Categoria: Revisões de Ferramentas
-

Complete cloud account hardening guide for Aws, azure and google cloud
Why cloud account hardening matters right now Over the last three years, cloud breaches linked to basic account misconfigurations have stayed stubbornly high. According to IBM’s Cost of a Data Breach reports, around 82–85% of investigated breaches between 2022 and 2024 involved data stored in cloud environments, and misconfig or stolen credentials remained among the…
-

Ai in cloud security: news, trends and its impact on defense and attack
Why AI is quietly reshaping cloud security and cloud attacks If you manage anything serious in the cloud, you’re already feeling that the game changed: more APIs, more identities, more misconfigurations, and now attackers using AI to chain tiny mistakes into big breaches. The interesting part is that both red and blue teams are plugging…
-
Incident response automation in cloud using Soar and serverless functions
Context and mindset for cloud incident response automation Why SOAR and serverless fit cloud-native security When you move most workloads to public cloud, incident response by hand simply cannot keep up with the volume and speed of events. That is where automação de resposta a incidentes em cloud becomes essential: you want playbooks that react…
-

How to assess serverless attack surface in Aws lambda and cloud functions
Avaliar a superfície de ataque em ambientes serverless parece simples à primeira vista: “não tenho servidor, então tenho menos coisa para proteger”. Na prática é quase o contrário. Você terceiriza parte da responsabilidade para o provedor de nuvem, mas ganha uma nova camada de riscos específicos de funções, eventos e integrações. Vamos destrinchar isso com…
-
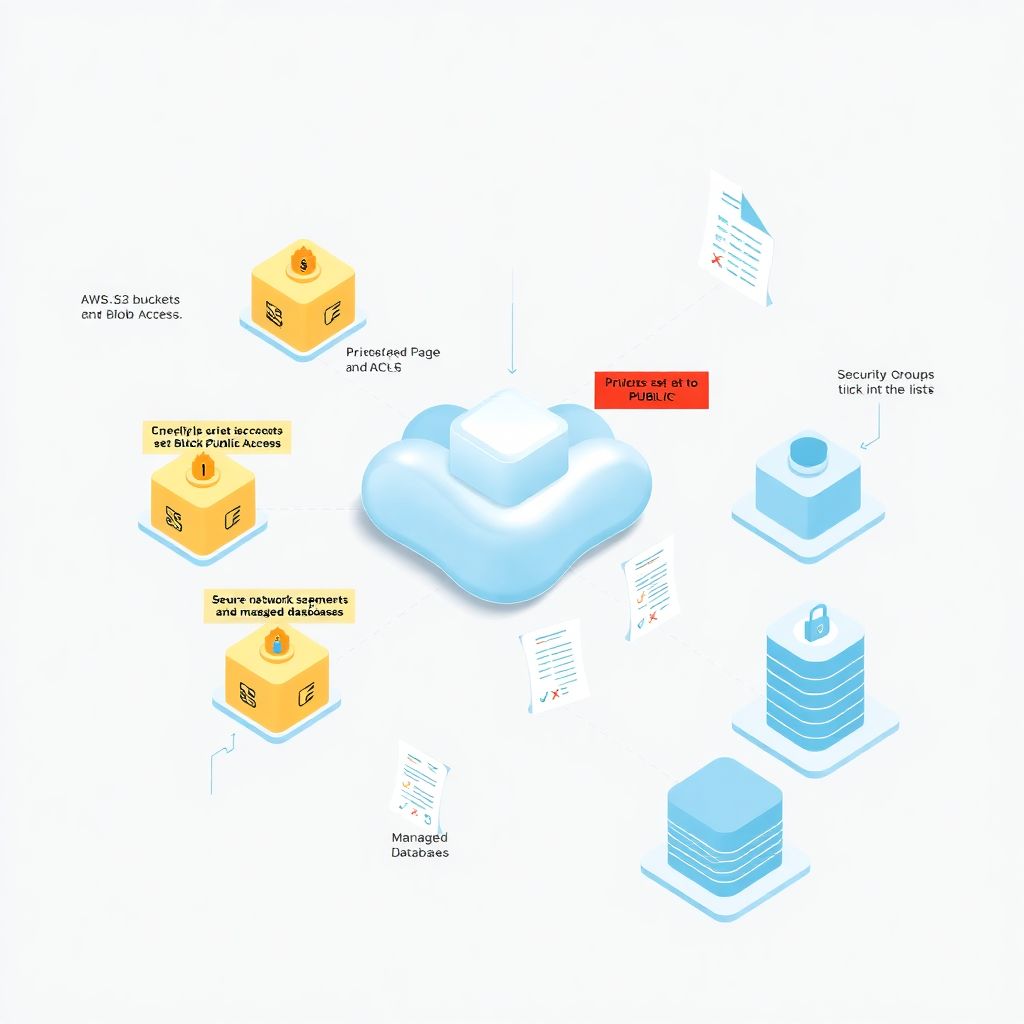
Common configuration errors in managed services S3, blob storage, Rds and how to avoid them
Historical background of managed services misconfigurations When cloud providers launched early managed storage like S3 and later Azure Blob, the main promise was to hide infrastructure complexity behind simple APIs. That convenience came with a subtle trap: security and governance knobs also moved into the console, where a single checkbox could expose terabytes of data….
-

Cloud compliance with Lgpd, Gdpr and Iso 27001: practical changes for It teams
Why cloud compliance suddenly became everyone’s problem in IT If you work with infrastructure, security or devops, you’ve probably noticed something in the last few years: talking about LGPD, GDPR and ISO 27001 in cloud environments stopped being a “legal thing” and turned into a very practical, very technical day‑to‑day concern. Since around 2022 the…
-

Cloud container and kubernetes security: from basic setup to critical production
Segurança em containers e Kubernetes: contexto real Por que isso virou assunto de sobrevivência When you move from pets (VMs) to cattle (containers), your attack surface explodes sideways. Studies from multiple cloud providers show that over 60–70% of successful cloud breaches in the last years envolveram algum tipo de erro em configuração de identidade, rede…
-
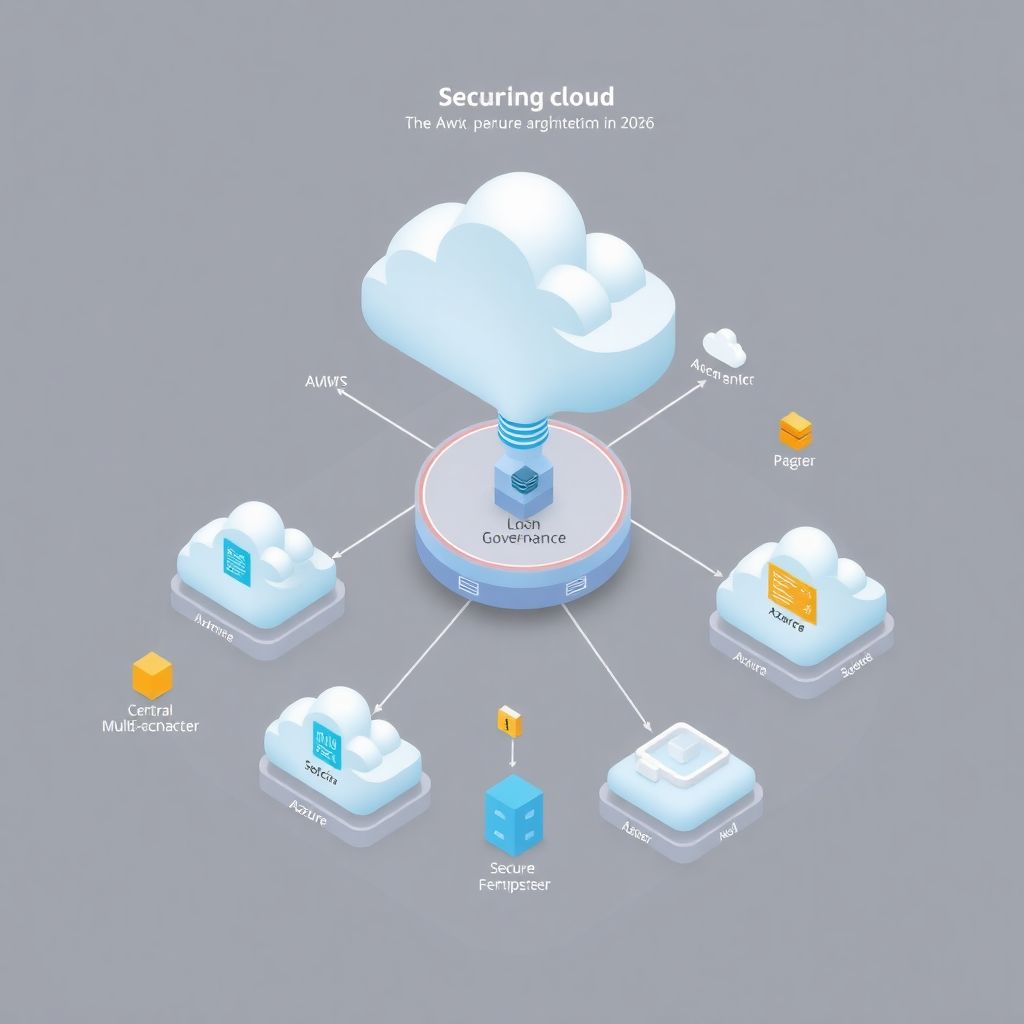
Secure multi-cloud architecture: patterns, pitfalls and best practices for 2026
Why “secure multi‑cloud” suddenly matters so much Multi‑cloud isn’t exactly new. Back in the early 2010s, most teams were wrestling with one big question: “AWS or not AWS?” Then Azure and GCP matured, SaaS exploded, and regulators started asking uncomfortable questions about resilience and data residency. Around 2018–2020, many enterprises “slid” into multi‑cloud almost by…
-
Implementing microsegmentation and east-west traffic control in cloud sddcs
Por que microsegmentação e tráfego leste-oeste viraram prioridade em 2026 Se você ainda pensa em segurança só como firewall de borda, está basicamente jogando em 2010. Em 2026, o grosso dos ataques bem-sucedidos em nuvem acontece dentro do data center, no tráfego leste-oeste entre workloads. Ransomware moderno não tenta só entrar: ele se move lateralmente,…
-
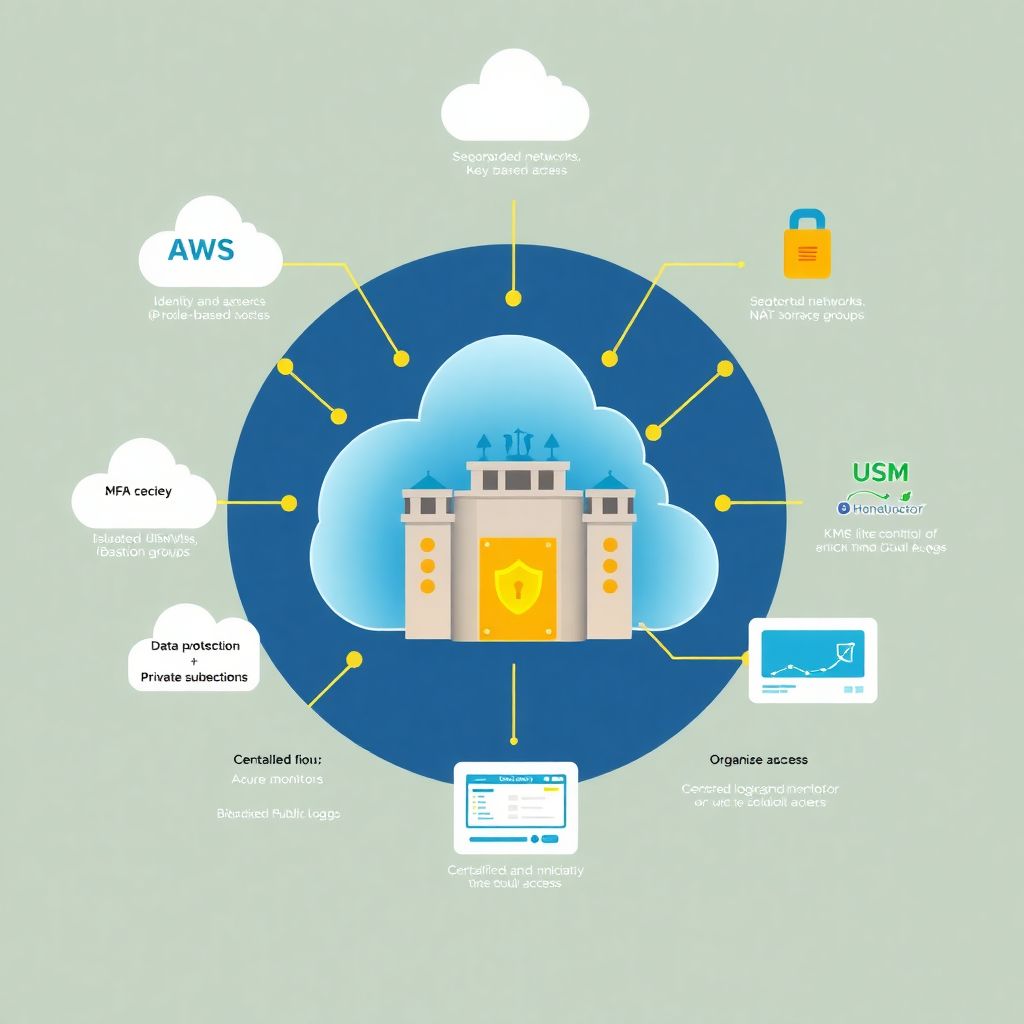
Secure configuration guide for Aws, azure and Gcp: essential security checklist
Cloud security stopped being “nice to have” a long time ago. Between 2021 and 2023, reports from Verizon, IBM e CrowdStrike mostram um crescimento consistente de incidentes ligados a configurações erradas em nuvem, responsável por 45–60% das violações analisadas, dependendo do estudo e do ano. A boa notícia: quase tudo isso é evitável com um…