, repeatable recovery runbooks your operations team can execute safely during an incident. Essential…
-

Casb tools review: key features that matter for mid and large enterprises
For medium and large Brazilian companies evaluating CASB, focus on visibility into sanctioned and shadow SaaS, strong DLP for sensitive data, deep identity integration, threat analytics, and a deployment model (API, proxy, or hybrid) that fits your network reality. Then balance capabilities against operational complexity, integration effort, and long‑term vendor viability. Critical CAPABILITIES to weigh…
-
Kubernetes cloud incident monitoring and response: tools, logs and best practices
Monitoring and incident response for Kubernetes in cloud environments means collecting the right telemetry (logs, metrics, traces, events), using integrated security and observability tools, defining clear alerts and playbooks, and practicing safe containment actions. This guide focuses on monitoramento Kubernetes na nuvem with practical, low‑risk steps suitable for intermediate engineers in Brazil. Essential insights for…
-

Secure public cloud landing zone: reference architecture and essential controls
When teams start talking about “secure-by-design cloud”, sooner or later the conversation chega naquele ponto chato: fundações. A tal da landing zone em cloud pública parece abstrata, mas é basicamente o conjunto de contas, redes, identidades, políticas e automações que definem como a sua empresa vai usar a nuvem pelos próximos anos. É a diferença…
-
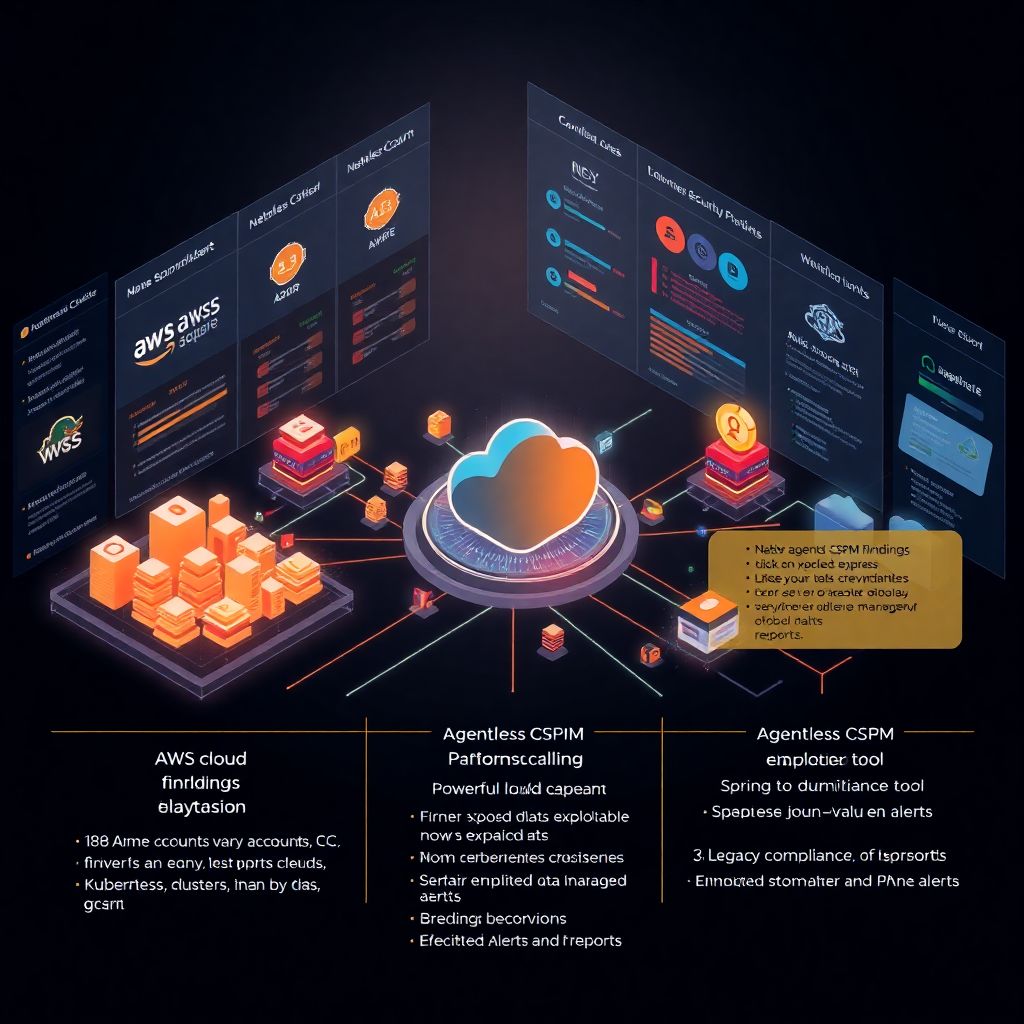
Cspm tools compared: technical cloud security posture management for large enterprises
Por que CSPM virou tema de conselho de administração Cloud security posture management deixou de быть tópico “de time de segurança” e virou assunto de risco corporativo. Em grandes empresas, особенно com dezenas de contas AWS, subscriptions Azure e projetos GCP, ninguém mais consegue saber manualmente se todos os buckets, VPCs, roles e chaves estão…
-
Cloud security automation with terraform, ansible and Ci/cd pipelines
Por que automatizar segurança em cloud deixou de ser opcional A automação de segurança em cloud com Terraform, Ansible e pipelines CI/CD virou questão de sobrevivência, não de modinha tecnológica. Entre 2023 e 2025, a adoção global de infraestrutura como código em ambientes de nuvem passou de cerca de 37% para algo perto de 60%,…
-

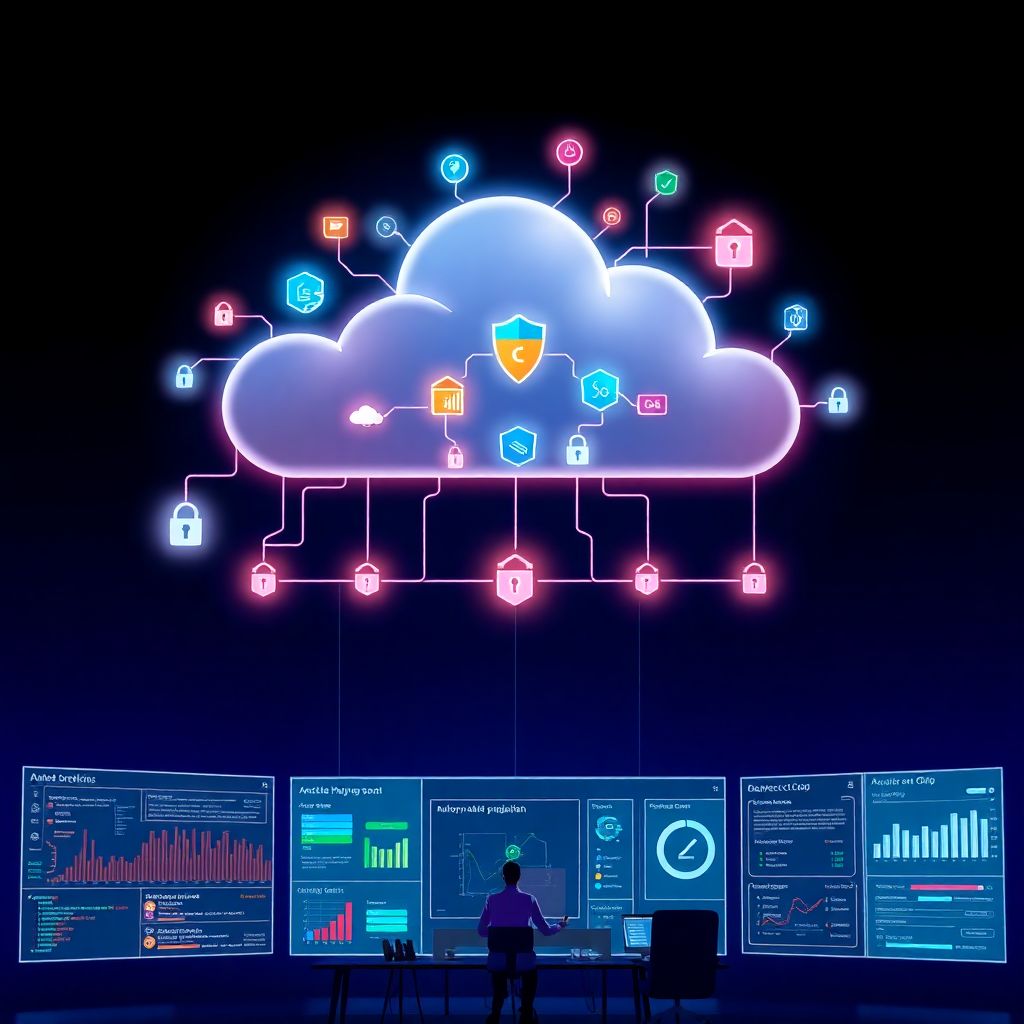
Cloud cybersecurity trends: emerging risks and predictions for coming years
Por que as tendências em cibersegurança cloud importam agora Quando a gente fala em tendências em cibersegurança em cloud 2025, não é futurologia de conferência: é planejamento de sobrevivência do negócio. Cibersegurança cloud é o conjunto de práticas, ferramentas e processos para proteger dados, workloads e identidades que rodam em provedores como AWS, Azure ou…
-
Zero trust in multi-cloud environments: implementing effective least-privilege access
Why Zero Trust in Multi‑Cloud Isn’t Optional Anymore If your company is running workloads in AWS, Azure, GCP and maybe a SaaS or two, you’re already in a zero trust multi cloud reality — whether you planned it or not. Users connect from everywhere, apps talk to each other across regions, and attackers only need…