Categoria: Guias
-

Threat modeling for cloud native applications: key strategies and tools
Threat modeling for cloud-native applications is a repeatable process to map your architecture, identify critical assets, think like realistic attackers, and prioritize risks with concrete controls. For Brazilian teams building on Kubernetes and managed cloud services, start small, automate where possible, and integrate with CI/CD instead of running one-off, heavyweight workshops only. Operational summary checklist…
-

Open source cloud security tools review: scanners, iac, Sast, Dast
For most Brazilian teams, the fastest way to implement cloud security with open source is to combine: Semgrep or SonarQube Community for SAST, OWASP ZAP for DAST, Checkov or tfsec for IaC, and Trivy for containers. Integrate them in CI/CD first, then expand with policy-as-code and runtime checks. At-a-glance security snapshot Start by mapping your…
-

Cloud cybersecurity trends for coming years with Ai, automation and emerging threats
Cloud cybersecurity in the next years will be shaped by AI‑driven attacks, large‑scale automation and fast‑evolving threat models around data, identity and software supply chain. For segurança em nuvem para empresas in Brazil, practitioners must combine AI‑assisted defense, zero‑trust‑by‑default and secure automation pipelines instead of isolated tools or manual processes. Core trends shaping cloud security…
-

How to conduct a cloud-native workloads vulnerability assessment in the cloud
A focused vulnerability assessment for cloud-native workloads means mapping every container, serverless function, and cluster component, then running automated scans plus targeted configuration reviews in a controlled way. In a pt_BR context, prioritize Kubernetes, CI/CD and cloud IAM, produce clear risk scores, and track remediation through tickets with verification checks. Prep item What is needed…
-

Future cloud security trends: Ai, Sase and confidential computing
Future cloud security will be shaped by AI-driven analytics, SASE-based access, confidential computing, and stricter data governance. For Brazilian teams, the priority is combining serviços de inteligência artificial para segurança em cloud with zero-trust design, multi-cloud visibility, and automation aligned with LGPD, while planning early for confidential computing provedores e plataformas. Executive summary: emerging vectors…
-
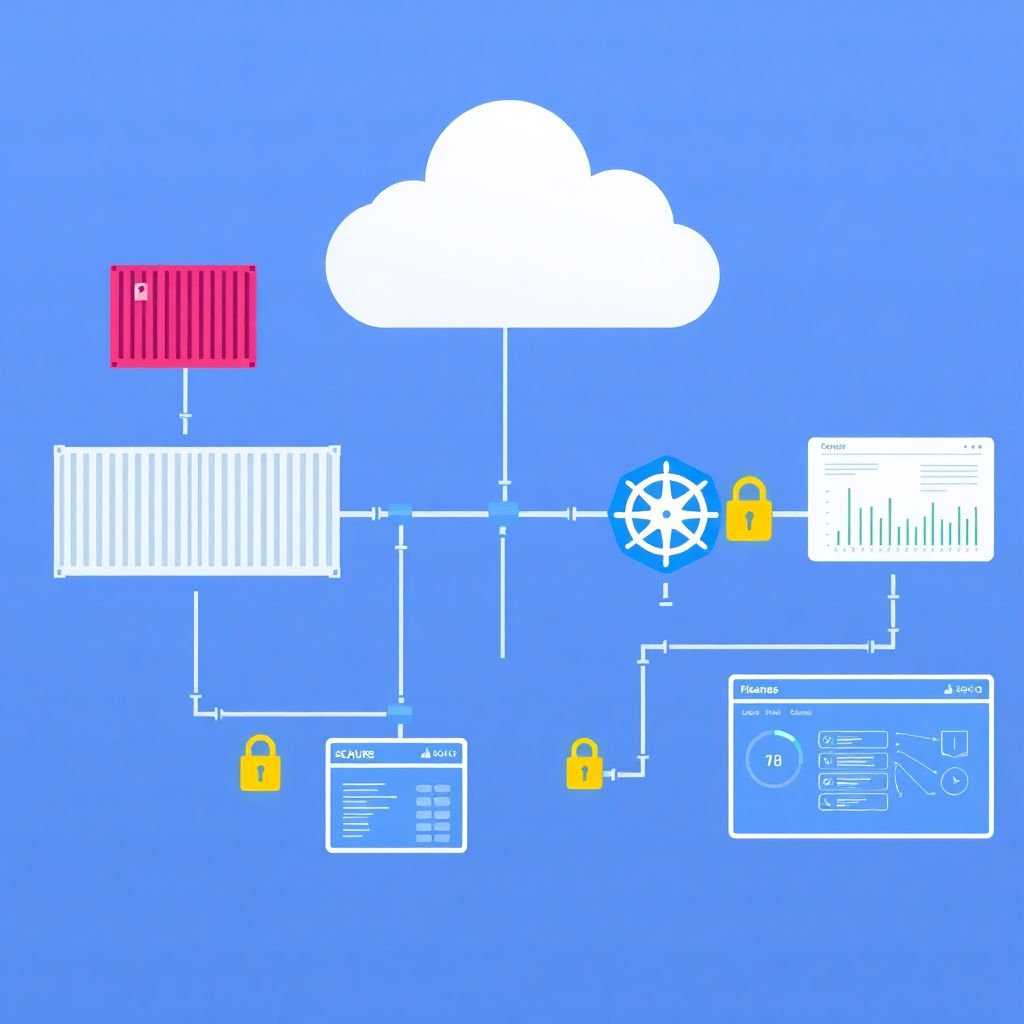
Cloud container security: from image registry to production orchestration
Cloud container security is about controlling risk from image creation to production orchestration: verify image provenance, scan and harden during build, lock down registries, protect CI/CD secrets, enforce policies at runtime, and monitor continuously. This step‑by‑step guide focuses on practical controls that fit typical pt_BR cloud environments and managed Kubernetes services. Security milestones across the…
-

Serverless risks and threats: main attack vectors and how to mitigate them
Serverless environments concentrate risk around function entry points, identities, and external dependencies. To reduce exposure, you must minimize permissions, validate and sanitize all inputs, lock down storage and logs, and continuously monitor function behavior. This guide explains principais vetores de ataque and gives concrete, safe steps to harden your workloads in Brazilian cloud contexts. Critical…
-

Open source tools for cloud vulnerability detection: a technical review
To choose an open-source cloud vulnerability scanner, combine IaC scanning (e.g., Checkov, tfsec), container and image scanning (e.g., Trivy, Grype), cloud configuration auditing (e.g., Prowler, ScoutSuite) and, where needed, runtime agents. Start from your main risks and cloud providers, then evaluate accuracy, integrations and maintenance before standardising on a small tool set. Executive summary for…
-

Zero trust security architectures for corporate multicloud environments
Zero Trust in corporate multicloud means authenticating and authorizing every identity, device, and workload on each request, using least privilege and continuous verification. You will standardize policies across providers, centralize identity, segment networks, encrypt data, and automate controls, while ensuring safe, reversible steps and clear rollback for each change. Essential Pre-Deployment Checklist for Multicloud Zero…
-

Real cloud security failure cases and key lessons learned for It teams
Real-world cloud security failures usually start with small misconfigurations or missed alerts and escalate quickly into data exposure, account takeover, or ransomware. For Brazilian IT teams, the priority is to use read-only checks first, reconstruct the incident timeline, contain access with minimal disruption, then implement architecture-level controls so the same pattern cannot repeat. Critical lessons…