Categoria: Revisões de Ferramentas
-

Practical guide to hardening accounts and identities in Aws, azure and google cloud
To harden cloud accounts and identities in AWS, Azure and Google Cloud, standardize identity hygiene (MFA, strong auth, no shared users), restrict and monitor privileged roles, isolate workloads by accounts/subscriptions/projects, and automate guardrails and alerting. Start small: protect break‑glass accounts, root/global admins, and service principals before tuning fine‑grained permissions. Concise hardening checklist for cloud accounts…
-

Multi-cloud security strategy for large enterprises: how to build it
A complete multi-cloud security strategy for large enterprises aligns business risk, regulatory needs and shared-responsibility models across providers. Start with risk and compliance mapping, then unify identity and access, segment networks, protect data with encryption and key management, establish centralized visibility and incident response, and enforce governance with automated, continuous compliance controls and periodic expert…
-

Cloud data encryption at rest and in transit: strategies that truly matter
Cloud encryption that actually reduces risk focuses on three things: consistent protection for data at rest and in transit, strong but practical key management, and alignment with regulations like LGPD. Start by mapping sensitive data, enforcing provider-native encryption, hardening TLS, and centralizing keys in managed KMS instead of building custom crypto. Core encryption priorities for…
-

Continuous container vulnerability monitoring: tools and best practices
Continuous container vulnerability monitoring means scanning images and running workloads on every change and regularly in production, using automated tools integrated into CI/CD and orchestrators. For teams in Brazil using Docker, Kubernetes and cloud, it reduces risk from outdated images, public base layers, and misconfigured runtimes while keeping delivery speed. Core conclusions for continuous container…
-

Cspm tools review: pros, cons and use cases for cloud security posture
CSPM (Cloud Security Posture Management) tools help continuously find misconfigurations, policy drifts, and compliance gaps across your cloud accounts. To choose the melhor solução CSPM para segurança em nuvem in a Brazilian context, compare cloud coverage, integration depth, automation, compliance support, CSPM preço licenciamento e custos de implementação, and how each tool fits your current…
-

Ai and machine learning for threat detection in cloud native environments
Using AI and machine learning for threat detection in cloud-native environments means turning logs, traces and metrics into near real-time detections of abnormal behavior. You combine telemetry from Kubernetes, serverless, PaaS and managed services with models that spot deviations, then feed alerts into response workflows already used by your security and SRE teams. Practical objectives…
-

Cloud security automation with infrastructure as code: terraform, cloudformation, bicep
To automate cloud security with Terraform, CloudFormation and Bicep, treat Infrastructure as Code as a security control: start from a threat model, encode guardrails as reusable modules and policies, enforce them in CI/CD, protect state and secrets, monitor for drift and non‑compliance, and use automated rollbacks for safe incident response. Practical outcomes and security priorities…
-

Backup and recovery strategies to build ransomware resilience in cloud
Use layered backups with immutability, air‑gapping and strong encryption; define RPO/RTO per business process; automate a tested recovery runbook across regions and accounts; and continuously monitor for anomalies. Combine backup em nuvem contra ransomware with strict access controls, regular restore tests and clear incident playbooks integrated with your cloud providers. Critical Backup and Recovery Concepts…
-

Cloud provider security assessment: technical due diligence checklist
To evaluate a cloud provider securely, treat it as a structured technical audit: map your data and compliance needs, run a control-by-control review, demand objective evidence, and document gaps with remediation plans. This checklist is tailored to due diligence for Brazilian companies and helps a provedor de nuvem seguro avaliação go beyond marketing claims. Essential…
-
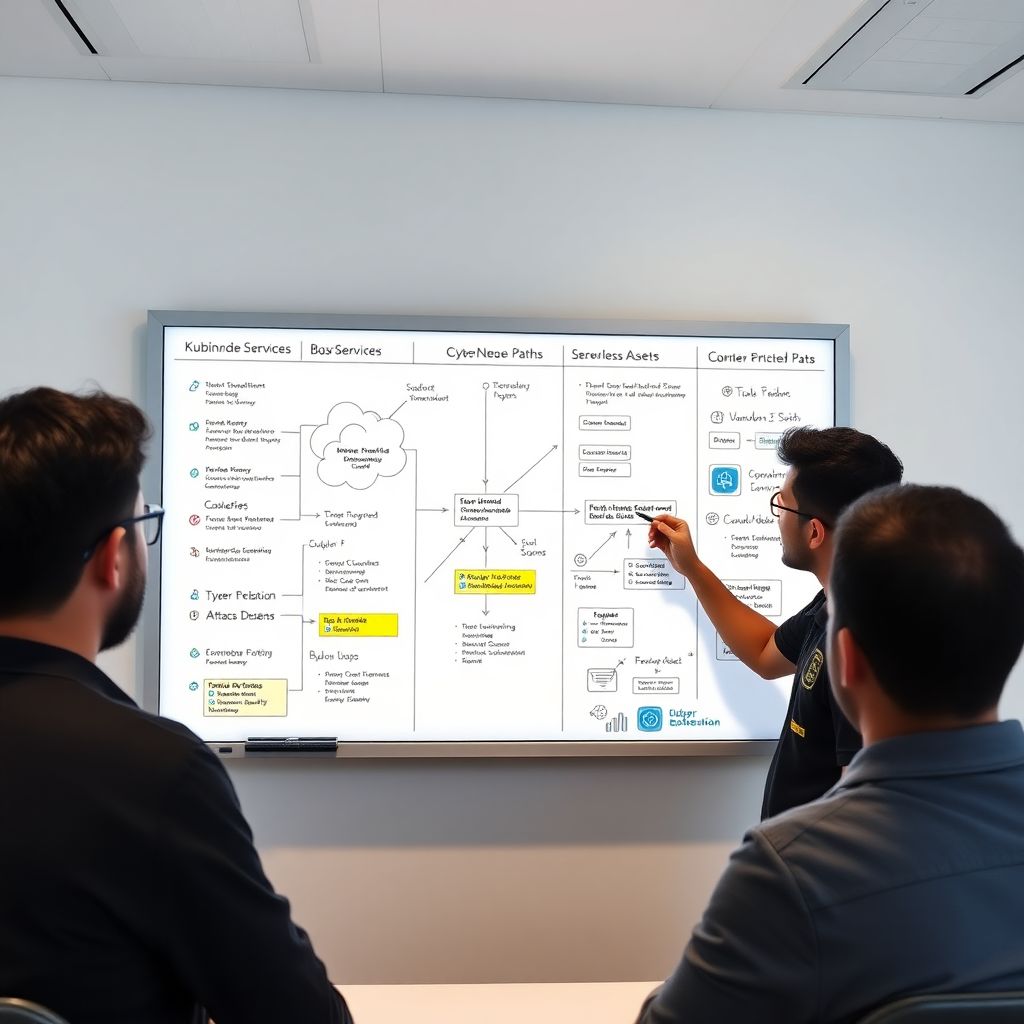
Risk-driven threat modeling for cloud-native architectures: a step-by-step guide
Cloud-native threat modeling is a structured way to map your Kubernetes, microservices and serverless assets, identify how data really flows, uncover attack paths, and rank risks by likelihood × impact. This guide gives a safe, concrete, risk‑oriented step‑by‑step, suitable for intermediate teams in Brazil working with modern cloud platforms. Risk-focused summary for cloud-native threat modeling…