Categoria: Notícias
-

Ci/cd pipeline security: protecting the cloud‑native application lifecycle
Secure CI/CD pipelines for cloud-native apps by locking down source control, isolating build agents, scanning and signing container images, enforcing Kubernetes admission policies, and wiring monitoring into every stage. Focus on least privilege, immutable artifacts, strong secrets management, and fast, automated detection and response for any pipeline compromise. Security preflight checklist for CI/CD pipelines Enforce…
-

Cloud access security broker (casb) comparison for medium and large enterprises
For Brazilian medium and large enterprises, the best CASB is the one that matches your identity stack, SaaS portfolio and support capacity, not a single universal vendor. Use a weighted scoring matrix, decide between inline, API or hybrid, compare plataformas CASB preços e funcionalidades and then pilot with real Brazilian traffic. At-a-glance conclusions for security…
-

Cloud security automation with iac: terraform, cloudformation, bicep risks and controls
Infrastructure as Code security in cloud means encoding controls directly in Terraform, AWS CloudFormation and Bicep so every change is reviewed, scanned, approved and monitored. You detect misconfigurations early, enforce least privilege, and remediate by updating code instead of clicking consoles, reducing drift and making automação de segurança em cloud com terraform repeatable. Executive security…
-

Cloud security compliance with Lgpd, Gdpr and global data privacy laws
Aligning cloud security with LGPD, GDPR and other privacy rules means translating legal duties into concrete controls: data mapping, classification, encryption, identity and access management, logging, vendor due‑diligence and incident response. Focus on Brazilian context (LGPD), but design your architecture so that adding GDPR or other regional rules is mostly configuration, not rework. Quick Compliance…
-

Cloud compliance manual: align your environment with Lgpd, Iso 27001 and Pci-dss
To align a cloud environment with LGPD, ISO 27001, PCI-DSS and similar standards in Brazil, you need to map data and services, choose cloud-appropriate controls, configure identity, logging and encryption, and create continuous evidence and monitoring routines. This guide gives a pragmatic, step-by-step manual that is safe, concrete and provider-agnostic. Compliance Snapshot: Core Requirements at…
-

Assessing cloud provider security posture before migrating critical workloads
To evaluate a cloud provider’s security posture before migrating critical workloads, map your business and regulatory requirements, request evidence (policies, audits, configurations), and run small, controlled tests. Focus on identity, network, and data protections, plus incident response maturity, so you can compare providers consistently and reject weak or opaque controls. Posture assessment summary Start from…
-
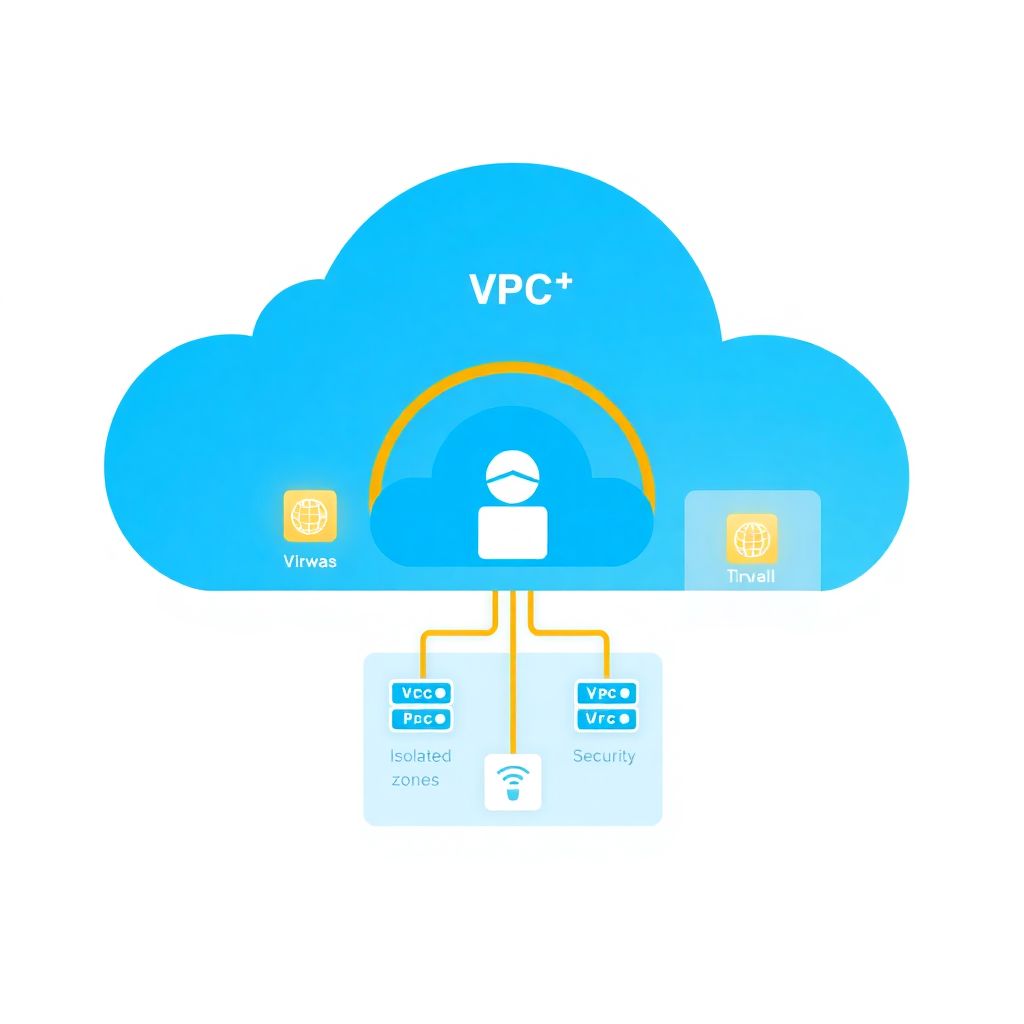
Network segmentation and microsegmentation in vpcs and vnets: implementation guide
Effective VPC/VNet segmentation means splitting your cloud network into clearly scoped zones (prod/non‑prod, tiers, shared services) with least‑privilege traffic between them. You combine subnets, route tables, firewalls, security groups and microsegmentation policies to reduce blast radius. Start simple, automate everything, and tighten rules iteratively with good logging. Pillars of effective VPC/VNet segmentation Design VPC/VNet boundaries…
-

Devsecops in practice: integrating security into Ci/cd pipelines for cloud projects
Implement DevSecOps in a cloud CI/CD pipeline by embedding security gates into each stage: design secure architecture, add shift-left code and dependency checks, scan Infrastructure as Code, manage secrets with least privilege, enforce runtime monitoring, and codify compliance. Use small, reversible changes and safe, auditable commands for every step. Core security goals to embed in…
-

Cloud encryption: how to choose between provider‑managed and self‑managed keys
For most workloads, start with provider-managed keys for low-cost, low-friction encryption, move to your own cloud KMS when you need stronger separation of duties and auditability, and adopt dedicated HSMs only for the small set of systems with strict compliance, high-value keys or cross-cloud, long-term cryptographic control. Cost-first summary: choosing the right cloud encryption model…
-

Cloud compliance guide: mapping Lgpd, Iso 27001, Pci-dss and Soc 2
Cloud compliance in Brazil means mapping LGPD, ISO 27001, PCI-DSS and SOC 2 to concrete cloud controls, contracts and evidence. Focus on data flows, residency, shared responsibility, and provider-native tools. Start small: one critical workload, define scope, assign owners, then iterate with lightweight governance and continuous monitoring. At-a-Glance Compliance Checklist for Cloud Deployments Define scope:…