Categoria: Artigos
-

How to structure an incident response runbook for hybrid cloud environments
A hybrid-cloud incident response runbook is a structured, step-by-step guide that defines who does what, when, and with which tools during an incident across on‑prem and multiple clouds. To build it, you must map assets, roles, incident classes, severity levels, and environment‑specific playbooks, then test, automate, and continuously refine. Essential Elements for a Hybrid-Cloud Incident…
-
Zero trust in the cloud: key principles, reference architecture and common pitfalls
Zero Trust na nuvem means assuming no implicit trust inside or outside your cloud, verifying every identity, device and workload on each request. Start by mapping identities and data, enforcing least privilege with strong IAM, segmenting networks, adding continuous monitoring and automating responses to risky behavior to reach sustainable Zero Trust security. Core principles to…
-

Assessing external attack surface of cloud applications with Asm tools
To safely assess the external attack surface of your cloud applications, deploy an external attack surface management (ASM) solution, map all internet‑facing assets, validate findings with non‑destructive tests, and integrate results into CI/CD and incident response. Focus on exploitable issues on critical assets and maintain continuous monitoring instead of one‑off scans. Assessment highlights for external…
-

Network segmentation and microsegmentation best practices in cloud-native environments
Cloud-native network segmentation and microsegmentation mean isolating workloads using identity, labels and policies instead of only IP-based firewalls. In Brazilian environments running Kubernetes and managed cloud computing services, good practice is to combine cluster NetworkPolicies, service mesh or host firewalls, plus automation and monitoring, always balancing security depth with team skills and available resources. Core…
-

Cloud key, secret and certificate management: comparing major providers vaults
For most Brazilian companies already standardized on one provider, the best budget-first choice is the native stack: AWS KMS + Secrets Manager, Azure Key Vault, or Google Secret Manager with Cloud KMS. Multi-cloud or on-prem integration usually justifies HashiCorp Vault. Start simple, centralize secrets, and upgrade only when compliance or scale really demand it. Budget-first…
-

Cloud security checklists for Aws, azure and Gcp before going to production
Use a repeatable, provider-specific security checklist before production to block the most common cloud incidents: leaked keys, overexposed networks, missing encryption and no logging. This guide gives safe, concrete checks for AWS, Azure and GCP, aligned with Brazilian teams (pt_BR), and can be used both internally and with external cloud security consultants. Pre-production security snapshot…
-

Cloud vulnerability analysis with managed scanners and seamless Ci/cd integration
Cloud vulnerability analysis in Brazilian environments means mapping your cloud assets, choosing safe scanners, running automated checks, and integrating results into CI/CD and ticketing. For intermediate teams, combine open‑source tools with a scanner de vulnerabilidades em nuvem gerenciado to scale, reduce blind spots, and keep developers in the loop. Executive summary of conclusions Start with…
-

Sensitive data protection in cloud: Dlp, masking, tokenization, environment isolation
Protecting sensitive data in cloud workloads combines clear data classification, soluções DLP em cloud para empresas, masking, tokenization, strong encryption, and segregação de ambientes em cloud para dados sensíveis. For pt_BR organizations aiming at ferramentas de segurança em nuvem для compliance LGPD, the focus is to minimize exposed data, reduce blast radius, and continuously verify…
-

How to structure a cloud security governance and compliance program for regulated firms
To structure a cloud security governance and compliance program for regulated companies in Brazil, start by mapping regulations to cloud services, defining risk ownership, and building a minimum control baseline. Then operationalize with clear workflows, evidence requirements, monitoring, and audit‑ready reporting tailored to your regulators, business units, and outsourced cloud providers. Governance and compliance blueprint…
-
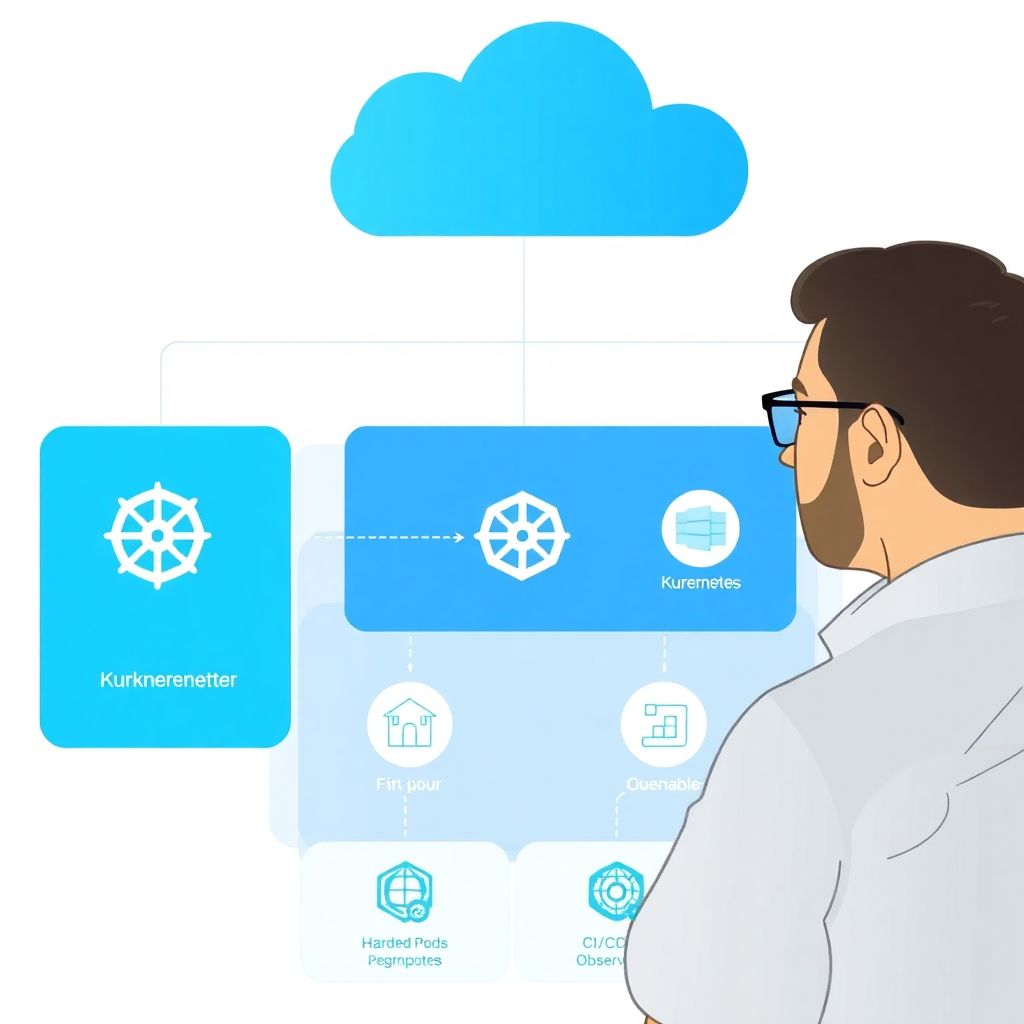
Secure kubernetes cloud workloads: complete configuration guide
To configure secure workloads in Kubernetes on cloud providers, start with a clear threat model, lock down the control plane, enforce network segmentation, and apply pod-level hardening. Then secure identities and CI/CD, add image signing, and implement strong observability and incident response. This guia de hardening de kubernetes em cloud focuses on practical, cloud-neutral steps….