Categoria: Manuais
-
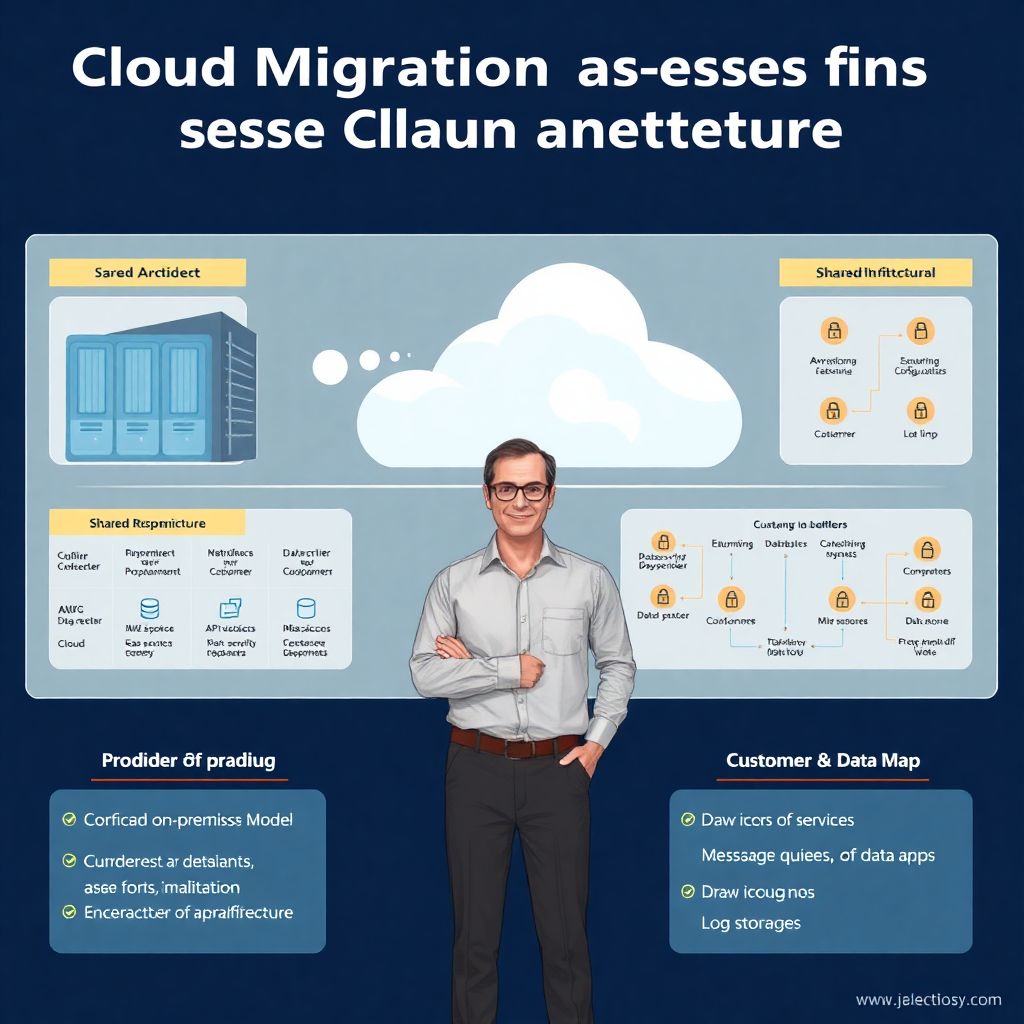
Cloud migration risk assessment: security checklist for It architects
Avaliação de risco em migrações para a nuvem: с чего реально начинать Переезд в облако давно перестал быть модной игрушкой. Для архитектора это уже обыденная работа — но именно на этапах оценки рисков чаще всего всё и ломается. Не потому что технологии сложные, а потому что рисками занимаются «по остаточному принципу»: пару слайдов в презентацию,…
-
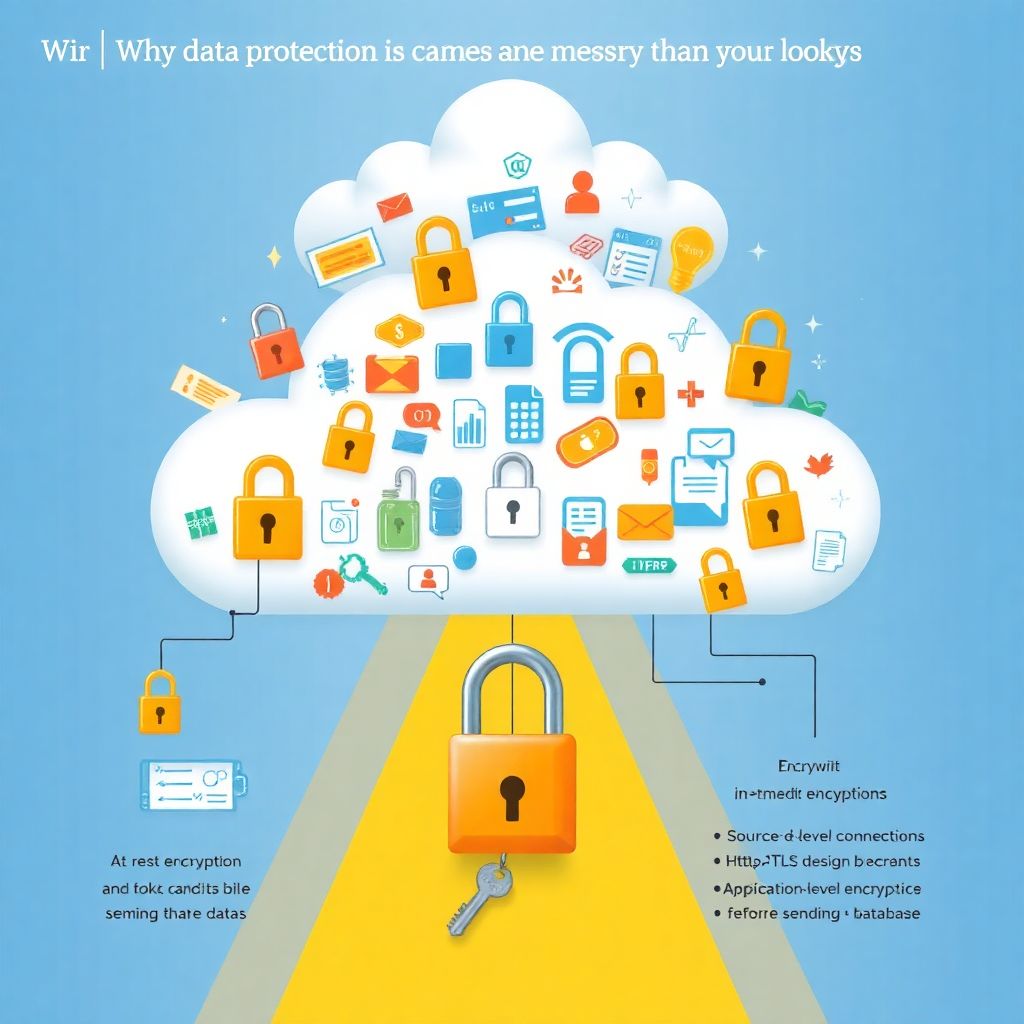
Sensitive data protection in cloud: encryption, tokenization and masking at scale
Why cloud data protection is messier than it looks When you move real business data to the cloud, three questions immediately appear: 1. Who can see it? 2. Who *really* can see it? 3. What happens if it leaks anyway? That last one hurts. Proteção de dados sensíveis na nuvem para empresas não é только…
-
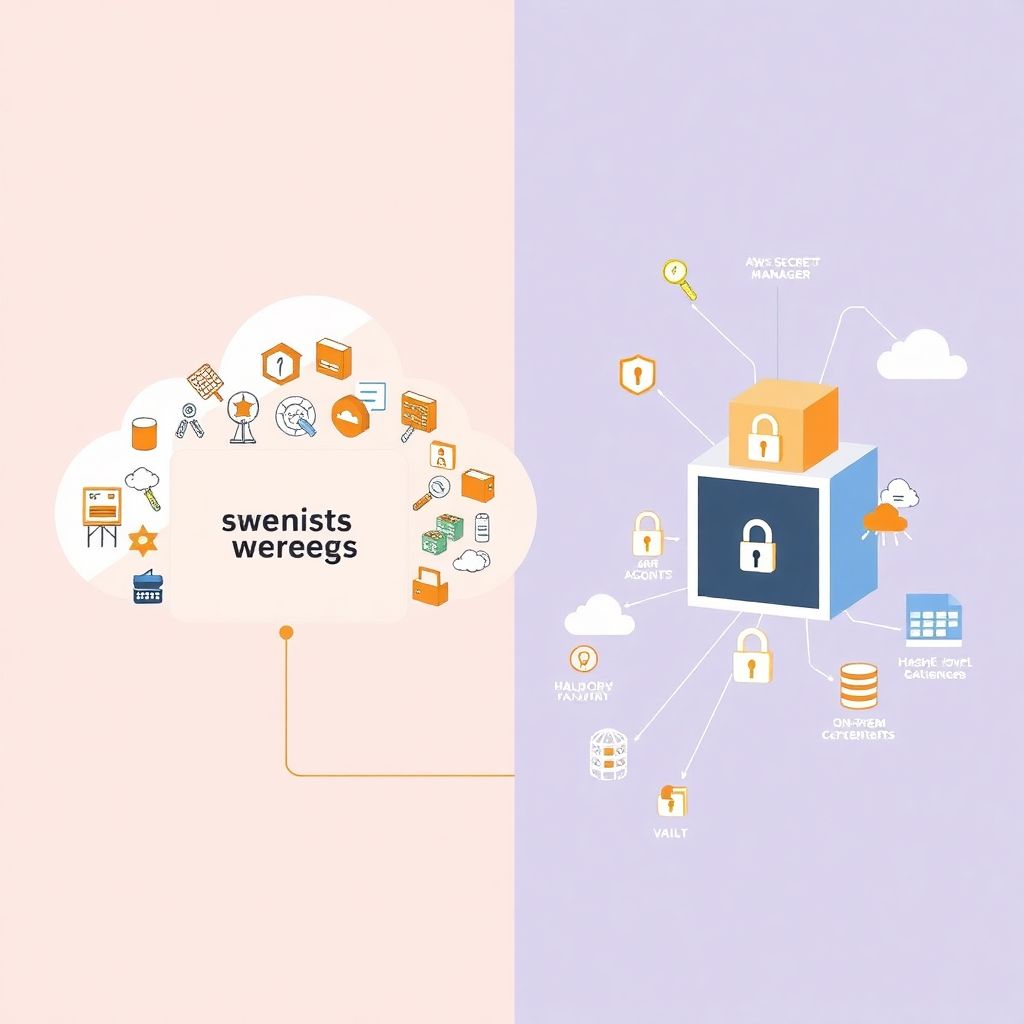
Cloud secrets management best practices with hashicorp vault and Aws secrets manager
Why cloud secret management suddenly became everyone’s problem If you run anything serious in the cloud today, you’re doing gestão de segredos na nuvem whether you like it or not. API keys, database passwords, OAuth tokens, SSH keys, encryption keys – all of that is “secret material” that attackers love, and that compliance teams lose…
-

Policy as code with terraform and open policy agent for secure infrastructure
Why “security as code” isn’t optional anymore Security policies written em PDFs, wikis e apresentações morrem rápido. Infra muda todo dia, times de DevOps automatizam tudo, e o resultado é simples: se a política não vira código, ela vira ruído. Implementar políticas de segurança baseadas em código com Terraform, Policy as Code e Open Policy…
-

Cloud data protection at rest and in transit with Tls, Hsm and end-to-end encryption
Why protecting data at rest and in transit in the cloud really matters When you move workloads to the cloud, you’re effectively putting your information on someone else’s computers and wires, o que torna a segurança de dados na nuvem criptografia em repouso e em trânsito uma prioridade prática, não теórica. Attackers rarely “hack the…
-
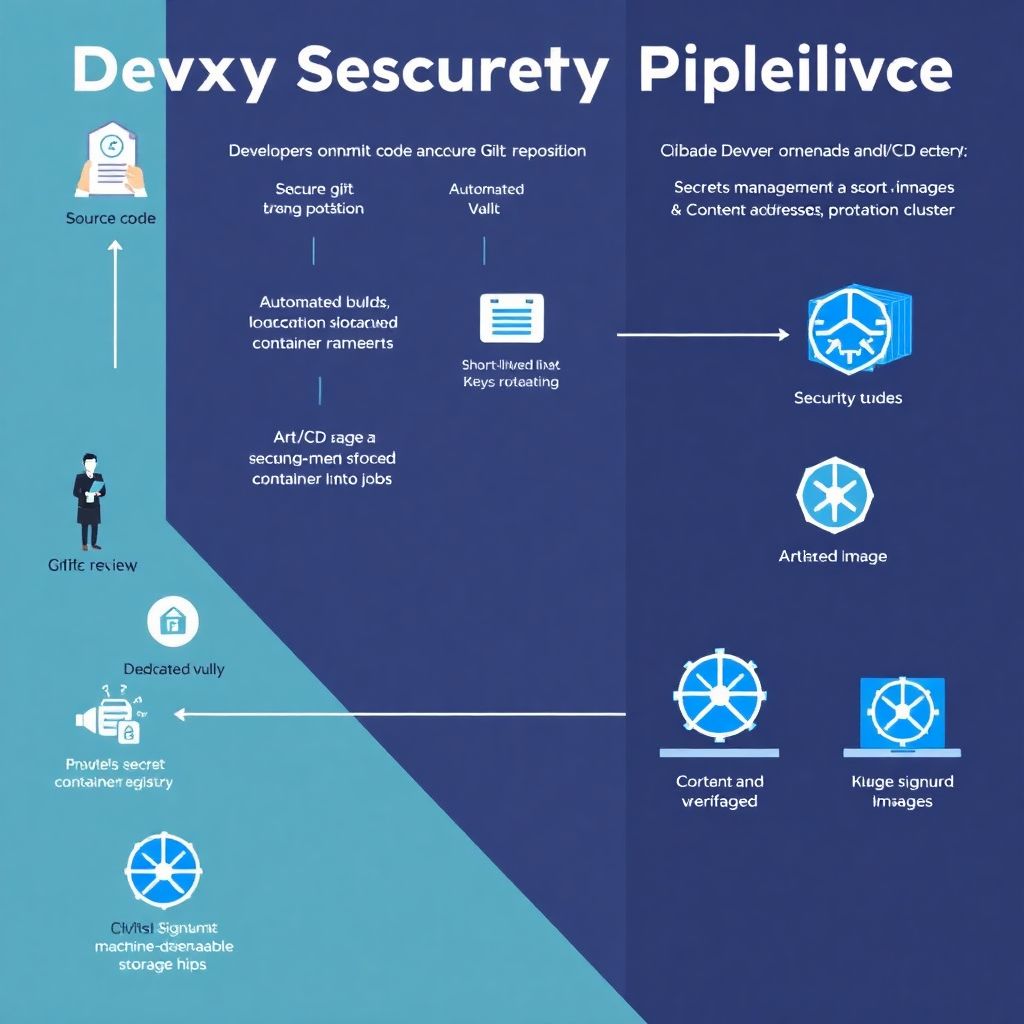
Ci/cd pipeline security: protecting secrets, artifacts and container registries
Why CI/CD security is the lever that changes your entire delivery game When teams talk about CI/CD, they usually focus on speed: more deployments, more automation, more features in production. But if you ignore security, that same pipeline becomes a perfectly oiled weapon — only pointed at your own infrastructure. Segurança em pipelines CI/CD isn’t…
-
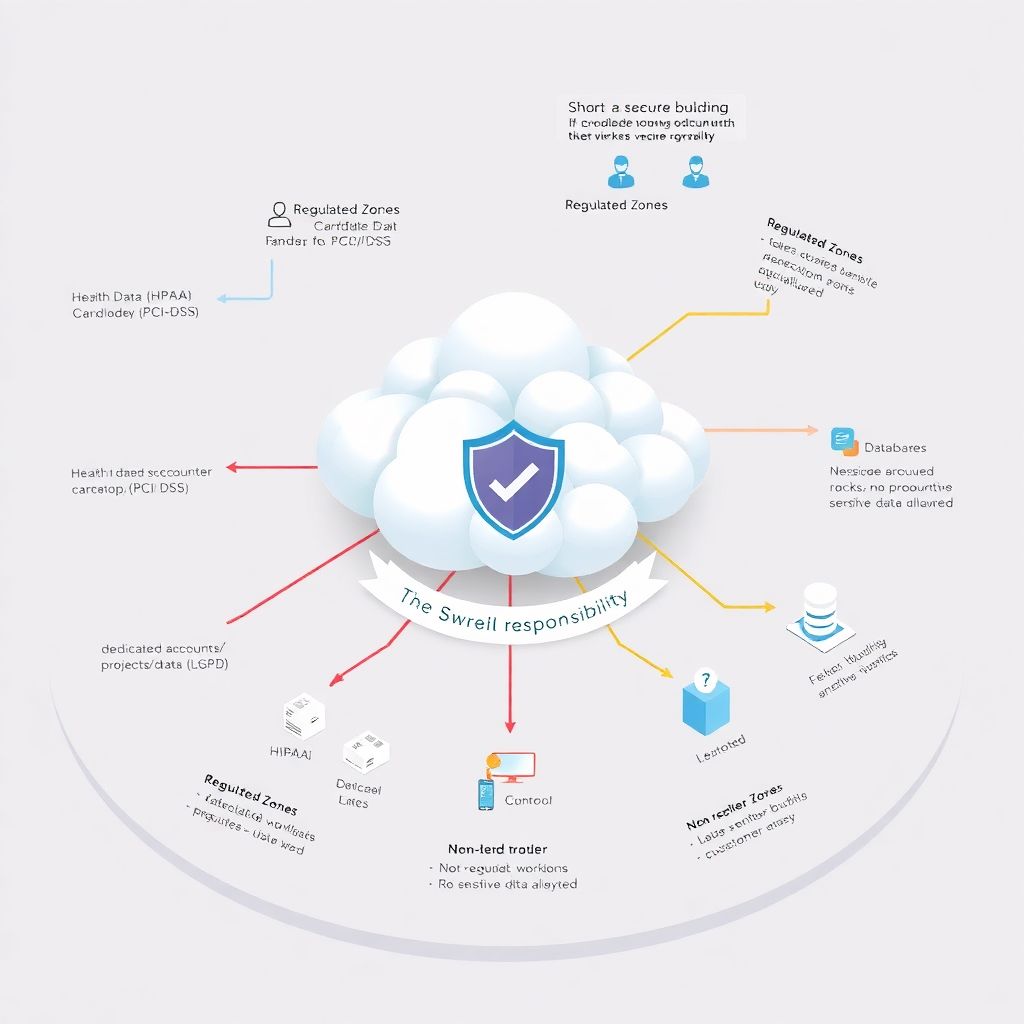
Cloud security compliance checklist for regulated companies under Lgpd, Hipaa, Pci-dss
Why a cloud security compliance checklist matters for regulated companies If your company touches health data, payment cards or personal data from Brazil, you can’t treat the cloud as “someone else’s computer and problem”. Regulators expect you to prove control, not just buy technology. A clear checklist de conformidade para cloud security em empresas reguladas…
-

Devops and security splits: introducing devsecops without slowing delivery pipeline
Frictions between DevOps and Security: why the gap still exists in 2026 Even in 2026, many organizations still treat DevOps and security as parallel universes. Product teams otimize lead time, deployment frequency and mean time to recovery, enquanto times de segurança mantêm foco em controles, auditoria e conformidade. Globalmente, diversas pesquisas indicam que mais de…
-

Cloud threat monitoring and detection: Siem vs Xdr vs native security tools
Why cloud threat monitoring in 2026 is a career-making choice Cloud isn’t “someone else’s computer” anymore; for большинство компаний это их основной офис, дата‑центр и лаборатория сразу. Когда приложение разворачивается за минуты, а данные летают между регионами и сервисами, мониторamento e detecção de ameaças em cloud перестают быть опцией и становятся вопросом выживания бизнеса. Те,…
-

Cloud provider security posture: checklist for buying and audit decisions
Por que vale a pena desconfiar antes de confiar Quando alguém pergunta se um provedor cloud é “seguro”, обычно espera ouvir o nome de um grande player e успокоиться. На практике всё сложнее: безопасность в облаке — это не бренд, а совокупность процессов, архитектурных решений и вашей собственной зрелости. Ошибка многих компаний — смотреть только…