Categoria: Guias
-
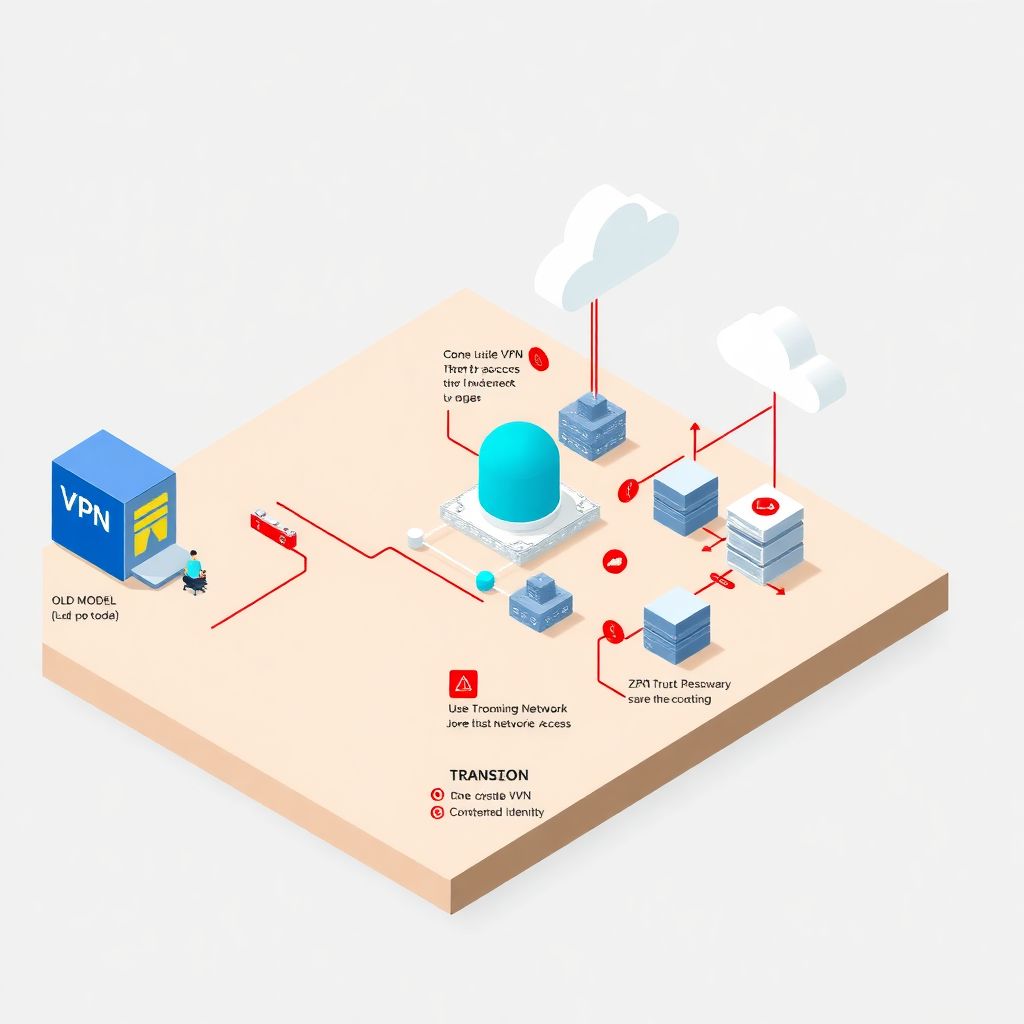
Remote cloud access security with Vpn, Ztna and federated identity
Why remote access to cloud infrastructure is harder than it looks When everything moved to “the cloud”, most companies quietly kept one very old habit: putting a VPN in front of everything and calling it a day. That worked when: – 90% of people were in the office – apps lived in one or two…
-
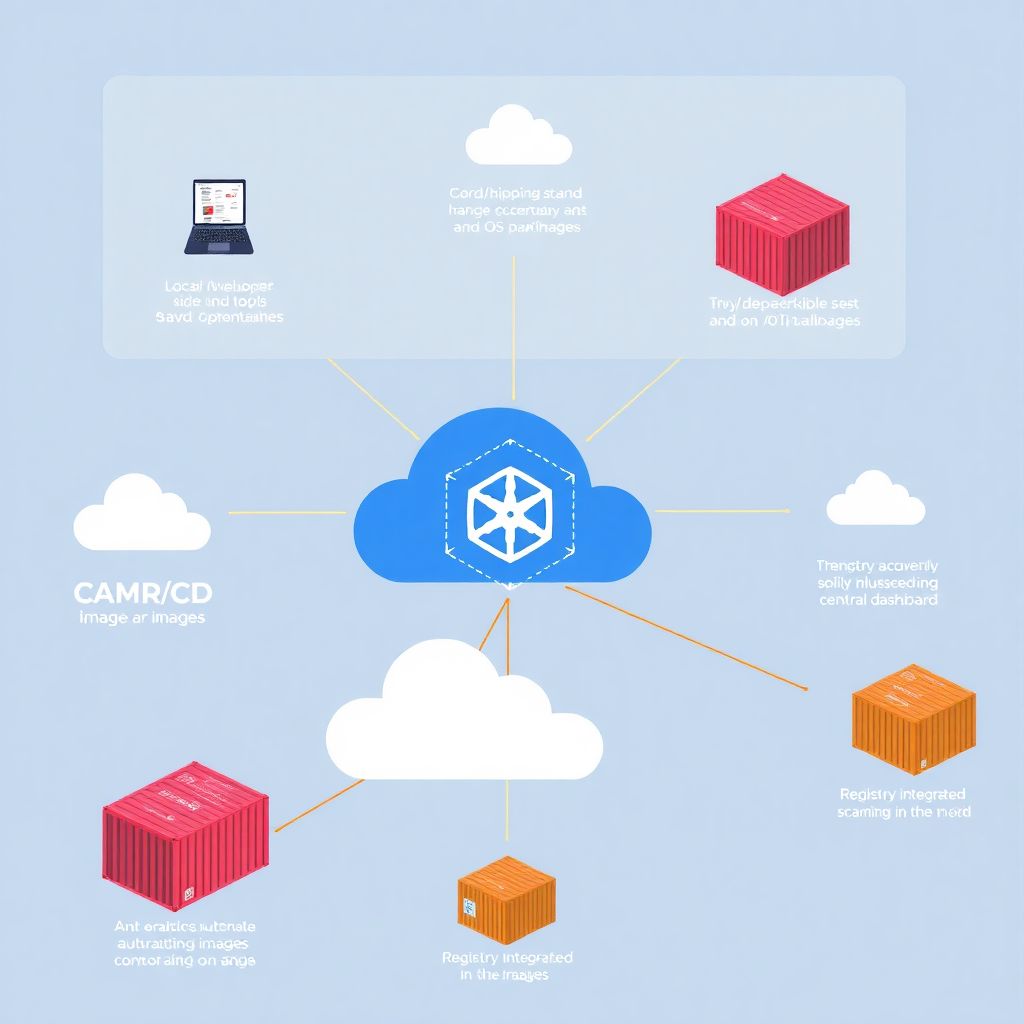
Container image vulnerability analysis with cloud registry security scanners
Why container vulnerability analysis in the cloud is trickier than it looks When you move workloads into Kubernetes or any other orchestration platform, it’s tempting to think: “I’m using official Docker images, I’m fine.” That’s usually wrong. Base images arrive with outdated libraries, teams add random tools during debugging, and images keep living in registries…
-
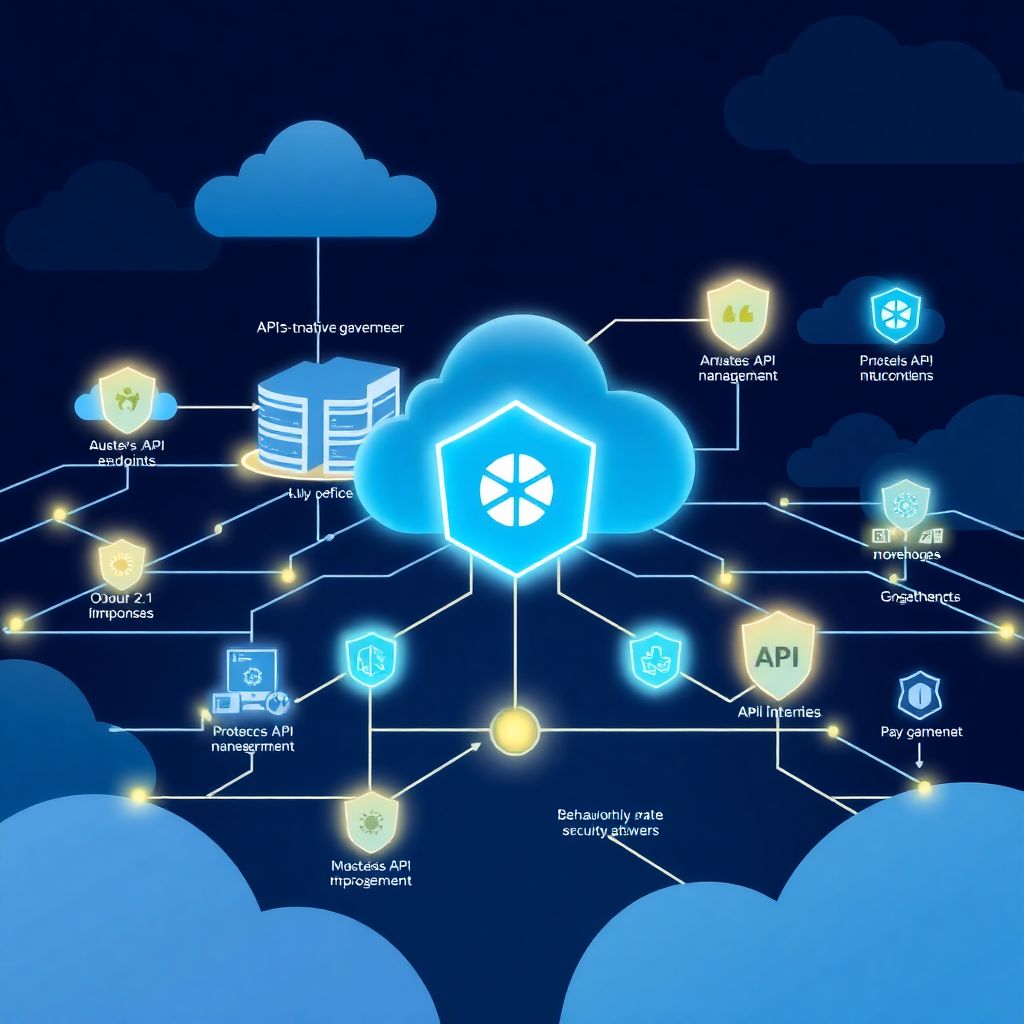
Cloud-native Api protection: auth, access control, rate limiting, public Api security
Почему защита API в cloud-native стала критически важной За последние три года API превратились из “внутреннего транспорта данных” в основной периметр безопасности. Gartner ещё в 2022 году прогнозировал, что к 2025 году API станут самым частым вектором атак, и этот прогноз уже подтвердился: по данным Verizon DBIR 2023–2025, доля инцидентов, напрямую связанных с API, стабильно…
-

Backup, disaster recovery and business continuity in cloud resilient architectures
Why resilience in the cloud matters From backup to full business survival When people first move systems to the cloud, they often think “the provider takes care of everything” and stop there. In reality, cloud only changes *how* you design resilience, not *whether* you need it. A simple backup will save your data, but it…
-
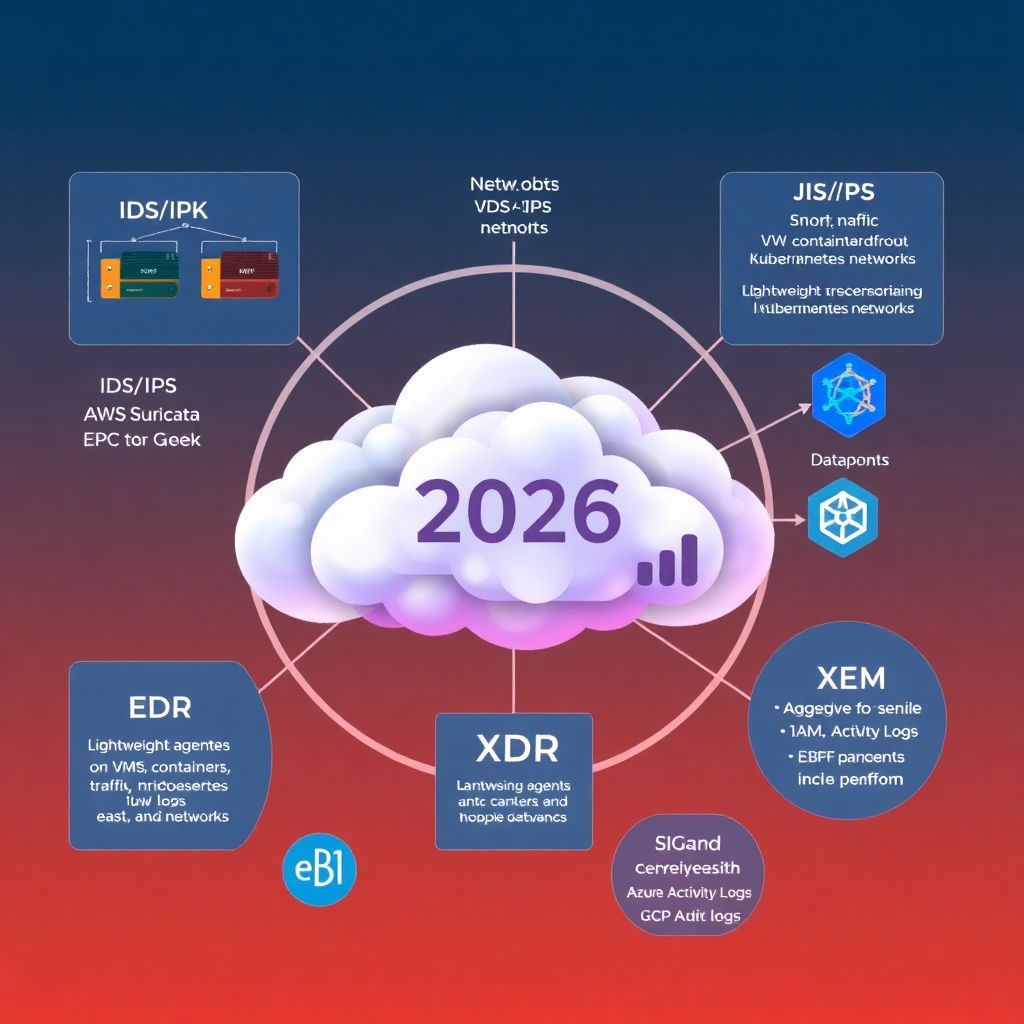
Open source cloud threat detection tools review: Ids/ips, Edr and Xdr
Por que todo mundo fala de IDS/IPS, EDR e XDR em cloud agora Cloud deixou de ser “novidade” faz tempo. Em 2026, praticamente toda empresa que leva segurança a sério já passou (ou está passando) por uma migração de parte do SOC para a nuvem. E aí aparece a pergunta incômoda: como manter visibilidade e…
-
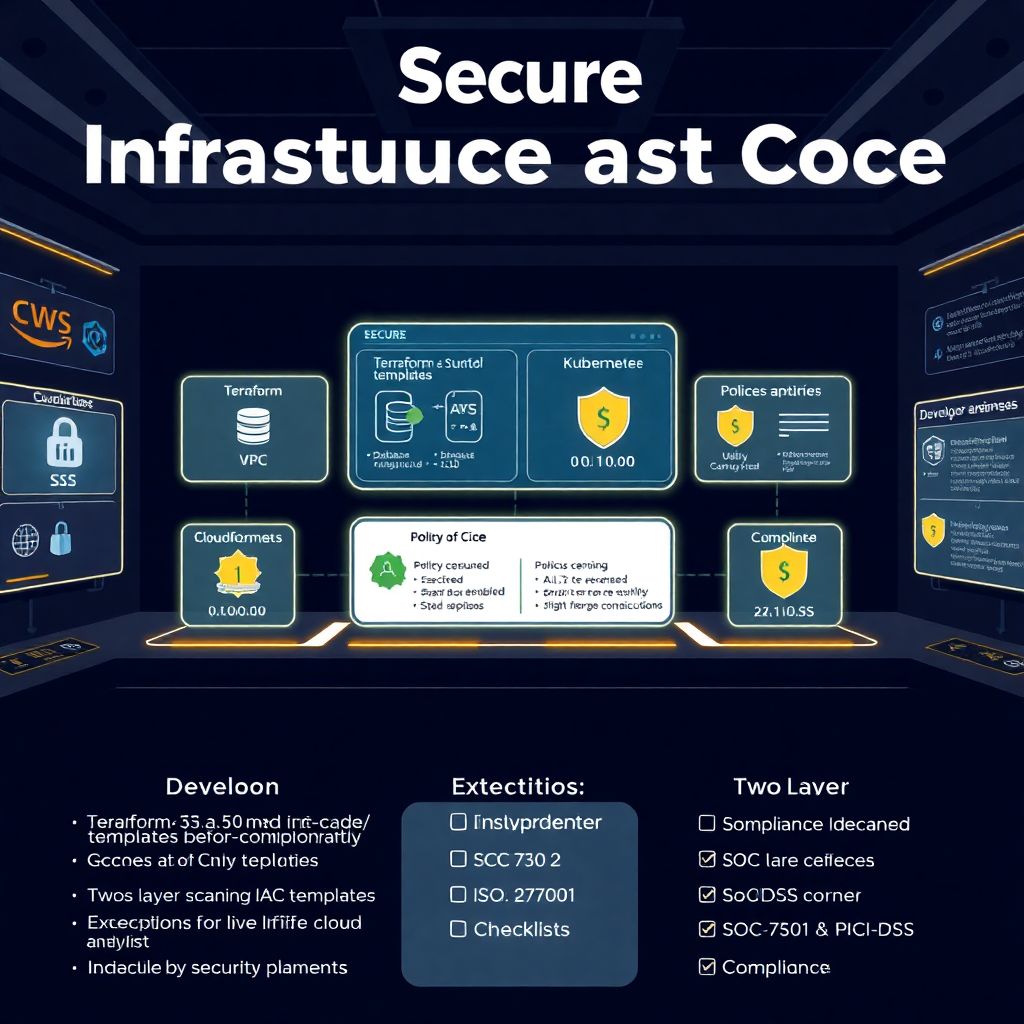
Infrastructure as code (iac) security: patterns, policies and template scanning
Why secure IaC is harder than it looks Most teams adopt Infrastructure as Code for speed, not for segurança, и это быстро мстит. One day you’re happily merging Terraform; a month later вы обнаруживаете, что половина S3-бакетов публичны, а в security group открыт 0.0.0.0/0. Именно здесь начинается разговор про infraestrutura como código segurança boas práticas….
-
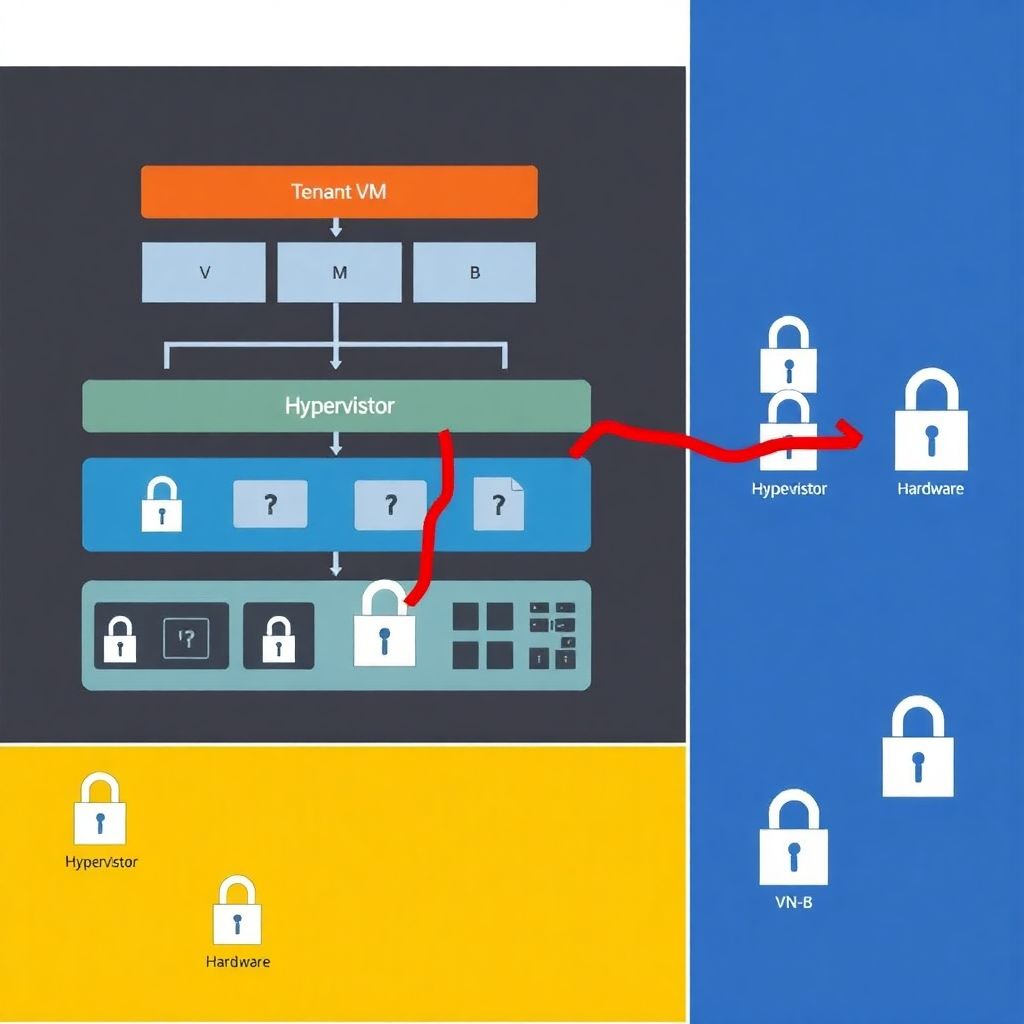
News: impact of recent hypervisor and isolation failures on major cloud providers
Why hypervisor isolation bugs in big clouds matter right now Over the last few years, cloud security headlines have shifted from “misconfigured S3 bucket” to “hypervisor escape lets attacker jump between tenants.” That’s a big deal: hypervisors and hardware isolation are the last line of defense between your VM and someone else’s. When that layer…
-
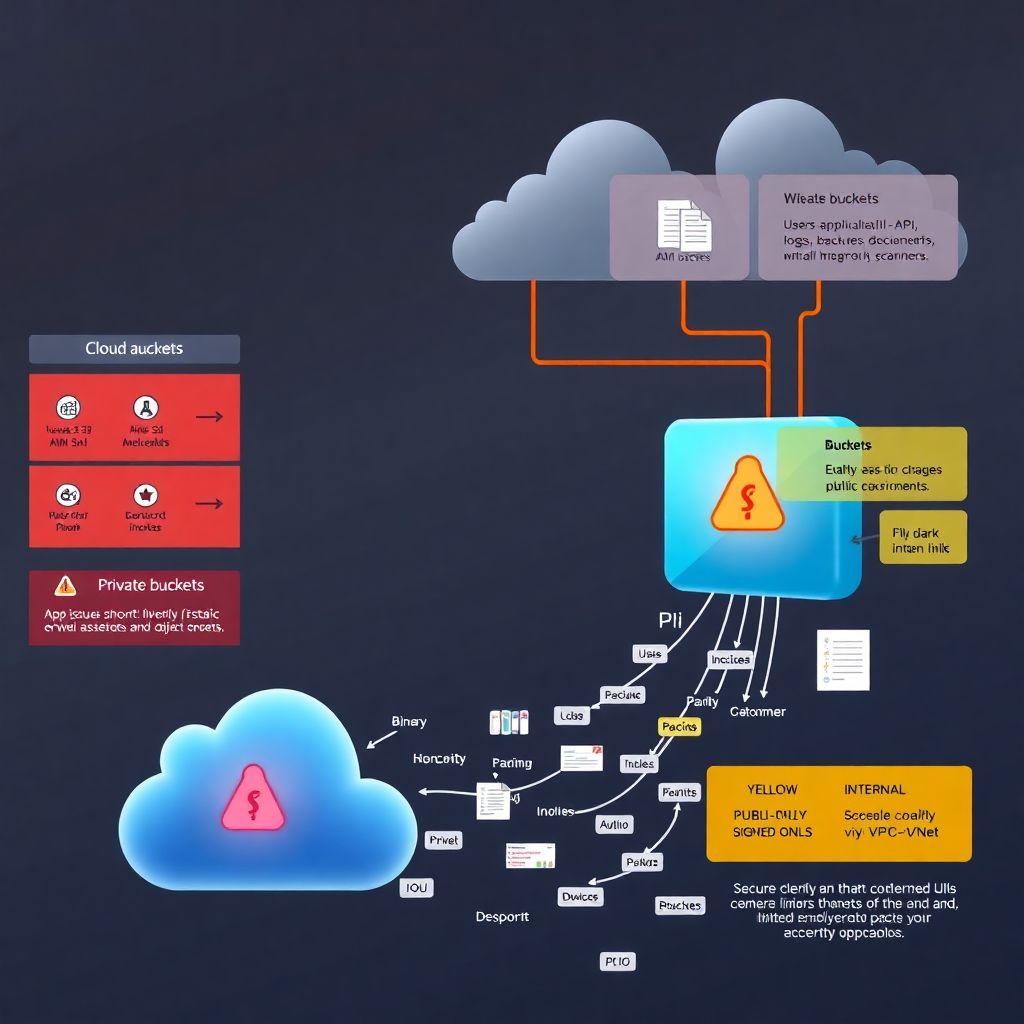
Secure cloud bucket and storage configuration guide to prevent data leaks
Why bucket misconfiguration is still the easiest way to leak everything If something in your cloud setup is going to leak data, odds are it’s not a zero‑day exploit. It’s a bucket with the wrong permissions. S3, GCS, Azure Blob, MinIO, Backblaze — different brands, same story: one checkbox, one wildcard (`*`), and suddenly your…
-

Cloud incident response: how to handle incidents with plans, tools and playbooks
Por que incidentes em cloud são diferentes (e mais complicados) em 2026 Se você já lidou com incidente em servidor físico lá nos anos 2000, lembra como era: entrar no datacenter, puxar cabo, reiniciar máquina, olhar log local. Em 2026, incidentes em ambientes cloud acontecem em um cenário totalmente diferente: dezenas de contas, múltiplas regiões,…
-

Cspm cloud security posture management: how to structure a program in your company
Por que sua empresa precisa levar CSPM a sério agora Programas de Cloud Security Posture Management deixaram de ser “nice to have” e viraram item de sobrevivência digital. À medida que times sobem tudo para nuvem em ciclos cada vez mais curtos, a superfície de ataque explode e ninguém consegue revisar manualmente cada configuração de…