Categoria: Artigos
-
Zero trust in the cloud: how to implement a minimal trust model in multicloud
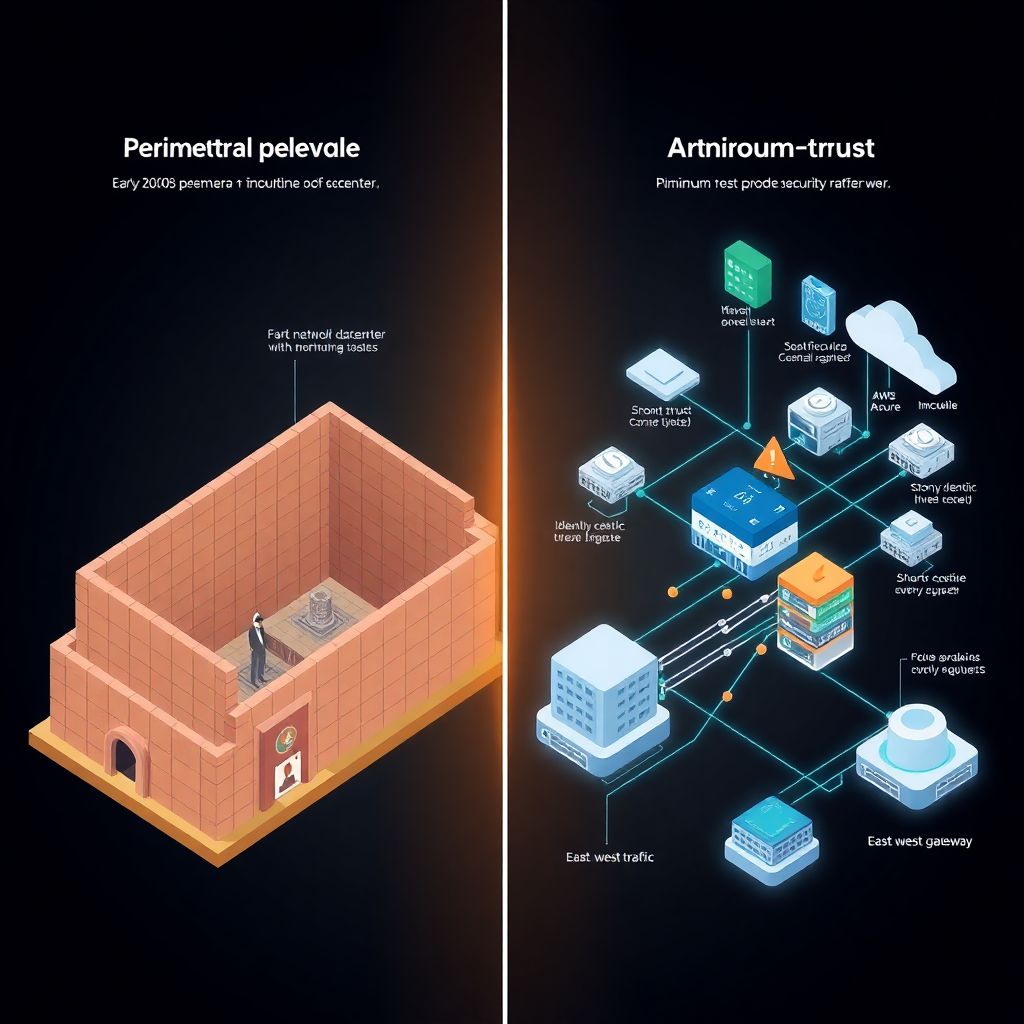
From perimeter firewalls to zero trust na nuvem Back in the 2000s, most companies trusted anything inside the corporate LAN and distrusted only the “outside”. VPNs, firewalls and IDS formed a hard edge, while workloads stayed concentraded in one datacenter. Around 2015, as AWS, Azure and GCP gained mass adoption, attackers began targeting identity, APIs…
-
Zero-day in managed cloud services: how to monitor, respond and inform business
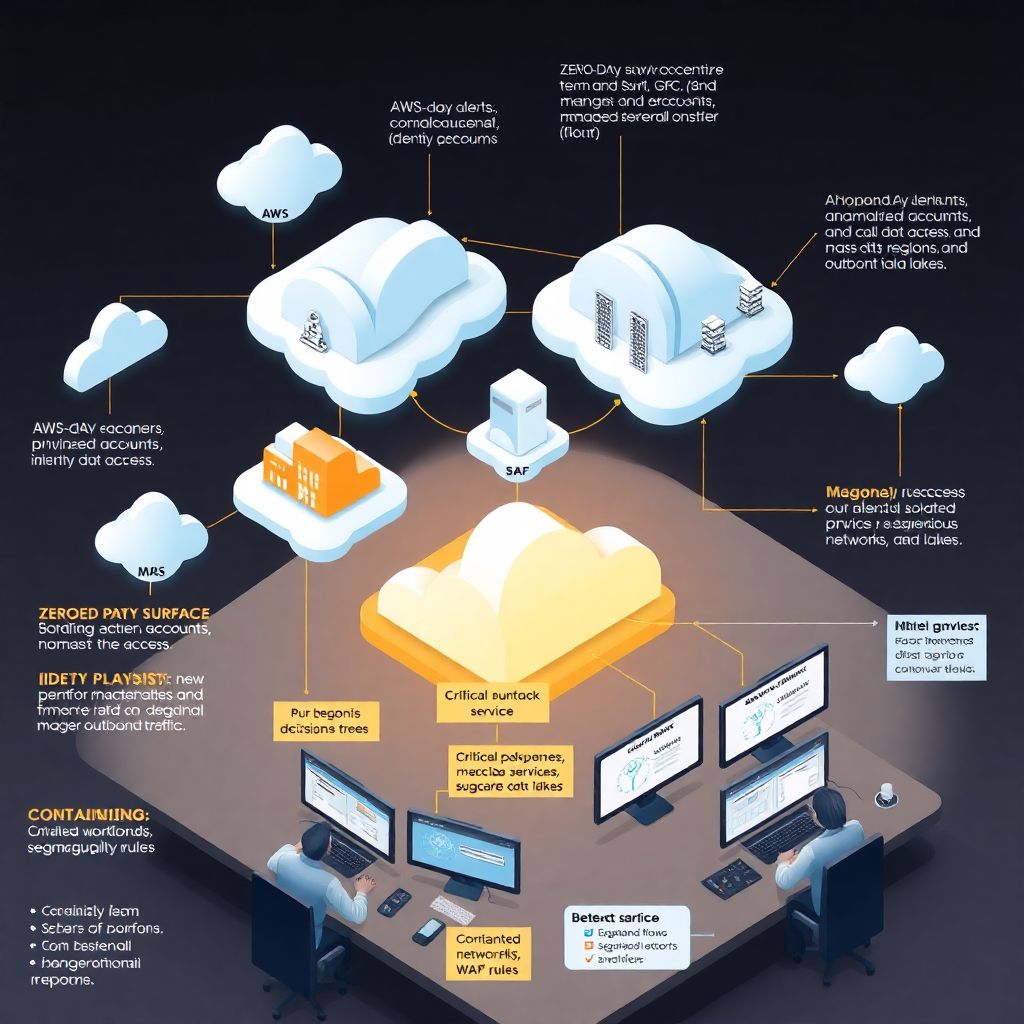
Why zero-days in managed cloud are a different beast Zero-day flaws are scary anywhere, but in managed cloud services they hit differently. You’re not just dealing with your own stack; you also depend on your provider, your MSSP, and often several third‑party platforms. When a zero-day pops up, you need to know very quickly: are…
-

Managed Waf comparison: reviewing tools from leading cloud providers
Why managed WAFs matter in 2026 In 2026, most web attacks never even reach your app; they die at the edge, inside a managed WAF. Cloud providers turned WAF into a kind of “security CDN layer”: always‑on, globally distributed and deeply integrated with identity, APIs and observability. Instead of managing rule engines and patches, teams…
-
News: recent cloud service vulnerabilities and their impact on companies
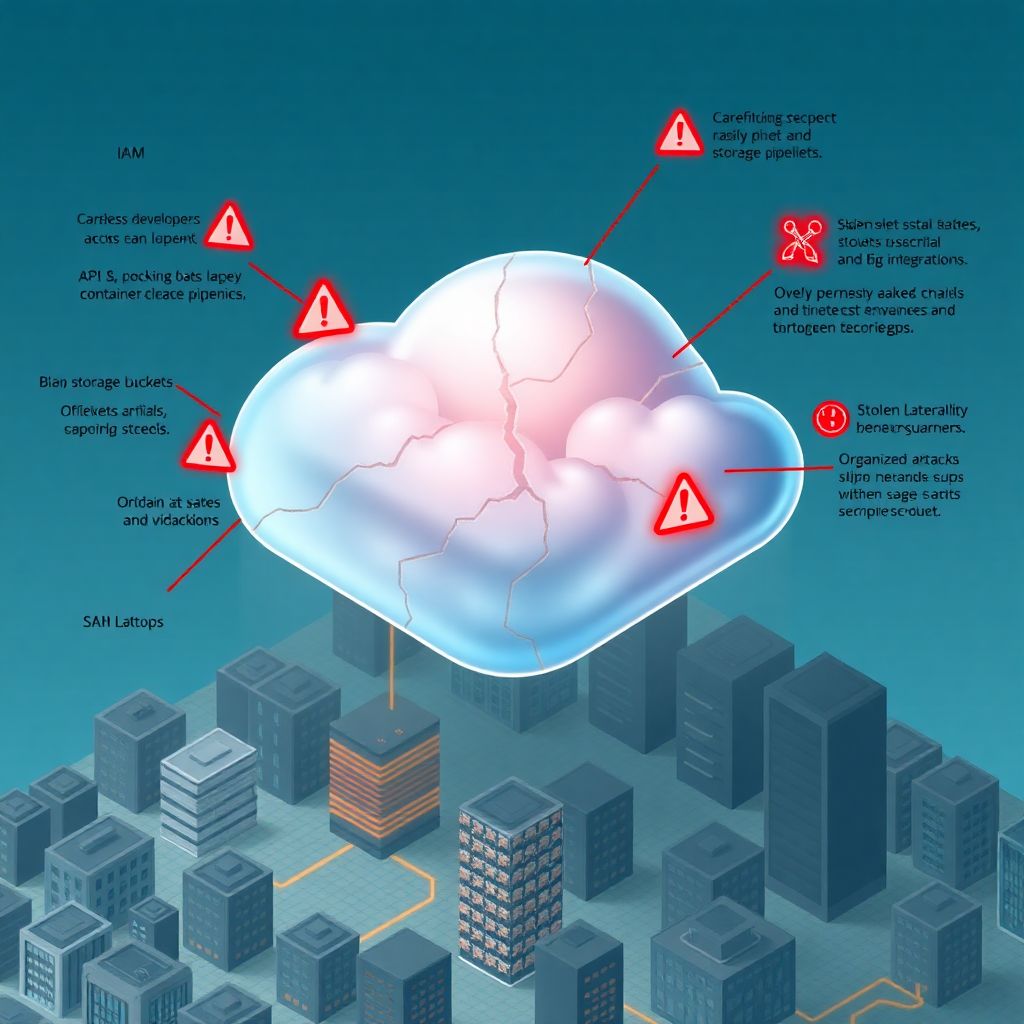
Why cloud vulnerabilities are back in the news (and why you should care) Over the last few years, cloud has gone from “nice to have” to “if it goes down, our business stops.” That shift made every misconfiguration, weak password and sloppy API suddenly front‑page material. When you read headlines about huge data leaks, ransomware…
-

Secure cloud landing zone guide for large organizations
Por que uma landing zone em cloud para grandes empresas virou assunto de sobrevivência Vamos ser diretos: para grandes organizações, hoje não é mais “se” vão para a nuvem, mas “como” vão fazer isso sem quebrar segurança, compliance e orçamento. Alguns números rápidos para alinhar contexto: – Segundo o Gartner (2023), mais de 65% das…
-
Kubernetes security: from basic cluster setup to resilient production environments
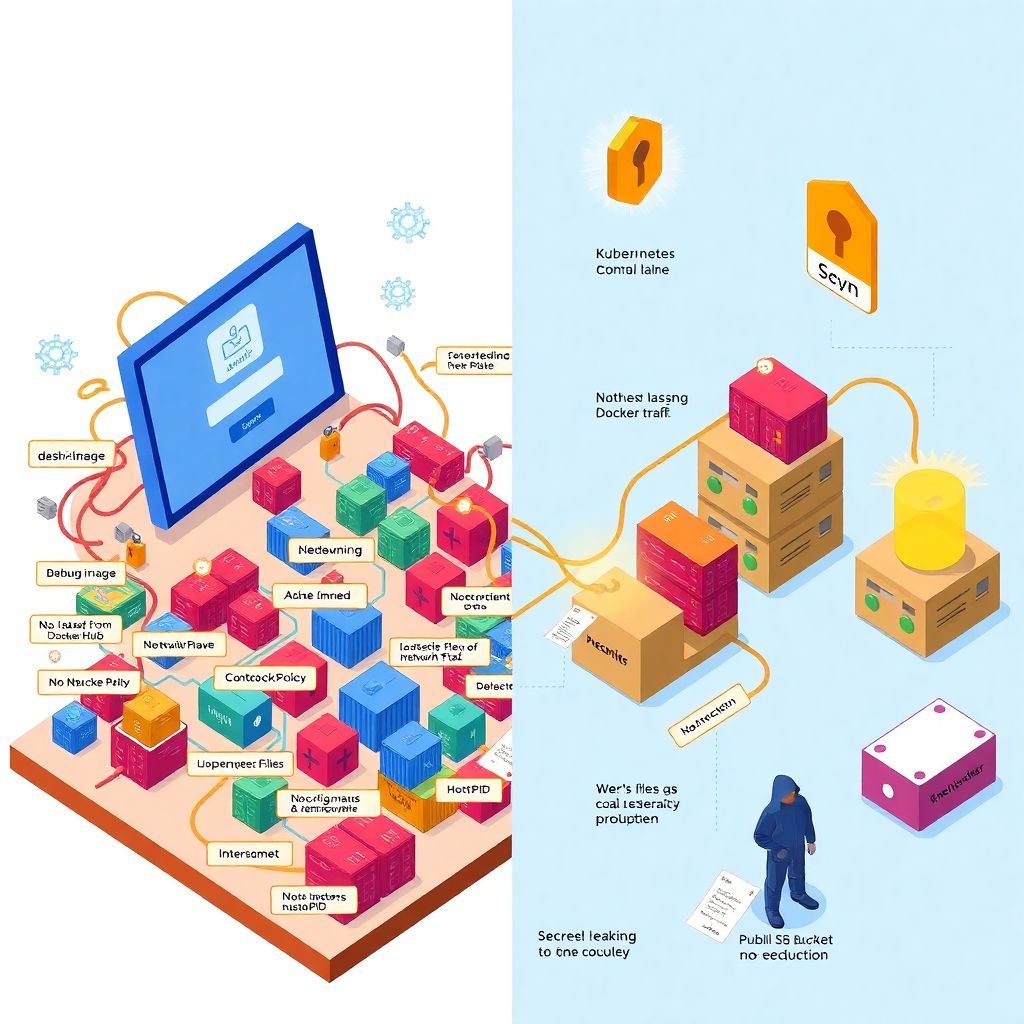
Por que segurança em Kubernetes parece сложнее, чем есть на самом деле Когда люди впервые заходят в мир Kubernetes, им быстро показывают деплойменты, сервисы и магию автоскейлинга. А вот безопасность обычно подвешивают «на потом», как будто это можно прикрутить одной галочкой в конце. Отсюда и вырастают классические истории: кластер с правами admin:admin, открытый в интернет,…
-

Best Cnapp tools compared: practical guide to protecting cloud workloads
Por que o CNAPP virou peça-chave da segurança em nuvem Do patch manual ao “piloto automático” de segurança Se você lembra como era proteger infraestrutura de nuvem em 2018–2020, dá quase nostalgia: scripts espalhados, dezenas de dashboards, alertas que ninguém lia e auditorias que pareciam um susto permanente. Em 2026, o jogo mudou. As empresas…
-

Cloud security posture management: how to build a Cspm program from scratch
Why CSPM became a must‑have (and not a “nice‑to‑have”) Back in 2015, “cloud security” in most companies meant: security groups, a few IAM roles, maybe some encryption, and a shared Excel with “best practices”. Fast‑forward to 2026, and we live in a world where one misconfigured S3 bucket or overly permissive Azure Storage account can…
-
Pentest and bug bounty best practices for secure cloud infrastructure
Por que pentest e bug bounty em cloud são diferentes do resto Quando você sai do mundo on-premise e entra em infraestruturas cloud, o “jogo” do pentest muda bastante. Você não está mais só procurando uma porta 22 aberta; agora precisa entender identidades, policies, serviços gerenciados e integrações entre contas. Boas práticas aqui não são…
-

Cloud security incident analysis: lessons from major real-world data breaches
Why real cloud breaches teach more than glossy vendor brochures When people talk about cloud security, the conversation often stays at the level of principles and best practices. In reality, most teams start changing behavior only after a painful incident — theirs or someone else’s. Looking closely at big data leaks in the cloud gives…