Categoria: Manuais
-

Future trends in cloud cybersecurity driven by Ai, automation and autonomous defense
Future cloud security will be dominated by AI-driven detection, policy‑aware automation and progressively autonomous defense. For a Brazilian mid‑size company, the practical move is to centralize logs, plug in cloud‑native AI analytics, automate the top five incident responses, and keep a human in the loop for all high‑impact actions. Executive snapshot of imminent cloud-security shifts…
-
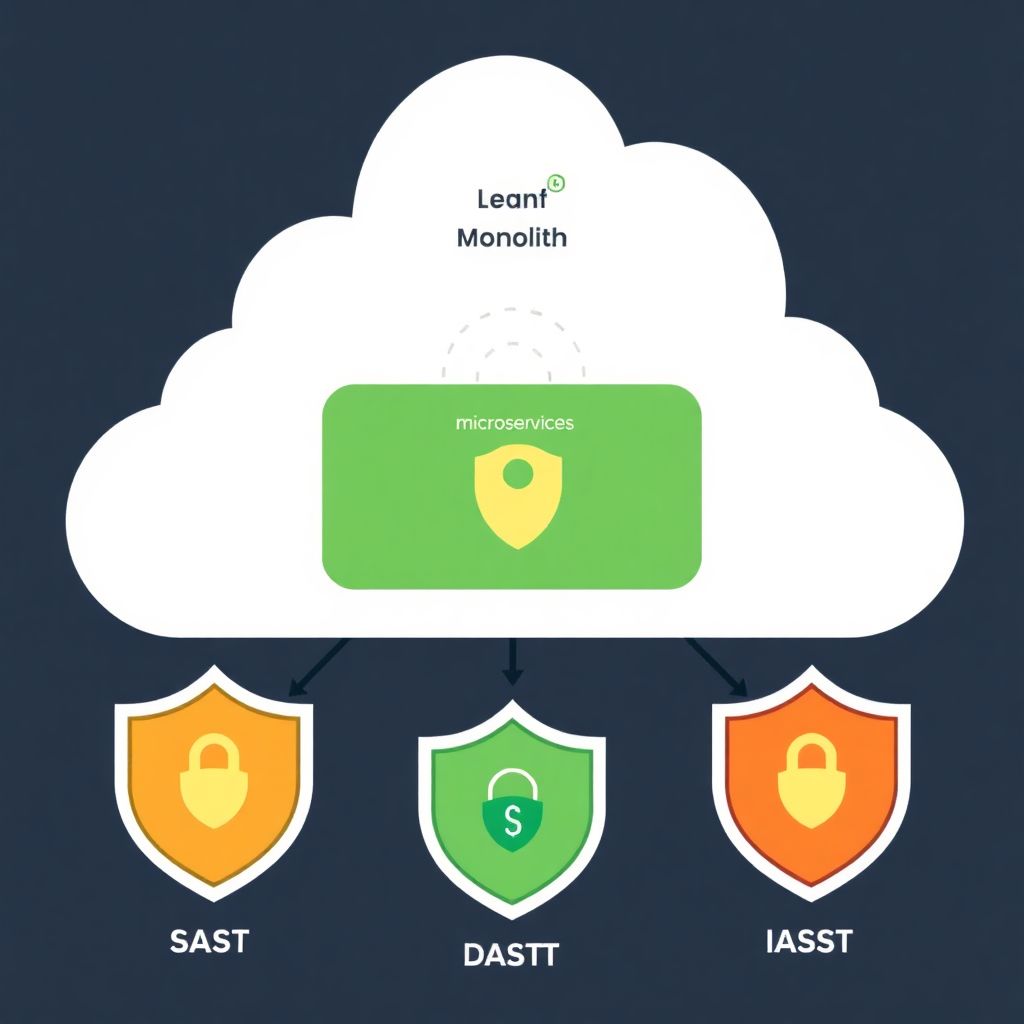
Sast, Dast and Iast tools review for securing cloud-hosted applications
Cloud-hosted applications benefit most from a combined approach: SAST for early code issues, DAST for exposed runtime flaws and IAST where you need deep insight in complex cloud-native stacks. The best choice depends on your architecture (monolith, microservices, serverless), compliance needs, team skills and how tightly you integrate security into CI/CD. Executive summary: cloud-native SAST,…
-

Remote work security: protecting cloud access with advanced Iam, Sso and Mfa
To secure remote work access to cloud services, centralize identities with strong IAM, route all access through enterprise SSO, and enforce adaptive MFA everywhere. Combine least privilege, just-in-time elevation, and continuous monitoring. Start with critical apps, roll out in phases, and keep controls simple enough that remote users actually follow them. Priority controls overview for…
-

Common cloud storage configuration errors that expose sensitive data and fixes
Common cloud storage misconfigurations that expose sensitive data include public buckets, permissive IAM policies, unprotected backups, weak encryption, missing logs, and leaked credentials in CI/CD. To achieve armazenamento em nuvem seguro para empresas, you must standardize secure defaults, automate checks, and continuously verify that every new resource follows the same hardened baseline. Primary misconfigurations that…
-

Cloud security policy automation with iac using terraform and cloudformation
Cloud security policy automation with Infrastructure as Code means encoding guardrails (network, identity, encryption, logging, compliance) directly into Terraform or CloudFormation. You validate every change in CI/CD before it reaches the cloud. This guide shows safe, practical steps, tools, and examples suitable for intermediate teams in Brazil (pt_BR context). Core security objectives for IaC-driven cloud…
-

How to create an incident response runbook for hybrid cloud environments
A hybrid-cloud incident response runbook is a structured, step‑by‑step playbook that unifies on‑prem and cloud procedures, tools and roles. It defines triggers, actions and verification for common incidents, so teams in Brazil can respond consistently, safely and quickly across AWS/Azure/GCP plus data centers and private clouds. Essential Incident Response Objectives for Hybrid Clouds Ensure consistent…
-

Multicloud security strategy for large enterprises: building robust protection
A robust multicloud security strategy for large Brazilian enterprises aligns governance, identity, networking, data protection, and operations across providers. Start by defining shared policies, unify identity and access controls, standardize network segmentation, enforce encryption and DLP, centralize logging and detection, and automate with secure IaC and clear vendor governance for every cloud environment you adopt….
-
Cloud cybersecurity trends: Ai, Sase and secure-by-design for the coming years
Cloud security in the next years will be dominated by AI analytics, SASE consolidation, Secure by Design practices, Zero Trust, and continuous compliance. For Brazilian organizations, safe progress means piloting each trend in small scopes, measuring risk reduction versus cost, and combining automation with clear processes and realistic skills planning. Strategic snapshot of upcoming cloud-security…
-

Cloud security news and analysis: recent leaks and key lessons to learn
Recent cloud leaks are large-scale exposures of data stored in cloud services, usually caused by misconfigurations, weak identity controls or third‑party failures. Analysing these incidents shows that companies in Brazil and globally must harden basics first: identity, network segmentation, logging and vendor management, prioritising measures by ease of implementation and risk reduction. Immediate implications of…
-

Ci/cd security in cloud-native pipelines: protecting code from commit to production
Secure CI/CD pipelines in cloud-native environments means hardening every hop from commit to production: source control, build systems, artifacts, deployments, secrets, and observability. This guide gives concrete, safe steps and checklists so intermediate teams can improve segurança em pipelines CI/CD without breaking delivery speed, reliability, or developer experience. Security snapshot: core protections for cloud-native CI/CD…