Categoria: Notícias
-

Assessing cloud provider security posture before migrating critical workloads
To evaluate a cloud provider’s security posture before migrating critical workloads, map your business and regulatory requirements, request evidence (policies, audits, configurations), and run small, controlled tests. Focus on identity, network, and data protections, plus incident response maturity, so you can compare providers consistently and reject weak or opaque controls. Posture assessment summary Start from…
-
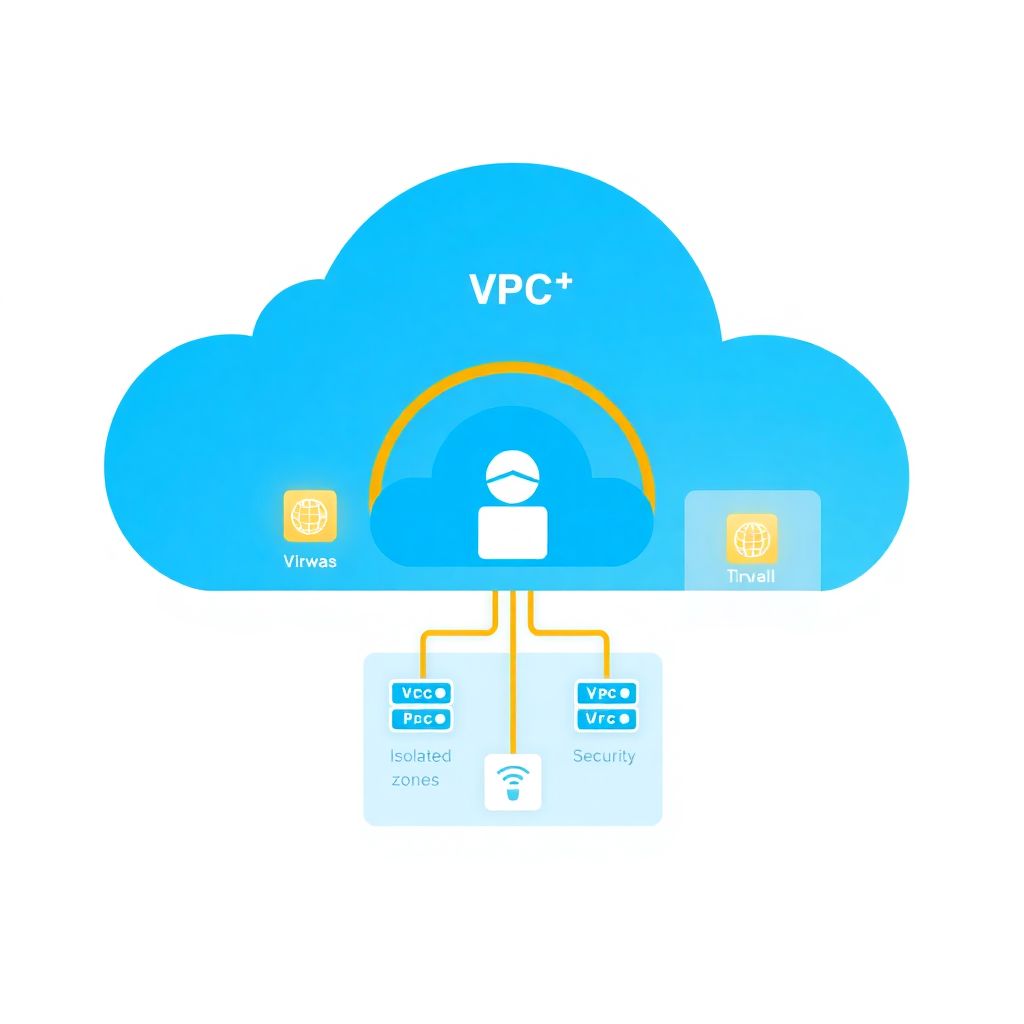
Network segmentation and microsegmentation in vpcs and vnets: implementation guide
Effective VPC/VNet segmentation means splitting your cloud network into clearly scoped zones (prod/non‑prod, tiers, shared services) with least‑privilege traffic between them. You combine subnets, route tables, firewalls, security groups and microsegmentation policies to reduce blast radius. Start simple, automate everything, and tighten rules iteratively with good logging. Pillars of effective VPC/VNet segmentation Design VPC/VNet boundaries…
-

Devsecops in practice: integrating security into Ci/cd pipelines for cloud projects
Implement DevSecOps in a cloud CI/CD pipeline by embedding security gates into each stage: design secure architecture, add shift-left code and dependency checks, scan Infrastructure as Code, manage secrets with least privilege, enforce runtime monitoring, and codify compliance. Use small, reversible changes and safe, auditable commands for every step. Core security goals to embed in…
-

Cloud encryption: how to choose between provider‑managed and self‑managed keys
For most workloads, start with provider-managed keys for low-cost, low-friction encryption, move to your own cloud KMS when you need stronger separation of duties and auditability, and adopt dedicated HSMs only for the small set of systems with strict compliance, high-value keys or cross-cloud, long-term cryptographic control. Cost-first summary: choosing the right cloud encryption model…
-

Cloud compliance guide: mapping Lgpd, Iso 27001, Pci-dss and Soc 2
Cloud compliance in Brazil means mapping LGPD, ISO 27001, PCI-DSS and SOC 2 to concrete cloud controls, contracts and evidence. Focus on data flows, residency, shared responsibility, and provider-native tools. Start small: one critical workload, define scope, assign owners, then iterate with lightweight governance and continuous monitoring. At-a-Glance Compliance Checklist for Cloud Deployments Define scope:…
-

News: cloud cybersecurity trends for next year and their impact on compliance
The main cloud security trends for the next year are expansion of Zero Trust, heavier use of AI and automation, stricter data residency and encryption, and tighter control of cloud supply chains. For Brazil, these trends directly affect how companies maintain LGPD compliance and prove continuous control effectiveness in cloud environments. Executive summary: top cloud…
-

Secure Iam in Aws, azure and Gcp: implementing identity-based access control
To implement secure, identity-based access control across AWS, Azure and GCP, centralize identities, enforce strong authentication, define least‑privilege roles, standardize cross‑cloud mappings, protect secrets with managed services and continuously audit. Start small with core workloads, then iterate policies using logs, access reviews and automated policy checks. Core IAM Principles to Enforce Across AWS, Azure and…
-
Zero trust in cloud: principles, reference architecture and common pitfalls
Zero Trust in cloud environments is a security model where no user, device, workload, or network is trusted by default, even inside your VPC or corporate VPN. Every access request is strongly authenticated, authorized, and continuously evaluated using identity, device posture, context, and risk, with fine-grained policies and segmentation. Executive summary: Zero Trust essentials for…
-

Ransomware protection techniques for cloud-first and hybrid environments
Use layered controls: harden cloud and hybrid architecture, enforce strong identity, encrypt and back up data with immutability, segment networks with Zero Trust, and deploy EDR/XDR plus automation. Combine native cloud controls with specialized software de segurança cloud para ransomware and clear runbooks so teams in Brazil can execute safe, repeatable responses. Operational priorities for…
-

Security automation with iac: terraform, cloudformation, bicep policies and scanners
Security automation with Infrastructure as Code means enforcing policies, validations, and scanners directly in Terraform, CloudFormation, and Bicep workflows. You codify guardrails, run static and runtime checks, and gate CI/CD so insecure changes cannot reach production, while keeping pipelines fast, repeatable, and auditable for regulated and non‑regulated environments. Security automation snapshot Define cloud‑specific and organization‑wide…