Categoria: Manuais
-

Zero trust in the cloud: implementing perimeterless security in multi-cloud environments
To implement a true perimeter-less zero trust na nuvem multi cloud, you map identities, devices, networks and data across all providers, enforce least privilege via identity-first controls, segment traffic with microperimeters, encrypt and classify data consistently, and continuously verify behavior with unified logging, automation and policy-as-code integrated into CI/CD. Core Principles for Zero Trust in…
-

How to protect sensitive data in cloud data lakes with masking and access control
To protect sensitive data in cloud data lakes, classify information, segment storage and networks, apply data masking and tokenization, and enforce strong access control with continuous monitoring. Combine security controls of your cloud provider with governance processes, focusing on least privilege, auditable configurations, and reversible protections aligned with legal and business requirements. Protection objectives and…
-

Cloud cybersecurity news: recent attacks and lessons on misconfiguration flaws
Recent cloud breaches show a clear pattern: most successful attacks do not exploit unknown bugs, but simple configuration mistakes in storage, identity, network exposure and logging. For teams in Brazil prioritising cibersegurança em cloud principais ameaças 2024, the fastest gains come from hardening defaults, standardising baselines and continuously validating configurations. Immediate Insights: What Recent Cloud…
-

Container vulnerability detection and analysis in cloud registries with automation
Cloud container vulnerability detection means scanning images in registries and running containers for known flaws, misconfigurations and secrets, then prioritising and fixing issues automatically. Use cloud‑native registries, integrated scanners and CI/CD gates to keep images safe. Start with inventory, then add automated scans, runtime monitoring and structured patch and rollback procedures. Prep checklist: essential steps…
-

Security in multi-cloud and hybrid environments: standardizing policies
To standardize security across multi-cloud and hybrid environments, define one reference security baseline, express it as code, then enforce it through centralized identity, network, data protection and monitoring controls across all providers. Use vendor-neutral tools where possible, and adapt only the minimal provider-specific exceptions needed for Brazilian and global regulatory requirements. Essential controls for harmonized…
-
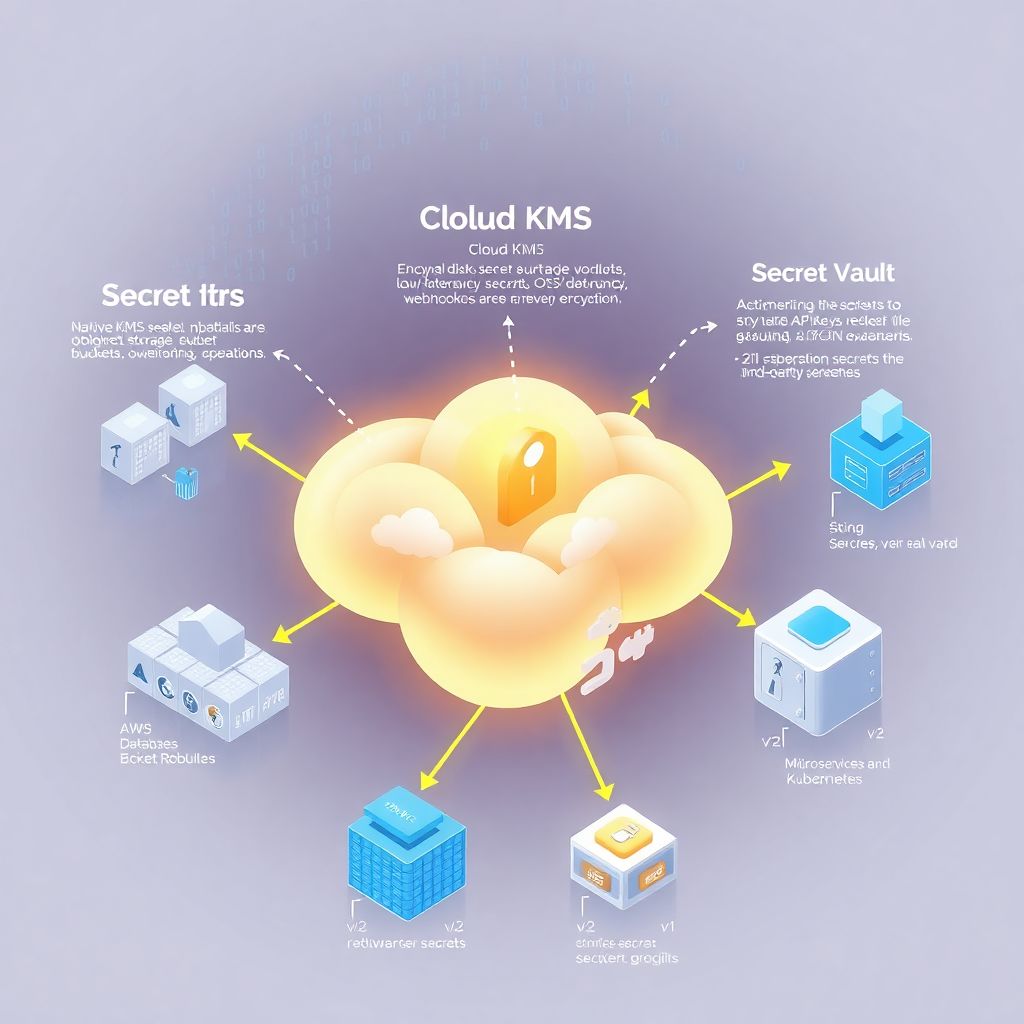
Cloud key and secret management: comparing native Kms, secret vaults and third‑party tools
Por que gestão de chaves e segredos na nuvem virou assunto de sobrevivência Quando a infraestrutura vai para a nuvem, a segurança deixa de ser только про «поставить хороший firewall». Сегодня основные утечки связаны не с взломом периметра, а с тем, что кто‑то оставил токен в GitHub или ключ шифрования в старом backup. Gestão de…
-

Incident response in cloud for Soc teams: building playbooks and simulations
Why cloud incident response feels different (and why your SOC must adapt) In on‑prem environments, incident response is often linear: detect, contain, eradicate, recover. In cloud, the same playbook breaks quickly. Identities are ephemeral, workloads autoscale, logs se espalham em vários serviços, and a “server” might be a short‑lived container that vanished 5 minutes ago….
-

Ransomware resilience in cloud with secure backup, data immutability and recovery
The moment you move critical workloads to the cloud, you’re not just buying elasticity and convenience — you’re also inheriting a new attack surface for ransomware. And attackers already know your backups are the last line of defense, so they go after them first. That’s why “resiliência a ransomware em cloud” isn’t a buzzword; it’s…
-
Cloud vulnerability remediation: from discovery to automated Ci/cd fixes
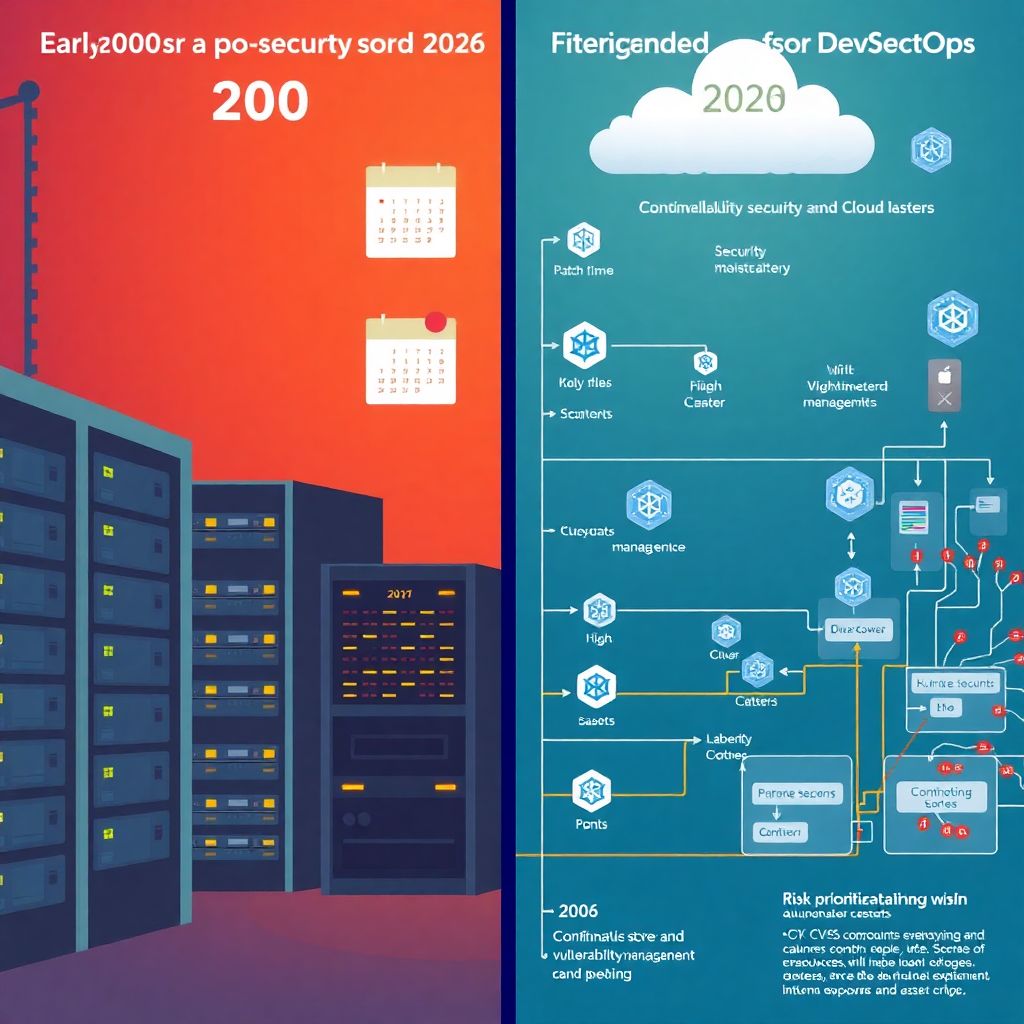
From “Patch Tuesday” to real‑time cloud defense Back in the 2000s security meant “Patch Tuesday”, nightly maintenance windows and a couple of firewalls humming in the data center. Fast‑forward to 2026: apps are rebuilt dozens of times per day, infra is ephemeral and attackers use automation as aggressively as we do. In this world, tratamento…
-
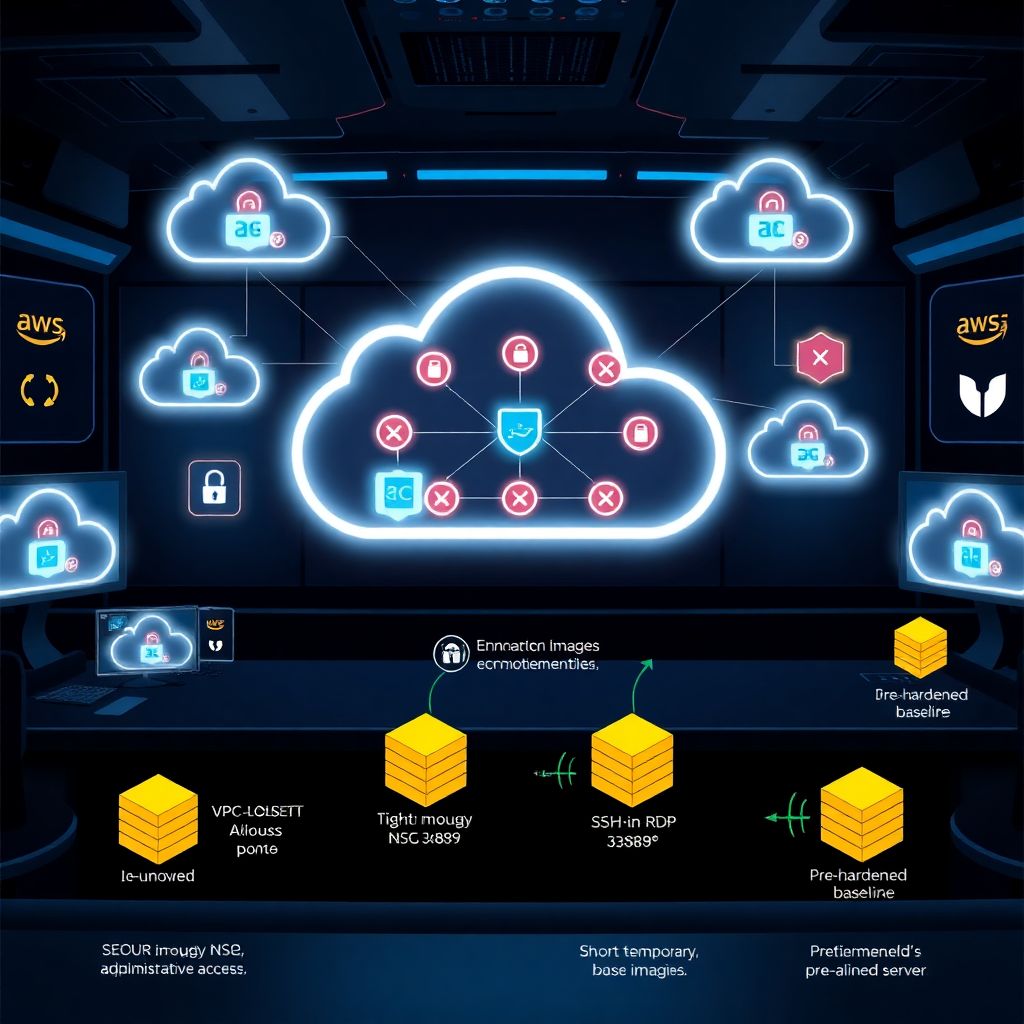
Practical hardening guide for cloud instances on Aws, azure and Gcp
Por que hardening em cloud em 2026 ficou bem mais sério Se em 2020 dava pra “levantar” uma VM na AWS, Azure ou GCP e só depois pensar em segurança, em 2026 isso virou receita pra incidente. Scanners de internet fazem varreduras em minutos, bots testam credenciais vazadas em massa, e ataques aproveitando configurações padrão…