Categoria: Artigos
-

Ci/cd pipeline security in the cloud: protecting the full delivery lifecycle
Securing CI/CD pipelines in the cloud means controlling identities, secrets, code integrity and deployments across all stages, from commit to production. For teams in pt_BR contexts using AWS, Azure, GCP or Kubernetes, the safest approach is to design least-privilege pipelines, isolate environments, automate checks and continuously monitor every action your pipeline performs. Essential security objectives…
-

Cloud key and secret management with Kms, Hsm and secret vaults implementation
To implement secure cloud key and secret management, combine a managed KMS for most encryption, an HSM for hardware-backed keys, and a managed secret vault for application credentials. Start with a clear key lifecycle, enforce least-privilege access, enable auditing, and test incident-response procedures before moving any production workload. Critical Principles for Cloud Key and Secret…
-

Cspm tools evaluation: choosing cloud security posture management and sample reports
To choose the best Cloud Security Posture Management platform, start from your clouds (AWS, Azure, GCP), required compliance reports, and how deeply you need to integrate with CI/CD and SOC tools. Compare coverage, noise level, report quality and total cost instead of only licenses, using trials and a structured CSPM evaluation checklist. CSPM evaluation -…
-

Protecting privileged cloud accounts with Mfa, rotation and just-in-time audited access
Protecting privileged accounts in cloud providers means combining strong identity hygiene, multi‑factor authentication (MFA), automated credential rotation, just‑in‑time (JIT) elevation and detailed auditing. The goal is to reduce the blast radius of compromise while keeping administrators productive. Each control has different deployment effort and residual risk, so you must balance them deliberately. Essential controls for…
-

Cloud encryption at rest and in transit: provider-managed vs customer keys
Use provider-managed keys for most low-to-medium risk workloads where speed, cost and simplicity matter more than granular control. Prefer customer-managed keys and BYOK when dealing with sensitive data, strict LGPD or sector regulation, cross-cloud strategies, or explicit client contracts that demand independent control over cloud encryption keys and detailed auditing. Operational summary: encryption choices in…
-

Serverless Api security: common threats, auth patterns and mitigation examples
Serverless API security in pt_BR environments depends on strong identity, least privilege, and tight observability around every function and endpoint. Focus on robust authentication and authorization, encrypted tokens with rotation, proteção contra ameaças comuns em apis rest serverless via WAF and rate‑limits, secure CI/CD, and ferramentas para segurança e monitoramento de apis serverless fully integrated….
-

Security risks in migrating on-premise workloads to cloud: It checklist
To map security risks in a migração de workloads para nuvem segurança scenario, start by classifying workloads, modeling threats on each migration path, and validating network, identity, data and operations controls. Use a structured checklist, evidences and simple tools so intermediate teams in Brazil can execute a safe, auditable migration. Primary security domains to map…
-

Cloud instance hardening guide for Aws, azure and Gcp from Ssh to keys
Por que hardening em cloud ficou tão sério depois de 2020 Se você voltar mentalmente para a era dos data centers físicos, “segurança” significava muito cabo, firewall perimetral e um rack trancado. Quando AWS e depois Azure e GCP ganharam tração, muita gente apenas “levantou e migrou” as mesmas práticas, ignorando que na nuvem tudo…
-
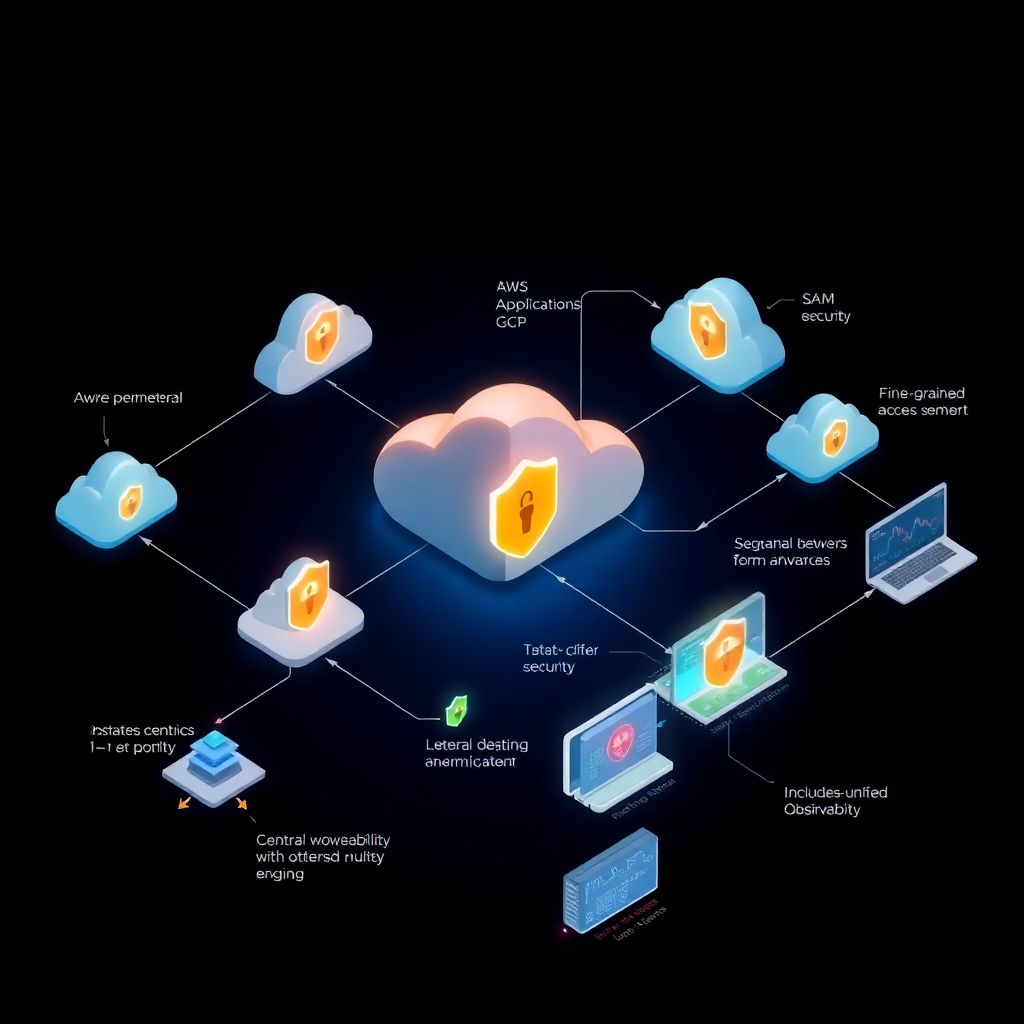
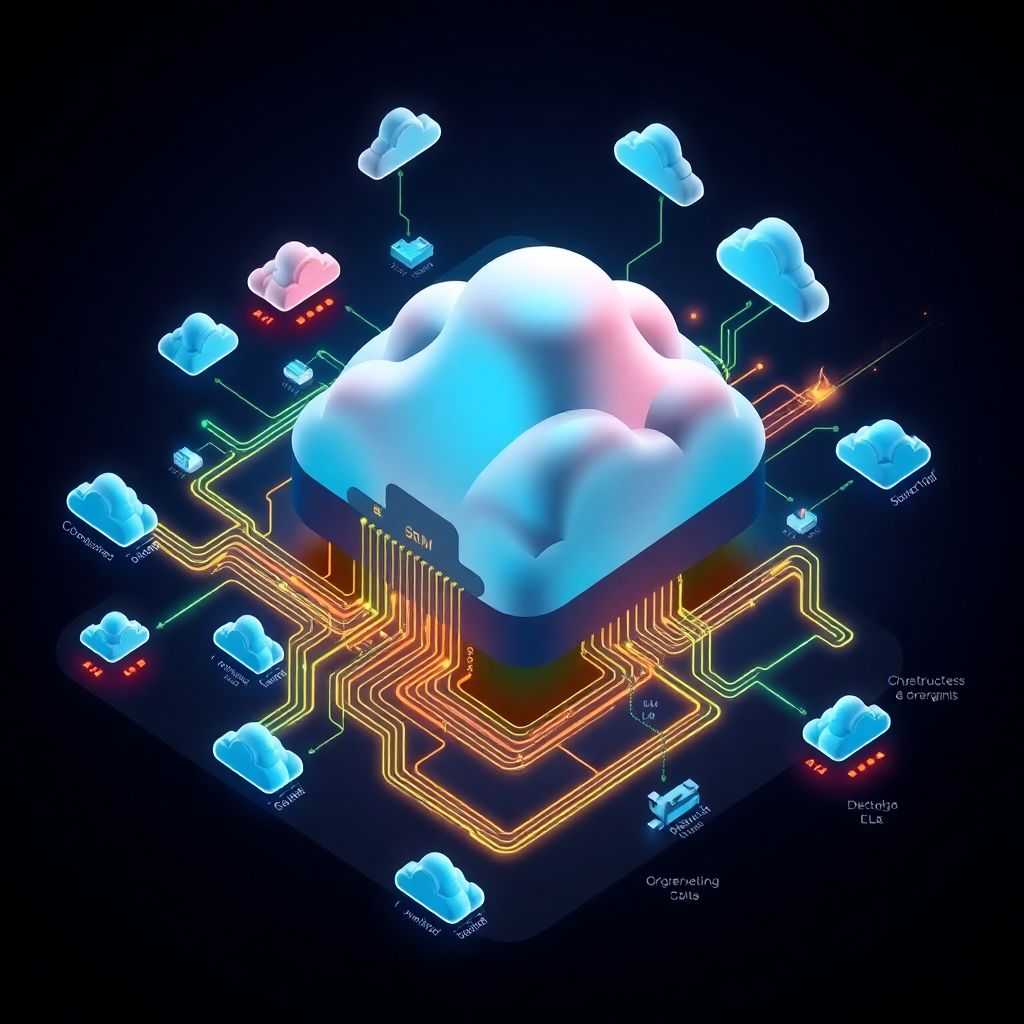
Zero trust in the cloud: implementing least-trust architecture in multi-cloud environments
Por que Zero Trust na nuvem multi cloud virou assunto obrigatório Em poucos anos, sair de um único provedor para um cenário de Zero Trust na nuvem multi cloud deixou de ser “inovação” e virou simples necessidade. Empresas misturam AWS, Azure, GCP e ainda levam em conta SaaS críticos, o que desmonta completamente a velha…
-
Continuous cloud monitoring: logging, Siem and real-time threat detection
Understanding continuous cloud monitoring Continuous monitoring in the cloud is less about shiny dashboards and more about building a nervous system for your entire infrastructure. Logs, metrics, traces and security events flow together so you can spot weird behavior before it becomes an incident. When people talk about *monitoramento contínuo na nuvem siem*, they mean…